This topic describes the authentication events that Carbon Black Cloud collects and reports.
| Windows Event ID | Description |
|---|---|
| 4624 | An account was successfully logged on |
| 4625 | An account failed to log on |
| 4634 | The account was logged off |
| 4647 | User initiated logoff |
| 4672 | Special privileges assigned to new logon (administrator equivalent) |
| 4740 | A user account was locked out |
| Logon session detected |
For example:
Logon session detected events occur when:
- The sensor was upgraded to a version that supports the Auth Events feature after the logon event occurred, but the sensor still detects the existence of an active logon session.
- Collection of Auth Events was enabled after the logon event occurred, but the sensor still detects the existence of an active logon session.
Logon session detected events do not have event IDs because the collection of authentication events was inactive when the authentication event occurred on the asset.
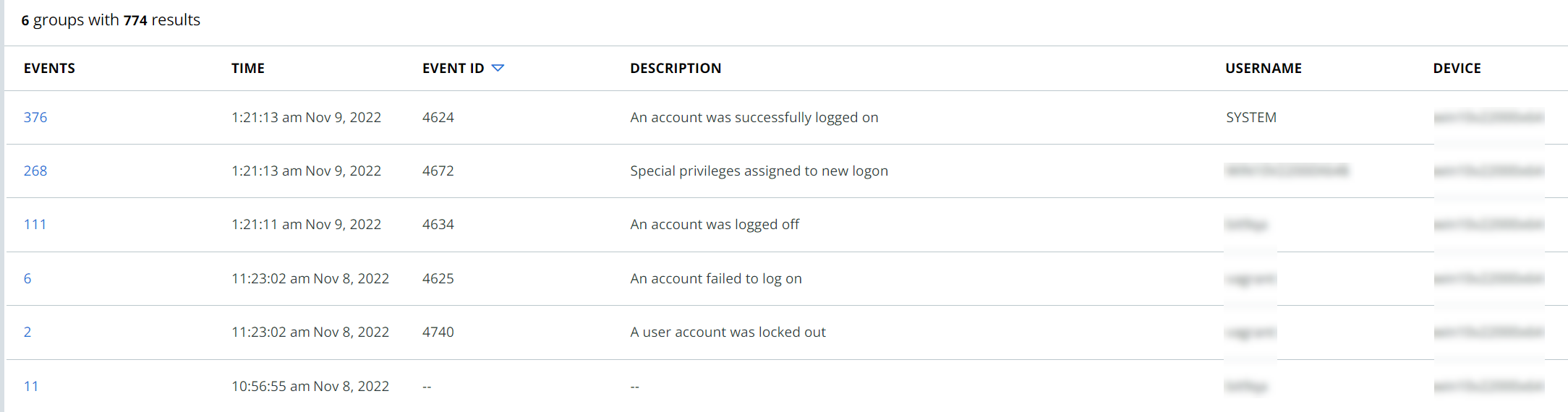
The Auth Events tab introduces a Group by feature, which allows you to group authentication events by one or more shared attributes.
You can group authentication events by:
- Windows Event ID
- Username
- Device
- Remote IP
- Time (1 minute 10 minutes, 1 hour, 1 day)
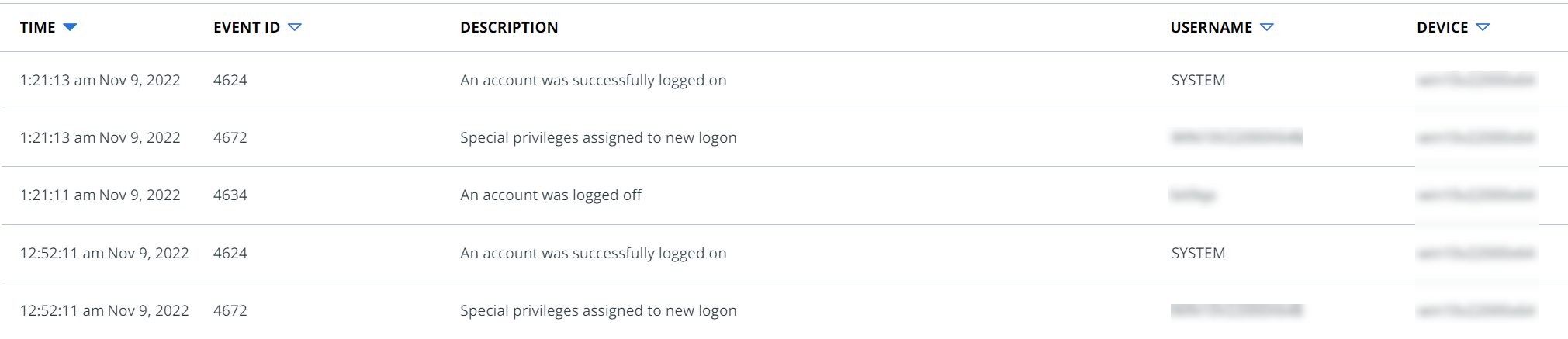
For example, to group all events that have the same Windows Event ID, select Windows Event ID in the Group by dropdown menu. The resulting table lists the number of events per grouping by Windows Event ID. You can click that number to expand the group to view all events (within the 10,000 results limit) for that particular Windows Event ID that is within the selected time range and/or number of results criteria.
To group events that have the same Windows Event ID that occurred within the same 1 hour periods, select Windows Event ID and 1 hour in the Group by dropdown menu.
Multiple Group by attributes can be applied to the authentication event results at a time. The order in which the Group by attributes are selected does not affect how the results are grouped or displayed. The application of Group by attributes is not sequential.