Purpose: To look for suspicious behavior based on unusual command lines.
Description: Reports or prevents behavior by common applications that is suspicious based on command line.
| Enabled by Default: | No |
| Platform: | Windows |
| Minimum Agent Version Required: | 8.0.0 |
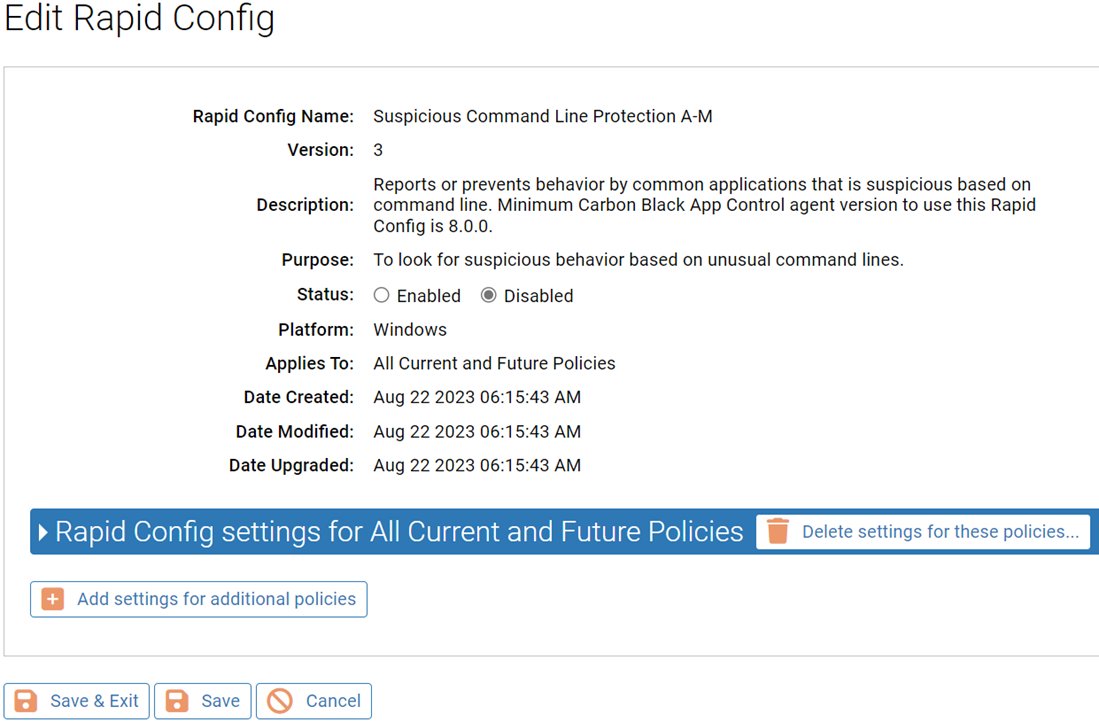
Rapid Config Settings
As with most rapid configs, you can:
-
Enable or disable the rapid config.
-
Specify what policies the rapid config applies to.
In addition, you can choose to Do Nothing, Report, or Block the specific items or behaviors.
For each of the following sections, specify what action you require.
Atbroker.exe
Use this group to specify how to handle suspicious Atbroker command lines. Atbroker is part of the Windows Assistive Technology Manager.
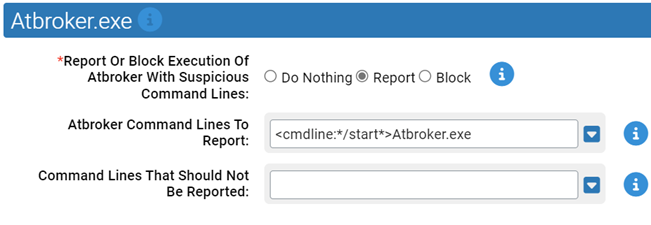
- Report Or Block Execution Of Atbroker With Suspicious Command Lines:
- Should execution of Atbroker with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Atbroker Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- <cmdline:*/start*>Atbroker.exe
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Bitsadmin.exe
Use this group to specify how to handle suspicious Bitsadmin command lines. Bitsadmin is part of the Background Intelligent Transfer Service
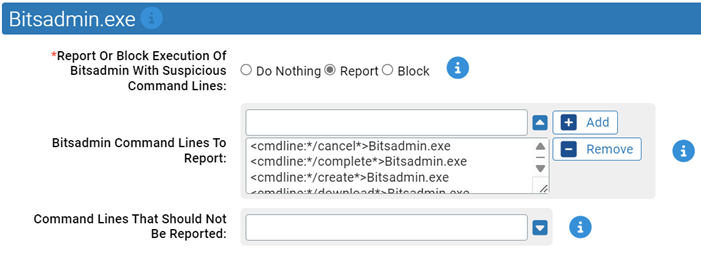
- *Report Or Block Execution Of Bitsadmin With Suspicious Command Lines:
- Should execution of Bitsadmin with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Bitsadmin Command Lines To Report:
- Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list.
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Control.exe
Use this group to specify how to handle suspicious Control command lines. Control.exe runs the Control Panel application.

- *Report Or Block Execution Of Control With Suspicious Command Lines:
- Should execution of Control with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Control Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- <cmdline:*.cpl*>Control.exe
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Cscript.exe
Use this group to specify how to handle suspicious Cscript command lines. Cscript is the Windows Script Host.
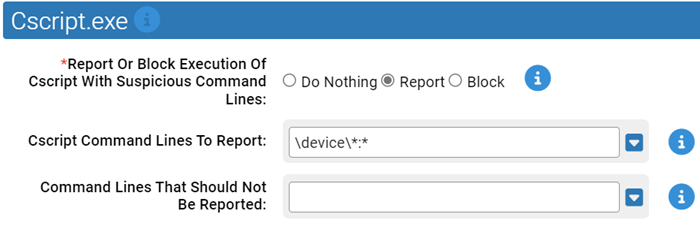
- *Report Or Block Execution Of Cscript With Suspicious Command Lines:
- Should execution of Cscript with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Cscript Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- \device\*:*
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Dnscmd.exe
Use this group to specify how to handle suspicious Dnscmd command lines. Dnscmd is a command line tool for managing DNS servers
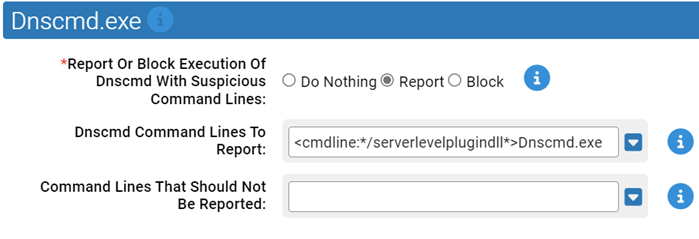
- *Report Or Block Execution Of Dnscmd With Suspicious Command Lines:
- Should execution of Dnscmd with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Dnscmd Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- <cmdline:*/serverlevelplugindll*>Dnscmd.exe
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Mavinject.exe
Use this group to specify how to handle suspicious Mavinject command lines. Mavinject is part of Microsoft Application Virtualization.
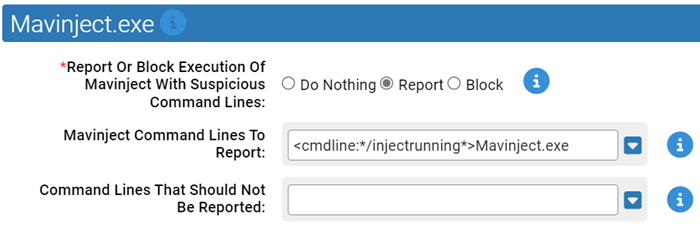
- *Report Or Block Execution Of Mavinject With Suspicious Command Lines:
- Should execution of Mavinject with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- Mavinject Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- <cmdline:*/injectrunning*>Mavinject.exe
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.
Msbuild.exe
Use this group to specify how to handle suspicious Msbuild command lines. Msbuild is the Microsoft Build Engine.
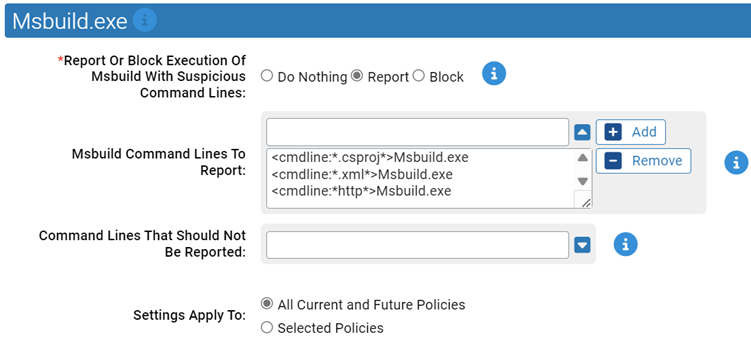
- *Report Or Block Execution Of MSbuild With Suspicious Command Lines:
- Should execution of MSbuild with suspicious command lines be reported or blocked? You should validate that legitimate execution is not blocked before enabling blocking.
- MSbuild Command Lines To Report:
-
Carbon Black App Control will report or block execution of the specified command lines. You can add or remove items from this list. By default, the list includes:
- <cmdline:*.csproj*>Msbuild.exe
- <cmdline:*.xml*>Msbuild.exe
- <cmdline:*http*>Msbuild.exe
- Command Lines That Should Not Be Reported:
- Execution of command lines specified here will not be reported or blocked.