Configure security policies in the Netskope security cloud to validate connectivity between the Netskope and VMware SD-WAN traffic.
The following steps depict an example of blocking gambling related websites by configuring the security policies.
Note: You can skip this procedure, if production traffic is already flowing in the portals.
Prerequisites
Ensure that the IPSEC tunnels to both the Primary and Secondary Netskope POPs are connected successfully.
Procedure
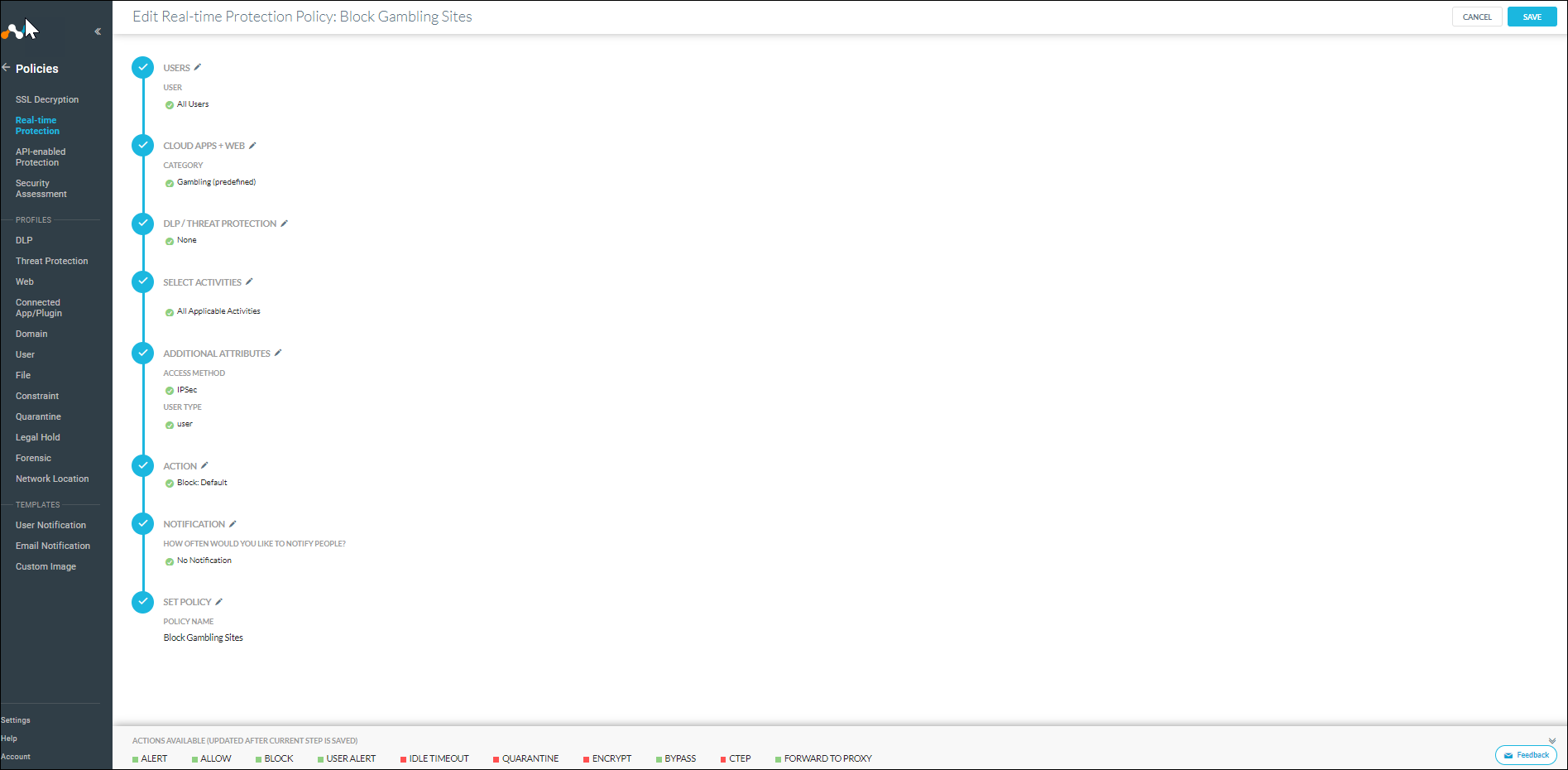
- Login to the Netskope next-generation secure web gateway and navigate to . Configure a policy to block all gambling related web sites, as shown in the following image.
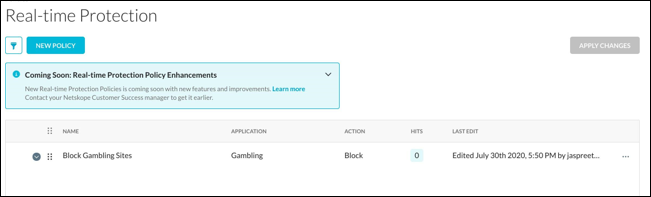
- Confirm that the policy has been applied and note the number of current hits or matches, against the policy. In the following example, there are 0 Hits.
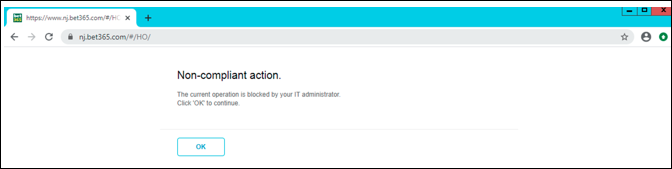
- In the Edge, login to any Windows based client on the LAN and try to browse any gambling based website.
Notice that the action is blocked as per the policy configured in the Netskope portal.
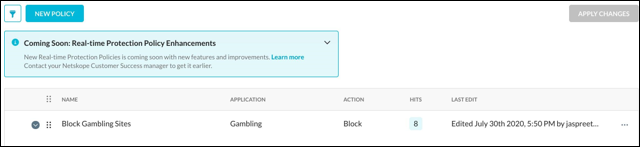
- In the Netskope next-generation secure web gateway, navigate to to check the hit count for the Block Gambling Sites policy.
Notice that the hit count has incremented, which indicates that the traffic is passing through the Netskope cloud security platform.
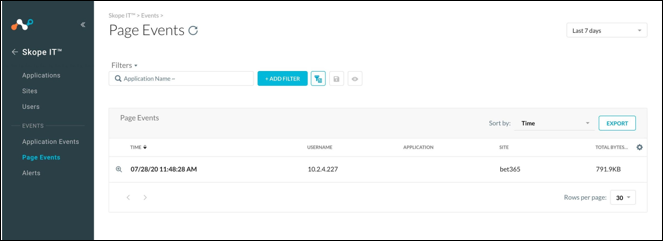
- Navigate to Skope IT portal and confirm the matches in the Page Events screen.
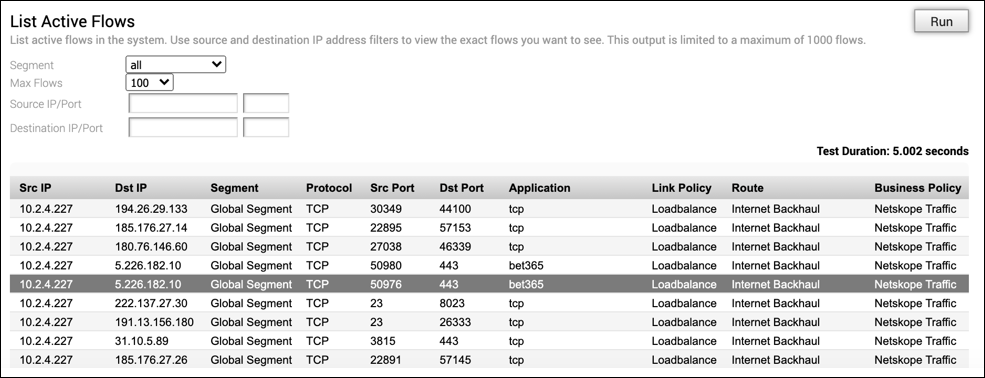
- Check the active flow in VMware SD-WAN Orchestrator portal to verify that the traffic hit the Non SD-WAN Destination via Gateway, for ultimate delivery to the Netskope security cloud.
- In the Enterprise portal, click .
- The Remote Diagnostics page displays all the active Edges.
- Select the Edge configured with Non SD-WAN Destination via Gateway. The Edge enters live mode and displays all the possible Remote Diagnostics tests than you can run on the Edge.
- Scroll down to the List Active Flows section and click Run to view the traffic flow.
Notice that the traffic destined to the URL http://www.bet365.com is transited through the Internet Backhaul route and then to the Netskope security cloud.