One of the configuration settings for Unified Access Gateway is the number of virtual Network Interface Cards (NICs) to use. When you deploy Unified Access Gateway, you select a deployment configuration for your network.
You can specify one, two, or three NICS settings which are specified as onenic, twonic or threenic.
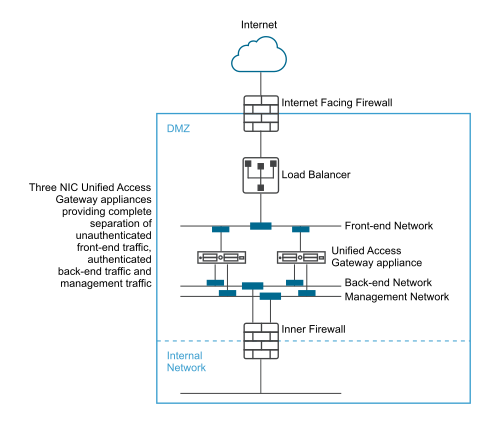
Reducing the number of open ports on each virtual LAN and separating out the different types of network traffic can significantly improve security. The benefits are mainly in terms of separating and isolating the different types of network traffic as part of a defense-in-depth DMZ security design strategy. This can be achieved either by implementing separate physical switches within the DMZ, with multiple virtual LANs within the DMZ, or as part of a full VMware NSX managed DMZ.
Typical Single NIC DMZ Deployment
The simplest deployment of Unified Access Gateway is with a single NIC (eth0) where all network traffic is combined onto a single network. Traffic from the Internet-facing firewall is directed to one of the available Unified Access Gateway appliances. Unified Access Gateway then forwards the authorized traffic through the inner firewall to resources on the internal network. Unified Access Gateway discards unauthorized traffic.

Separating Unauthenticated User Traffic from Back-End and Management Traffic
An alternative option over the single NIC deployment (eth0) is to specify two NICs. The first is still used for Internet facing unauthenticated access, but the back-end authenticated traffic and management traffic are separated onto a different network (eth1).

In a two NIC deployment, Unified Access Gateway must authorize the traffic going to the internal network through the inner firewall. Unauthorized traffic is not on this back-end network. Management traffic such as the REST API for Unified Access Gateway is only on this second network
If a device on the unauthenticated front-end network, such as the load balancer, was compromised then reconfiguring that device to bypass Unified Access Gateway is not possible in this two NIC deployment. It combines layer 4 firewall rules with layer 7 Unified Access Gateway security. Similarly, if the Internet facing firewall was misconfigured to allow TCP port 9443 through, this would still not expose the Unified Access Gateway Management REST API to Internet users. A defense-in-depth principle uses multiple levels of protection, such as knowing that a single configuration mistake or system attack does not necessarily create an overall vulnerability
In a two NIC deployment, you can put additional infrastructure systems such as DNS servers, RSA SecurID Authentication Manager servers on the back-end network within the DMZ so that these servers cannot be visible on the Internet facing network. Putting infrastructure systems within the DMZ guards against layer 2 attacks from the Internet facing LAN from a compromised front-end system and effectively reduces the overall attack surface.
Most Unified Access Gateway network traffic is the display protocols for Blast and PCoIP. With a single NIC, display protocol traffic to and from the Internet is combined with traffic to and from the back-end systems. When two or more NICs are used, the traffic is spread across front-end and back-end NICs and networks. This reduces the potential bottleneck of a single NIC and results in performance benefits.
Unified Access Gateway supports a further separation by also allowing separation of the management traffic onto a specific management LAN. HTTPS management traffic to port 9443 is then only possible from the management LAN.