The Carbon Black App Control console can be integrated with identity providers (IdPs) that use the Security Assertion Markup Language (SAML). This allows you to require two-factor authentication (2FA) for logging in to the Carbon Black App Control console, for compliance purposes or to meet your own best practice standards.
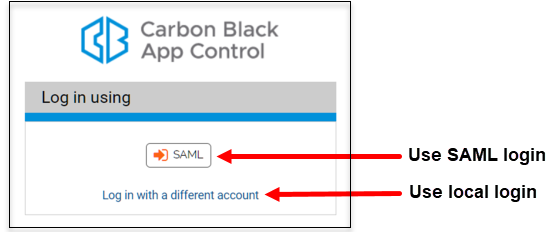
Once you save a properly configured IdP in App Control, you will be able to use SAML to log in to an existing Carbon Black App Control account. A new button with your identity provider name appears on the Carbon Black App Control login page.
When a user clicks the button, they are directed to the login page of the identity provider. If they provide their correct credentials in the IdP, they are logged into the Carbon Black App Control Console as the user whose email address matches the one for the IdP account used.
When SAML is enabled, you can configure some user roles to allow local logins. Users that have one of these roles have the option of clicking Log in with a different account and entering their Carbon Black App Control credentials to access the console. You can enable local logins in either the System Configuration page for SAML Logins or in the Permissions table for a specific role.

A user who attempts a local login without having a user role that allows this will see a login error that requests a valid user name and password. The user can click the Log in with SAML button to go to their IdP for authentication.
- The IdP account you log in with must have the same email address as a user in App Control, provided either through the IdP NameID attribute or an attribute named EmailAddress (always used if provided). The identities are not matched by name.
- If the email address for the IdP account a user logs in with does not match the email address of any Carbon Black App Control user, the login fails.