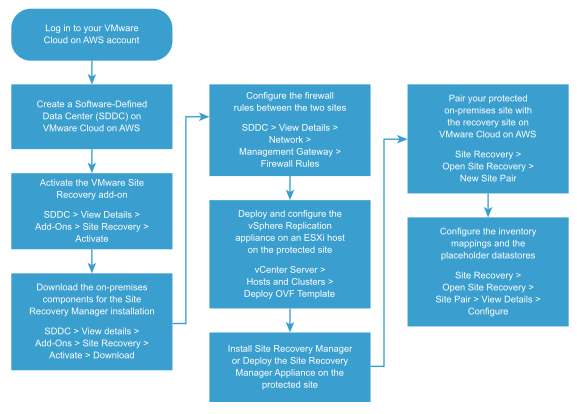
To start using VMware Site Recovery, you must perform several procedures in a predefined order.
This overview of the workflow that you must follow to set up an on-premises protected site and pair it up with a recovery site on VMware Cloud on AWS can help you through the process of protecting your data and applications.
The process includes activating the VMware Site Recovery service, downloading the components for the on-premises installation, configuring the firewall rules, installing and configuring vSphere Replication and Site Recovery Manager, and pairing the protected and the recovery sites.
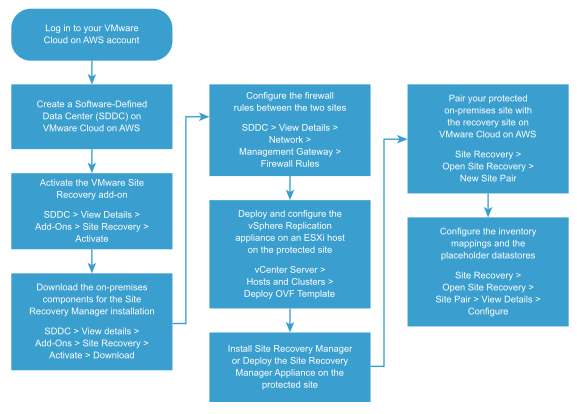
Procedure
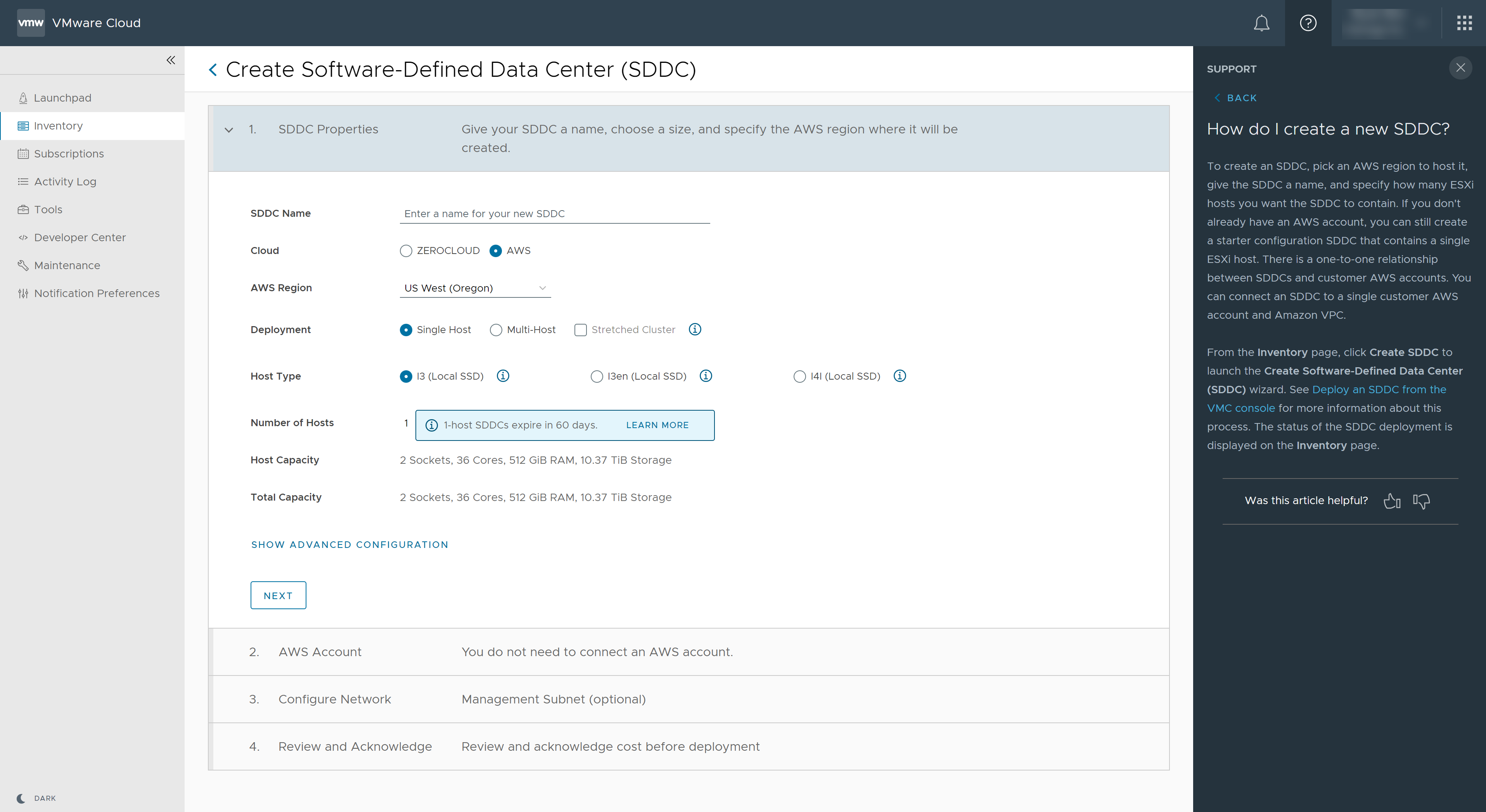
- Create an SDDC on VMware Cloud on AWS.
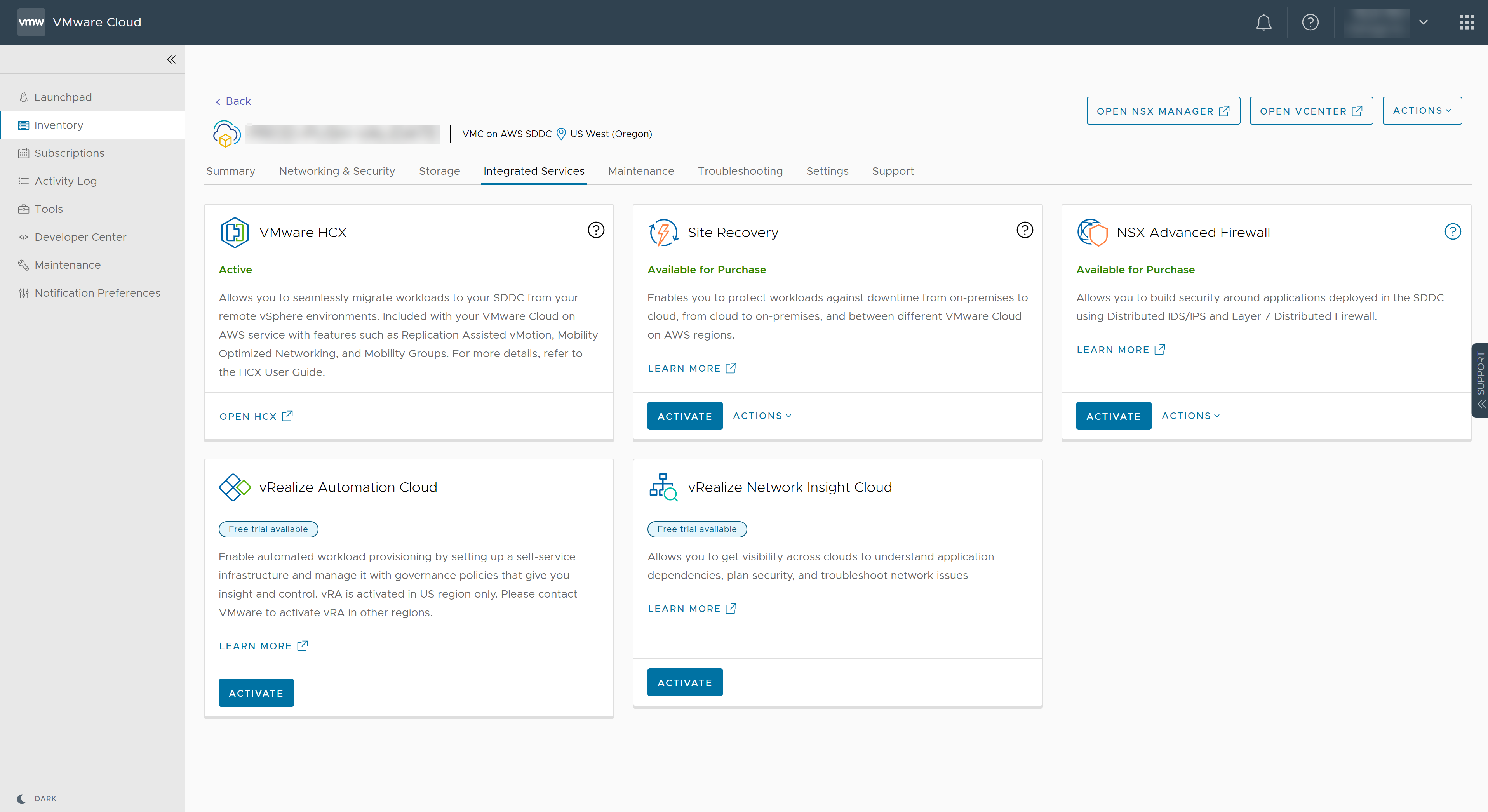
- Activate the VMware Site Recovery integrated service.
- Download the on-premises components for the Site Recovery Manager installation.
- Download vSphere Replication.
- Download Site Recovery Manager.
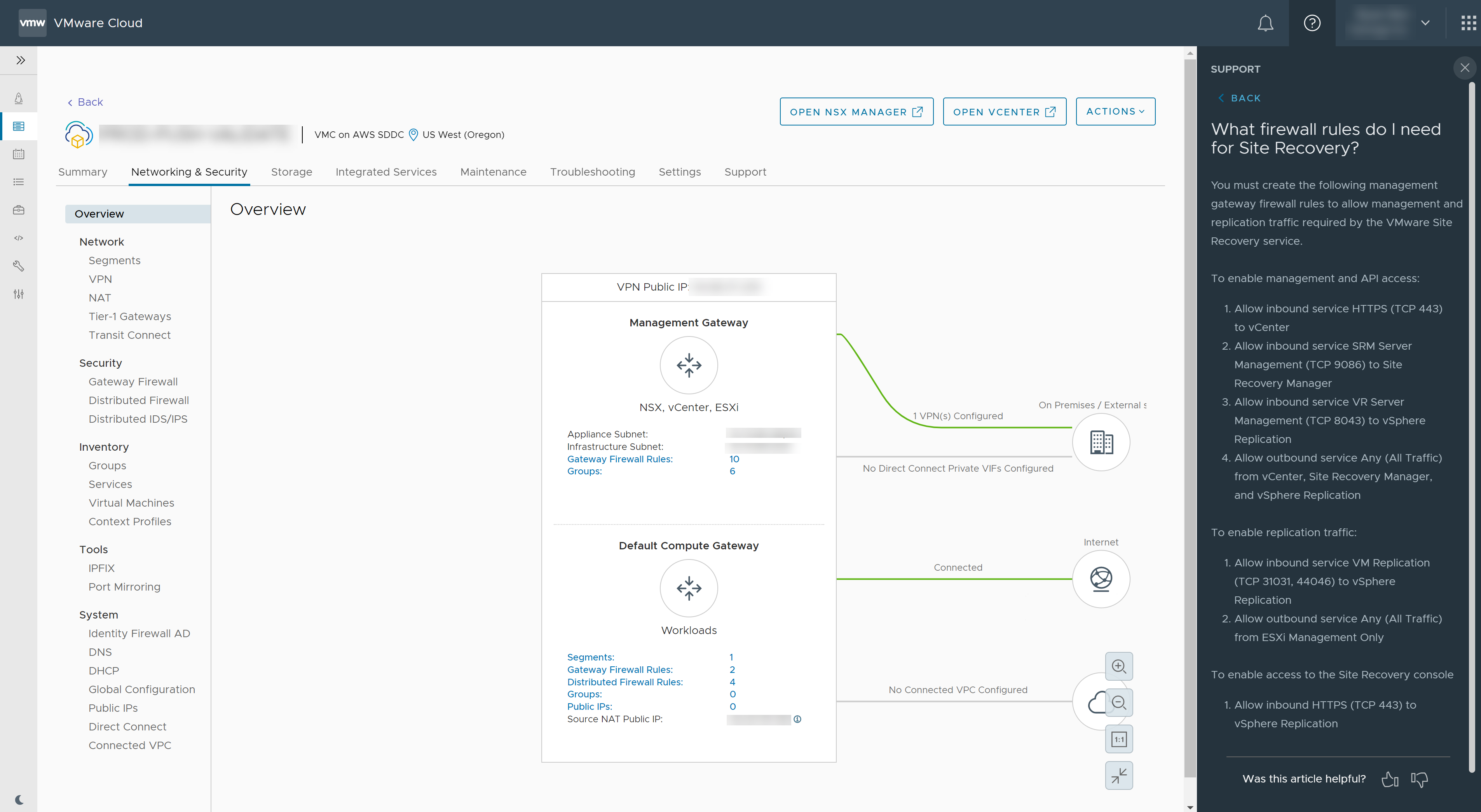
- Configure the firewall rules between the two sites.
- Deploy the vSphere Replication appliance on an ESXi host on the protected site.
- Configure vSphere Replication by using the virtual appliance management interface (VAMI).
The URL for the VAMI of the
vSphere Replication management server is https://
vr-appliance-address:5480.
- Install Site Recovery Manager on the protected site. You can either install Site Recovery Manager on a Windows server, or deploy and configure the Site Recovery Manager Appliance, a virtual Linux machine that is optimized to run Site Recovery Manager and its associated services.
To ensure optimal performance, use the embedded vPostgreSQL database for your on-premises installation.
- Pair your protected on-premises site with the recovery site on VMware Cloud on AWS.
You can pair the two sites by logging in to the
vSphere Web Client and opening the
Site Recovery user interface at either the protected or the recovery site.
- Use the Site Recovery user interface to configure the inventory mappings and the placeholder datastores.
What to do next
Start using
VMware Site Recovery:
- Configure replication on the virtual machines to protect.
- Create and manage protection groups.
- Create, test, and run recovery plans.