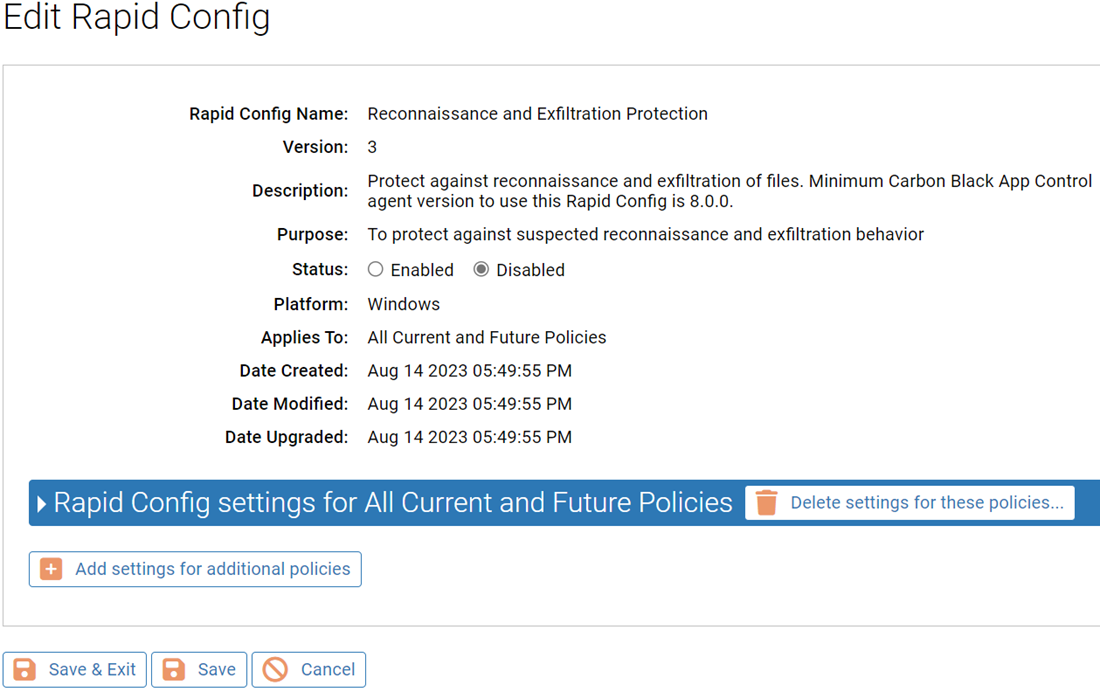
Purpose: To protect against suspected reconnaissance and exfiltration behavior.
Description: Protect against reconnaissance and exfiltration of files.
| Enabled by Default: | No |
| Platform: | Windows |
| Minimum Agent Version Required: | 8.0.0 |
Adversaries may leverage Exchange PowerShell cmdlets and commands to access, read, and/or exfiltrate sensitive information, such as emails. This rapid config will focus on those behaviors, starting with rules targeting Exchange recon, discovery, and exfiltration, as observed in Sunburst post-exploitation behaviors. An adversary may attempt to enumerate users and roles on Exchange servers to assess permissions, query configured Virtual Directory information, exfiltrate mailboxes via mailbox exports and archiving tools.
How can Carbon Black App Control help?
The Reconnaissance and Exfiltration Rapid Config can be enabled to report or block zip tool command lines that can be used for exfiltration. You can also leverage this Rapid Config to monitor suspicious command lines that focus on the reconnaissance, discovery, exfiltration, and cleanup associated with Exchange PowerShell cmdlets. This rapid config will be updated as tactics emerge and evolve.
Rapid Config Settings
As with most rapid configs, you can:
-
Enable or disable the rapid config.
-
Specify what policies the rapid config applies to.
In addition, you can choose to Do Nothing, Report, or Block the specific items or behaviors.
For each of the following sections, specify what action you require.
Suspicious Microsoft Exchange Reconnaissance and Exfiltration Command Lines
This groups protects against specific techniques used in affiliation with MS exchange reconnaissance and exfiltration. These techniques were seen in the SolarWinds breach. When enabled, this rule reports or blocks the use of common zipping tools such as 7z.exe, WinRar, and PowerShell in relation to .ost or .pst files, which could indicate archiving email files for exfiltration.
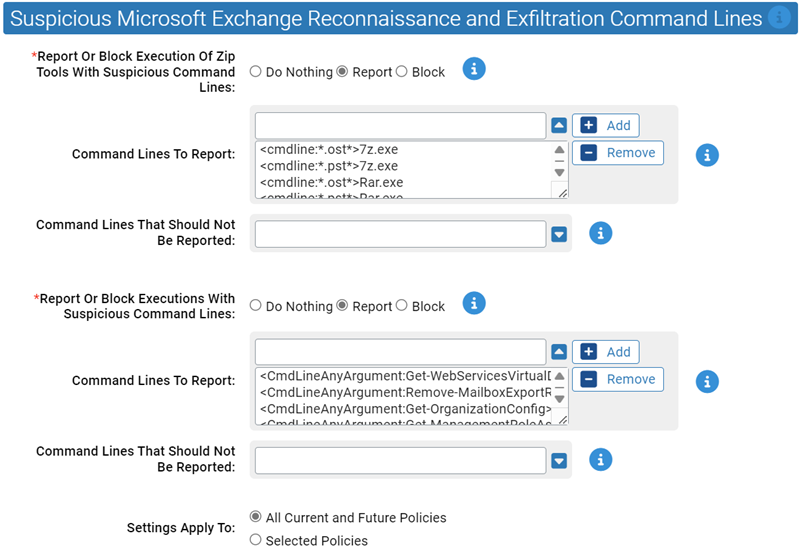
- Report Or Block Execution Of Zip Tools With Suspicious Command Lines:
- Should execution of zip tools with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Command Lines To Report:
- Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the following are listed:
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
- *Report Or Block Executions With Suspicious Command Lines:
- Should execution of these suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Command Lines To Report:
- Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the following are listed:
- Command Lines That Should Not Be Reported:
- Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list.