JSON Web Token (JWT) is an open standard (RFC 7519) that is used for securely transmitting information between parties (a client and a server).
JWT is a set of JSON objects tied together which is used over the web or between a client and a server to validate or authorize the user. They are signed at the client-side using a private key, and the verification is done using a public key provided by an IDP. JWT validation is the authorization method used to provide access to the protected resource based on a JWT issued by an authorization server.
Avi Load Balancer validates the JWT token received from the client using a public key issued by the Authorization server.
The authorization server issues the JWT directly to client, and the client must present the JWT to the NSX Advanced Load Balancer virtual service for validation. NSX Advanced Load Balancer does not issue any JWT on its own.
JWT Validation Main Components
The followings are the main components used in a JWT validation process:
-
JSON Web Key Set (JWKS)
-
JSON Web Token (JWT)
Frequently Used Terms in JWT Validation
Term |
Description |
kid |
Identifier of the static key used to sign the JWT. |
algo |
Algorithm used to sign the key. |
iss |
Authorization server that issued the JWT. |
aud |
Recipients that the JWT is intended for (Avi Load Balancer virtual service). |
sub |
Identifies the principal that is subject of the JWT. |
exp |
The expiration time of the token in seconds. |
nbf |
Identifies the time before which the token must not be accepted for processing. |
iat |
The issuing time of the token in seconds. |
jti |
Unique identifier of the token. |
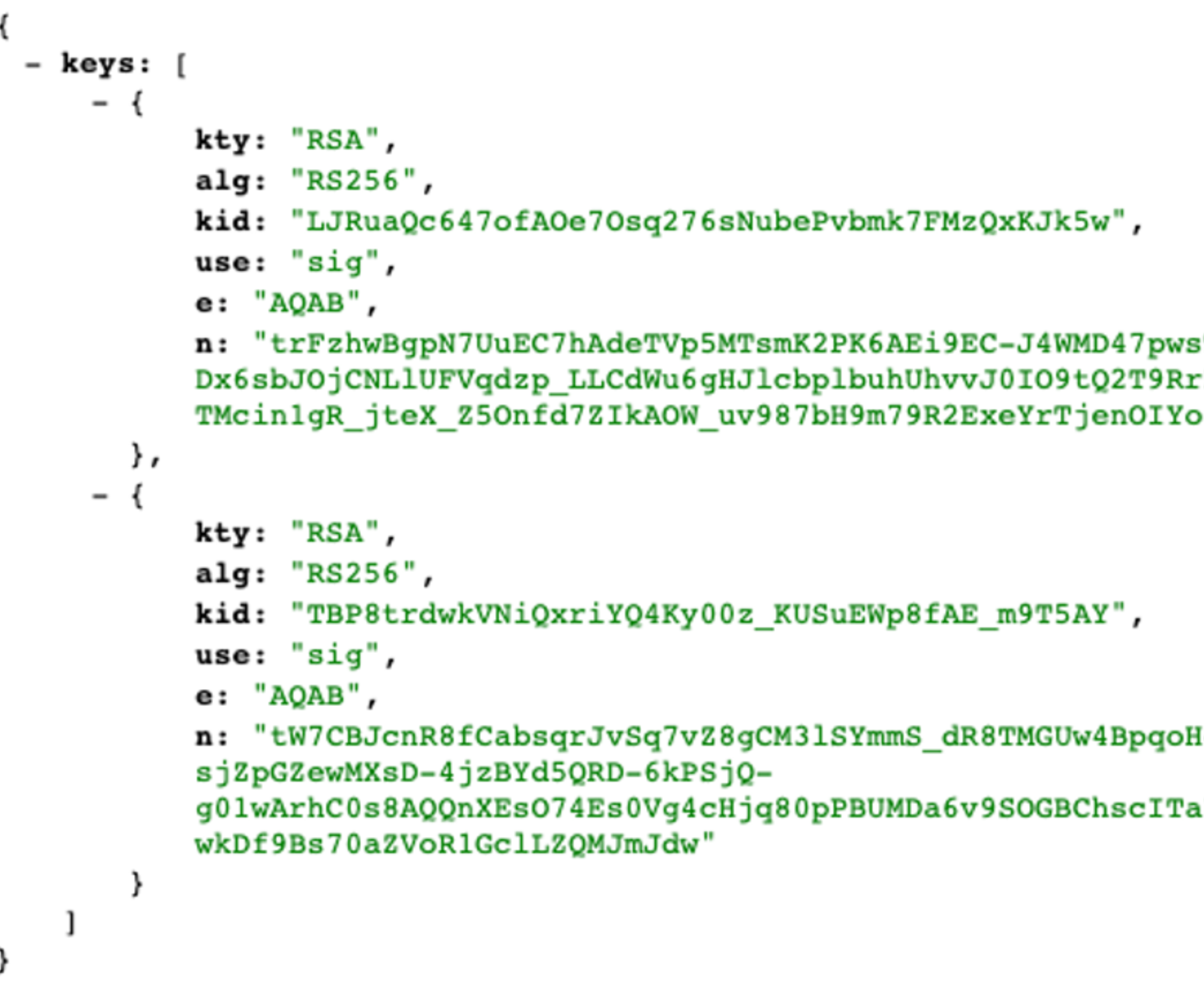
JSON Web Key Set (JWKS)
JSON Web Key Set (JWKS) is a set of public keys issued by an authorizing server. These keys are used to verify any JSON Web Token (JWT). JWKS is a JSON object that represents a set of JWKs. Each JWK is uniquely identified by a key identifier (kid). The issuer adds the kid to the JWT Header to specify the key used to sign the token. The authorization server signs JWTs, and publishes the public signing keys in a JWKS (JSON Web Key Set).
JSON Web Token
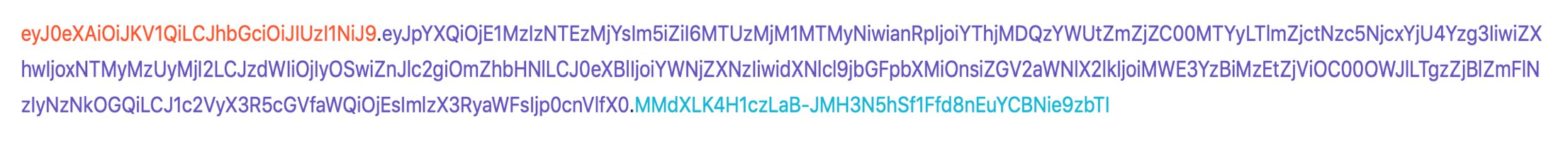
In the compact form, JSON Web Tokens (JWT) consist of the following components separated by dots (.):
-
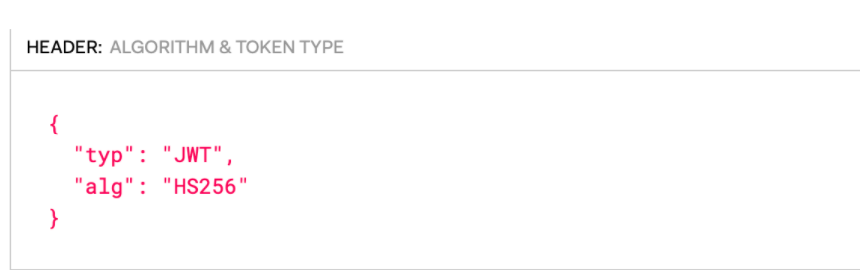
Header: The header consists of the following:-
Type of the token, which is JWT.
-
Signing algorithm which can be HMAC, SHA256, or RSA. The following is an example of a JWT header.
-
-
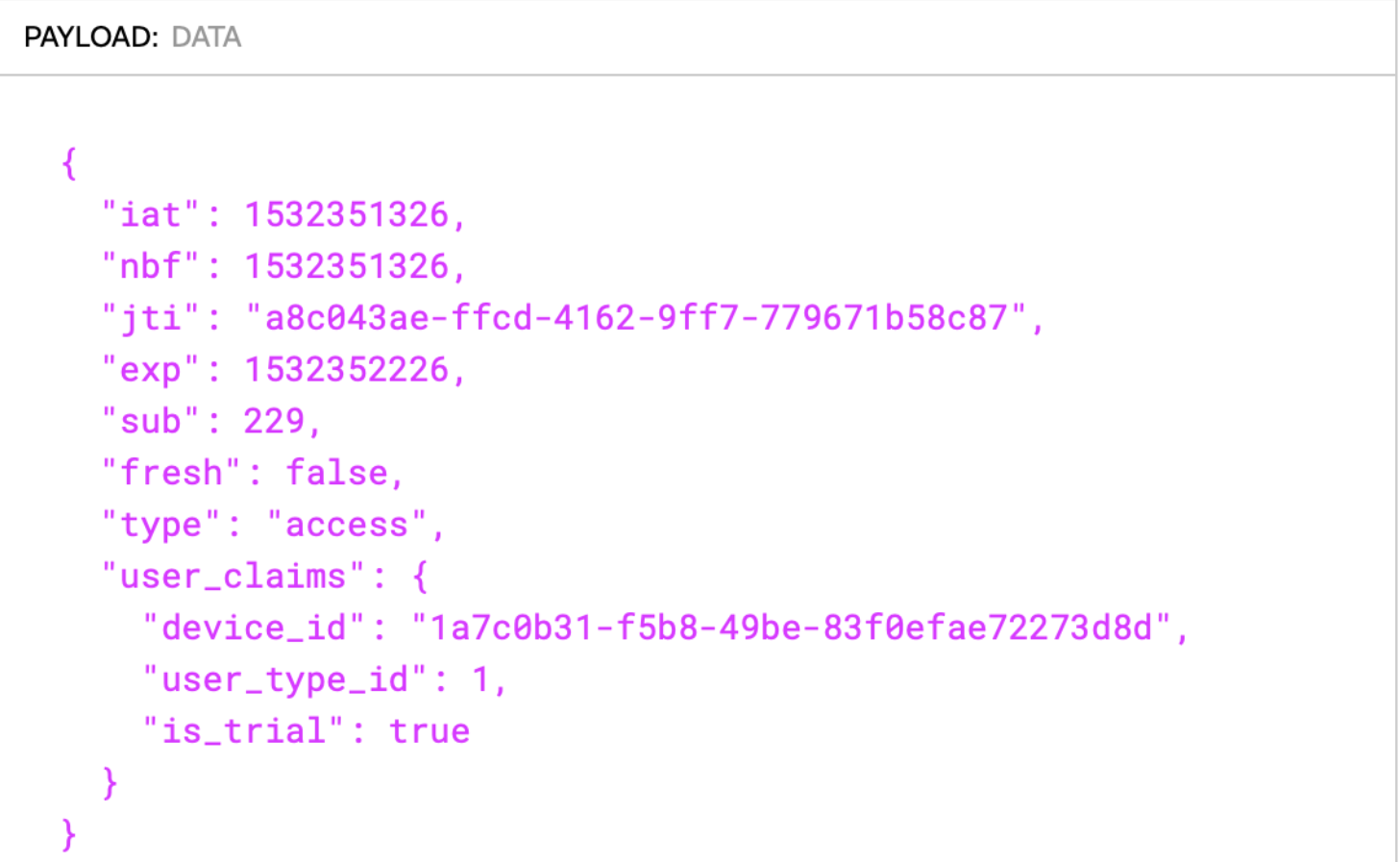
Payload: JWT Payload consists of information about the source or the client.JWT Payload contains the claims set. Claims are statements about an entity (of user) and additional data. Claims are of three types: Registered, Public, and Private.-
Registered Claims: These are the Claims that are registered in the IANA “JSON Web Token Claims” registry. For more information, refer to IANA Registered claims: https://www.iana.org/assignments/jwt/jwt.xhtml#claims
-
iss: Identifies the principal that issued the JWT
-
aud: Identifies the recipients that the JWT is intended for
-
sub: Identifies the principal that is the subject of the JWT
-
exp: The expiration time of the token in seconds since January 1, 1970 UTC (Unix time)
-
nbf: Identifies the time (a timestamp in seconds since January 1, 1970 UTC) before which the token must not be accepted for processing. (Unix time)
-
iat: The issuing time of the token in seconds since January 1, 1970 UTC (Unix time)
-
jti: Unique identifier of the Token
-
-
The following is a sample payload for a JWT.
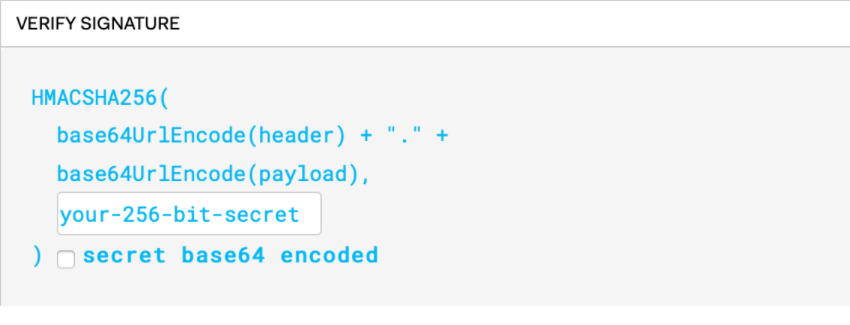
Signature: The signature is used to check the message or the request from the user which is not tampered.
A sample JSON token is shown below (when the above components are put together, but separated by a dot (.).