Let’s Encrypt is a free, automated (automates both issuing and renewing the certificate) and open certificate authority. The following section describes integration of Let's Encrypt Certificate Authority with NSX Advanced Load Balancer.
SSL/TLS protocol helps keeping an internet connection secure and safeguard any sensitive data sent between two machines, systems or devices, preventing intruders from reading, and modifying any information transferred between two machines, systems or devices. Though SSL/TLS certificate ensures secure, encrypted connections between systems, following are some challenges around it.
Manually getting a certificate.
The cost associated with a certificate signed by CA.
Let’s Encrypt resolves the above challenges. For more information, see Let’s Encrypt.
Working with Let’s Encrypt
Before issuing a certificate, Let’s Encrypt servers validate that the requester controls the domain names in that certificate using challenges as defined by the ACME standard. Let’s Encrypt uses the ACME protocol to verify that you control a given domain name and to issue you a certificate. There are different ways that the agent or client can prove control of the domain.
Provisioning a DNS record under the domain (as per CSR’s common name).
Provisioning an HTTP resource under a well-known URI.
The NSX Advanced Load Balancer supports HTTP-01 challenge for domain validation.
HTTP-01 Challenge
Let’s Encrypt gives a token to the ACME client that puts a file on the web server at http://<YOUR_DOMAIN>/well-known/acme-challenge/<TOKEN>. This file contains the token and a thumbprint of account key.
Once the ACME client tells Let’s Encrypt that the file is ready, Let’s Encrypt tries retrieving it (potentially multiple times from multiple vantage points).
If validation checks get the right responses from the web server, the validation is considered successful, and a certificate is issued.
As Let’s Encrypt CA communicates on port 80 for HTTP-01 challenge, port 80 must be opened on the firewall and Let’s Encrypt CA must be able to reach user network (network where the NSX Advanced Load Balancer System is deployed). Let’s Encrypt CA connects through public network to user’s NSX Advanced Load Balancer System on port 80.
The script automatically creates a virtual service on port 80 for the respective virtual service listening on port 443/custom SSL Port, only if there is no virtual service already listening on port 80.
For more information on domain validation, see the following links.
Configuring Let’s Encrypt
Following is the configuration summary for the Let’s Encrypt integration with the NSX Advanced Load Balancer.
Get the script which would assist in getting and renewing the certificate.
Add the script as controller script on the NSX Advanced Load Balancer System.
Add user account with customer (limited access only).
Create certificate management profile on NSX Advanced Load Balancer System.
Add virtual service on NSX Advanced Load Balancer System.
Make sure that the FQDN resolves to public IP and port 80 is open at Firewall.
Create CSR and select the configured certificate management profile.
Review the list of certificates. Let’s Encrypt CA would push signed certificate.
Associate the certificate to the configured virtual service.
Configuring the NSX Advanced Load Balancer System
To configure Let’s Encrypt for NSX Advanced Load Balancer.
Download the script available at letsencrypt_mgmt_profile. To download the file, click Raw option. Copy the code available.
In the NSX Advanced Load Balancer, navigate to and click Create.
Add a meaningful name and paste the code copied in step 1 in the Import or Paste Control Script field. Save the configuration.
Configure a custom role by navigating to . Ensure that read and write access is enabled for Virtual Service, Application Profile, SSL/TLS Certificates and Certificate Management Profile, for this role.

Add a user by navigating to , enter all the required details and select the configured custom role.

Navigate to and click Create.
Enter a meaningful name, select the configured control script and enable custom parameters, add custom parameters as shown in the following example:

Note:It is recommended not to use admin account. Always add a user account which has custom role (with limited access).
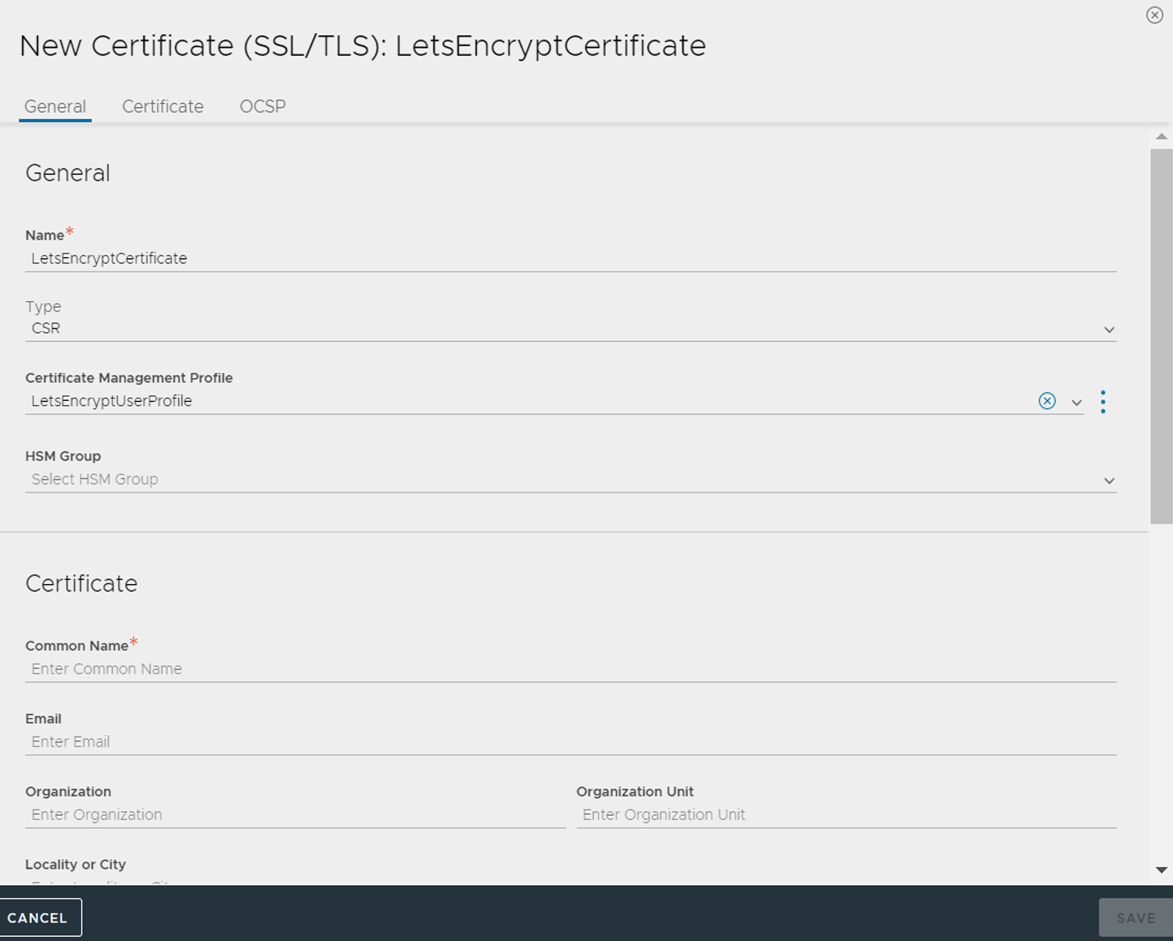
Navigate to , click Create and select Application Certificate.
Enter meaningful name, common name, select the configured certificate management profile, add all relevant details and save the configuration.
Ensure that a virtual service is configured with the Application Domain Name as Common Name (CN) of certificate. CN of certificate must match with the Application Domain Name of the virtual service. FQDN (CN of certificate or Application Domain Name of virtual service must resolve to IP address and the domain must be reachable).
After few minutes, review the list of the certificates. You can see the certificate pushed by Let’s Encrypt CA. Associate the certificate to the configured virtual service.
Logs
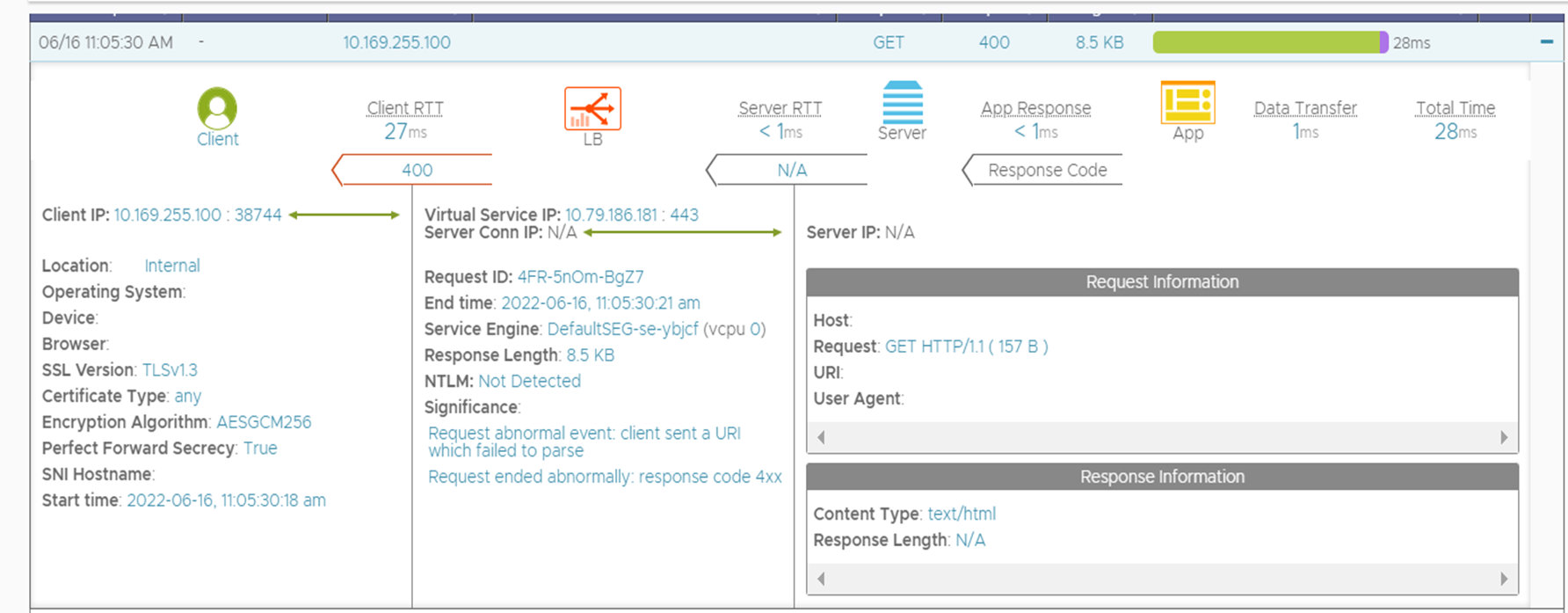
To view the logs, enable non-significant logs for the configured virtual service and generate the certificate. Following is an example of the log.
Automation of certificate renewal
Controllerproperties has the configuration for the ssl_certificate_expiry_warning_days. In the default configuration, the value for ssl_certificate_expiry_warning_days is 30 days, 7 days, and 1 day. This setting can be modified if required. When certificate renewal is required (based on configured settings), the script gets activated and automatically takes care of certificate renewal.
Let’s Encrypt CA imposes a rate limit. So ensure that the renewal of the certificate does not hit the rate limit.
Additional Information
For more information on rate limit, see Rate Limits.
For more information on SSL/TLS Certificate, see SSL Certificates.