Install Tanzu Application Platform in your air-gapped environment
This topic tells you how to install Tanzu Application Platform (commonly known as TAP) on your Kubernetes cluster and registry that are air-gapped from external traffic.
Before installing the packages, ensure that you have completed the following tasks:
- Review the Prerequisites to ensure that you have set up everything required before beginning the installation.
- Install Tanzu CLI.
- Deploy Cluster Essentials. This step is optional if you are using VMware Tanzu Kubernetes Grid cluster.
Relocate images to a registry
To relocate images from tanzu.packages.broadcom.com registry to your air-gapped registry:
-
Retrieve your Broadcom registry API token:
-
Sign in to the Broadcom Support Portal.
-
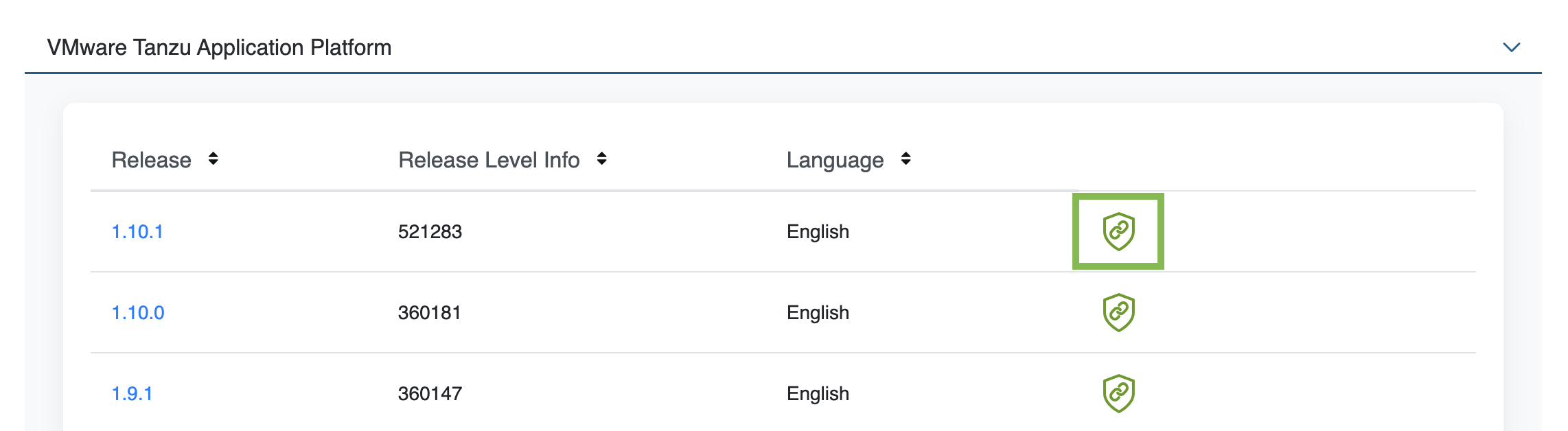
Go to Tanzu Application Platform (TAP) and expand the VMware Tanzu Application Platform dropdown.
-
Click the Token Download icon next to the Tanzu Application Platform version you want to download.
-
Follow the instructions in the dialog box. Save the token as a variable named
MY_BROADCOM_SUPPORT_ACCESS_TOKEN. For example:export MY_BROADCOM_SUPPORT_ACCESS_TOKEN=API-TOKENWhere
API-TOKENis your token from the Broadcom Support Portal.
-
-
Set up environment variables for installation use by running:
# Set tanzu.packages.broadcom.com as the source registry to copy the Tanzu Application Platform packages from. export IMGPKG_REGISTRY_HOSTNAME_0=tanzu.packages.broadcom.com export IMGPKG_REGISTRY_USERNAME_0=MY-BROADCOM-SUPPORT-USERNAME export IMGPKG_REGISTRY_PASSWORD_0=${MY_BROADCOM_SUPPORT_ACCESS_TOKEN} # The user’s registry for copying the Tanzu Application Platform package to. export IMGPKG_REGISTRY_HOSTNAME_1=MY-REGISTRY export IMGPKG_REGISTRY_USERNAME_1=MY-REGISTRY-USER export IMGPKG_REGISTRY_PASSWORD_1=MY-REGISTRY-PASSWORD # These environment variables starting with IMGPKG_* are used by the imgpkg command only. export TAP_VERSION=VERSION-NUMBER export REGISTRY_CA_PATH=PATH-TO-CA export TO_REPO=MY-REPOWhere:
MY-BROADCOM-SUPPORT-USERNAMEis the user with access to the images intanzu.packages.broadcom.com.MY-REGISTRYis your air-gapped container registry.MY-REGISTRY-USERis the user with write access toMY-REGISTRY.MY-REGISTRY-PASSWORDis the password forMY-REGISTRY-USER.VERSION-NUMBERis your Tanzu Application Platform version. For example,1.7.11.PATH-TO-CAis the path to your CA certificate.MY-REPOis your repository in the air-gapped container image registry. Examples:- Harbor has the form
MY-REGISTRY/REPO-NAME/tap-packages. - Docker Hub has the form
MY-REGISTRY/tap-packages. - Google Cloud Registry has the form
MY-REGISTRY/MY-PROJECT/REPO-NAME/tap-packages.
- Harbor has the form
-
Copy the images into a
.tarfile fromtanzu.packages.broadcom.comonto an external storage device with the Carvel tool imgpkg by running:imgpkg copy \ -b tanzu.packages.broadcom.com/tanzu-application-platform/tap-packages:$TAP_VERSION \ --to-tar tap-packages-$TAP_VERSION.tar \ --include-non-distributable-layers -
Relocate the images with the Carvel tool imgpkg by running:
imgpkg copy \ --tar tap-packages-$TAP_VERSION.tar \ --to-repo $TO_REPO \ --include-non-distributable-layers \ --registry-ca-cert-path $REGISTRY_CA_PATH
Add the Tanzu Application Platform package repository
Tanzu CLI packages are available through repositories. Adding the Tanzu Application Platform package repository makes Tanzu Application Platform and its packages available for installation.
To add the Tanzu Application Platform package repository to your cluster:
-
Create a namespace called
tap-installfor deploying any component packages by running:kubectl create ns tap-installThis namespace keeps the objects grouped together logically.
-
Create a registry secret by running:
tanzu secret registry add tap-registry \ --server $IMGPKG_REGISTRY_HOSTNAME_1 \ --username $IMGPKG_REGISTRY_USERNAME_1 \ --password $IMGPKG_REGISTRY_PASSWORD_1 \ --namespace tap-install \ --export-to-all-namespaces \ --yes -
Create a secret for accessing the user’s registry by running:
tanzu secret registry add registry-credentials \ --server $IMGPKG_REGISTRY_HOSTNAME_1 \ --username $IMGPKG_REGISTRY_USERNAME_1 \ --password $IMGPKG_REGISTRY_PASSWORD_1 \ --namespace tap-install \ --export-to-all-namespaces \ --yes -
Add the Tanzu Application Platform package repository to the cluster by running:
tanzu package repository add tanzu-tap-repository \ --url $IMGPKG_REGISTRY_HOSTNAME_1/tap-packages:$TAP_VERSION \ --namespace tap-installWhere
$TAP_VERSIONis the Tanzu Application Platform version environment variable you defined earlier. -
Get the status of the Tanzu Application Platform package repository, and ensure the status updates to
Reconcile succeededby running:tanzu package repository get tanzu-tap-repository --namespace tap-installNote
The
VERSIONandTAGnumbers differ from the earlier example if you are on Tanzu Application Platform v1.0.2 or earlier. -
List the available packages by running:
tanzu package available list --namespace tap-installFor example:
$ tanzu package available list --namespace tap-install / Retrieving available packages... NAME DISPLAY-NAME SHORT-DESCRIPTION accelerator.apps.tanzu.vmware.com Application Accelerator for VMware Tanzu Used to create new projects and configurations. api-portal.tanzu.vmware.com API portal A unified user interface for API discovery and exploration at scale. apis.apps.tanzu.vmware.com API Auto Registration for VMware Tanzu A TAP component to automatically register API exposing workloads as API entities in TAP GUI. backend.appliveview.tanzu.vmware.com Application Live View for VMware Tanzu App for monitoring and troubleshooting running apps buildservice.tanzu.vmware.com Tanzu Build Service Tanzu Build Service enables the building and automation of containerized software workflows securely and at scale. carbonblack.scanning.apps.tanzu.vmware.com VMware Carbon Black for Supply Chain Security Tools - Scan Default scan templates using VMware Carbon Black cartographer.tanzu.vmware.com Cartographer Kubernetes native Supply Chain Choreographer. cnrs.tanzu.vmware.com Cloud Native Runtimes Cloud Native Runtimes is a serverless runtime based on Knative connector.appliveview.tanzu.vmware.com Application Live View Connector for VMware Tanzu App for discovering and registering running apps controller.source.apps.tanzu.vmware.com Tanzu Source Controller Tanzu Source Controller enables workload create/update from source code. conventions.appliveview.tanzu.vmware.com Application Live View Conventions for VMware Tanzu Application Live View convention server developer-conventions.tanzu.vmware.com Tanzu App Platform Developer Conventions Developer Conventions external-secrets.apps.tanzu.vmware.com External Secrets Operator External Secrets Operator is a Kubernetes operator that integrates external secret management systems. fluxcd.source.controller.tanzu.vmware.com Flux Source Controller The source-controller is a Kubernetes operator, specialised in artifacts acquisition from external sources such as Git, Helm repositories and S3 buckets. grype.scanning.apps.tanzu.vmware.com Grype for Supply Chain Security Tools - Scan Default scan templates using Anchore Grype metadata-store.apps.tanzu.vmware.com Supply Chain Security Tools - Store Post SBoMs and query for image, package, and vulnerability metadata. namespace-provisioner.apps.tanzu.vmware.com Namespace Provisioner Automatic Provisioning of Developer Namespaces. ootb-delivery-basic.tanzu.vmware.com Tanzu App Platform Out of The Box Delivery Basic Out of The Box Delivery Basic. ootb-supply-chain-basic.tanzu.vmware.com Tanzu App Platform Out of The Box Supply Chain Basic Out of The Box Supply Chain Basic. ootb-supply-chain-testing-scanning.tanzu.vmware.com Tanzu App Platform Out of The Box Supply Chain with Testing and Scanning Out of The Box Supply Chain with Testing and Scanning. ootb-supply-chain-testing.tanzu.vmware.com Tanzu App Platform Out of The Box Supply Chain with Testing Out of The Box Supply Chain with Testing. ootb-templates.tanzu.vmware.com Tanzu App Platform Out of The Box Templates Out of The Box Templates. policy.apps.tanzu.vmware.com Supply Chain Security Tools - Policy Controller Policy Controller enables defining of a policy to restrict unsigned container images. scanning.apps.tanzu.vmware.com Supply Chain Security Tools - Scan Scan for vulnerabilities and enforce policies directly within Kubernetes native Supply Chains. service-bindings.labs.vmware.com Service Bindings for Kubernetes Service Bindings for Kubernetes implements the Service Binding Specification. services-toolkit.tanzu.vmware.com Services Toolkit The Services Toolkit enables the management, lifecycle, discoverability and connectivity of Service Resources (databases, message queues, DNS records, etc.). snyk.scanning.apps.tanzu.vmware.com Snyk for Supply Chain Security Tools - Scan Default scan templates using Snyk spring-boot-conventions.tanzu.vmware.com Tanzu Spring Boot Conventions Server Default Spring Boot convention server. sso.apps.tanzu.vmware.com AppSSO Application Single Sign-On for Tanzu tap-auth.tanzu.vmware.com Default roles for Tanzu Application Platform Default roles for Tanzu Application Platform tap-gui.tanzu.vmware.com Tanzu Developer Portal web app graphical user interface for Tanzu Application Platform tap-telemetry.tanzu.vmware.com Telemetry Collector for Tanzu Application Platform Tanzu Application Platform Telemetry tap.tanzu.vmware.com Tanzu Application Platform Package to install a set of TAP components to get you started based on your use case. tekton.tanzu.vmware.com Tekton Pipelines Tekton Pipelines is a framework for creating CI/CD systems.
Prepare Sigstore Stack for air-gapped policy controller
ImportantThis section only applies if the target environment requires support for keyless authorities in
ClusterImagePolicy. You must set thepolicy.tuf_enabledfield totruewhen installing Tanzu Application Platform. By default, keyless authorities support is deactivated.
By default, the public official Sigstore “The Update Framework (TUF) server” is used. You can use an alternative Sigstore Stack by setting policy.tuf_mirror and policy.tuf_root.
The Sigstore Stack consists of:
For an air-gapped environment, an internally accessible Sigstore Stack is required for keyless authorities.
Install your Tanzu Application Platform profile
The tap.tanzu.vmware.com package installs predefined sets of packages based on your profile settings. This is done by using the package manager installed by Tanzu Cluster Essentials.
For more information about profiles, see Components and installation profiles.
To prepare to install a profile:
-
List version information for the package by running:
tanzu package available list tap.tanzu.vmware.com --namespace tap-install -
Create a
tap-values.yamlfile by using the Full Profile sample as a guide. These samples have the minimum configuration required to deploy Tanzu Application Platform. The sample values file contains the necessary defaults for:- The meta-package, or parent Tanzu Application Platform package
- Subordinate packages, or individual child packages
Keep the values file for future configuration use.
Full Profile
To install Tanzu Application Platform with Supply Chain Basic, you must retrieve your cluster’s base64 encoded ca certificate from $HOME/.kube/config. Retrieve the certificate-authority-data from the respective cluster section and input it as B64_ENCODED_CA in the tap-values.yaml.
The following is the YAML file sample for the full-profile:
shared:
ingress_domain: "INGRESS-DOMAIN"
image_registry:
project_path: "SERVER-NAME/REPO-NAME"
secret:
name: "KP-DEFAULT-REPO-SECRET"
namespace: "KP-DEFAULT-REPO-SECRET-NAMESPACE"
ca_cert_data: |
-----BEGIN CERTIFICATE-----
MIIFXzCCA0egAwIBAgIJAJYm37SFocjlMA0GCSqGSIb3DQEBDQUAMEY...
-----END CERTIFICATE-----
profile: full
ceip_policy_disclosed: true
buildservice:
kp_default_repository: "KP-DEFAULT-REPO"
kp_default_repository_secret: # Takes the value from the shared section by default, but can be overridden by setting a different value.
name: "KP-DEFAULT-REPO-SECRET"
namespace: "KP-DEFAULT-REPO-SECRET-NAMESPACE"
exclude_dependencies: true
supply_chain: basic
contour:
infrastructure_provider: aws
envoy:
service:
type: LoadBalancer
annotations:
# This annotation is for air-gapped AWS only.
service.kubernetes.io/aws-load-balancer-internal: "true"
ootb_supply_chain_basic:
registry:
server: "SERVER-NAME" # Takes the value from the shared section by default, but can be overridden by setting a different value.
repository: "REPO-NAME" # Takes the value from the shared section by default, but can be overridden by setting a different value.
gitops:
ssh_secret: "SSH-SECRET"
maven:
repository:
url: https://MAVEN-URL
secret_name: "MAVEN-CREDENTIALS"
accelerator:
ingress:
include: true
enable_tls: false
git_credentials:
secret_name: git-credentials
username: GITLAB-USER
password: GITLAB-PASSWORD
appliveview:
ingressEnabled: true
appliveview_connector:
backend:
ingressEnabled: true
sslDeactivated: false
host: appliveview.INGRESS-DOMAIN
caCertData: |-
-----BEGIN CERTIFICATE-----
MIIGMzCCBBugAwIBAgIJALHHzQjxM6wMMA0GCSqGSIb3DQEBDQUAMGcxCzAJBgNV
BAgMAk1OMRQwEgYDVQQHDAtNaW5uZWFwb2xpczEPMA0GA1UECgwGVk13YXJlMRMw
-----END CERTIFICATE-----
local_source_proxy:
# Takes the value from the project_path under the image_registry section of shared by default, but can be overridden by setting a different value.
repository: "EXTERNAL-REGISTRY-FOR-LOCAL-SOURCE"
push_secret:
# When set to true, the secret mentioned in this section is automatically exported to Local Source Proxy's namespace.
name: "EXTERNAL-REGISTRY-FOR-LOCAL-SOURCE-SECRET"
namespace: "EXTERNAL-REGISTRY-FOR-LOCAL-SOURCE-SECRET-NAMESPACE"
# When set to true, the secret mentioned in this section is automatically exported to Local Source Proxy's namespace.
create_export: true
tap_gui:
app_config:
auth:
allowGuestAccess: true # This allows unauthenticated users to log in to your portal. If you want to deactivate it, make sure you configure an alternative auth provider.
kubernetes:
serviceLocatorMethod:
type: multiTenant
clusterLocatorMethods:
- type: config
clusters:
- url: https://${KUBERNETES_SERVICE_HOST}:${KUBERNETES_SERVICE_PORT}
name: host
authProvider: serviceAccount
serviceAccountToken: ${KUBERNETES_SERVICE_ACCOUNT_TOKEN}
skipTLSVerify: false
caData: B64_ENCODED_CA
catalog:
locations:
- type: url
target: https://GIT-CATALOG-URL/catalog-info.yaml
#Example Integration for custom GitLab:
integrations:
gitlab:
- host: GITLAB-URL
token: GITLAB-TOKEN
apiBaseUrl: https://GITLABURL/api/v4/
backend:
reading:
allow:
- host: GITLAB-URL # Example URL: gitlab.example.com
metadata_store:
ns_for_export_app_cert: "MY-DEV-NAMESPACE"
app_service_type: ClusterIP # Defaults to LoadBalancer. If shared.ingress_domain is set earlier, this must be set to ClusterIP.
Important
Tanzu Build Service is installed by default with
litedepndencies. When installing Tanzu Build Service in an air-gapped environment, the lite dependencies are not available because they require Internet access. You must install thefulldependencies by settingexclude_dependenciestotrue. The existing ClusterStore instances will not be updated if you switch fromlitedependencies tofulldependencies after the initial installation completes.Installing Grype by using
tap-values.yamlas follows is deprecated in v1.6 and will be removed in v1.8:grype: targetImagePullSecret: "TARGET-REGISTRY-CREDENTIALS-SECRET"You can install Grype by using Namespace Provisioner instead.
Where:
-
INGRESS-DOMAINis the subdomain for the host name that you point at thetanzu-shared-ingressservice’s External IP address. -
KP-DEFAULT-REPOis a writable repository in your registry. Tanzu Build Service dependencies are written to this location. Examples:- Harbor has the form
kp_default_repository: "my-harbor.io/my-project/build-service". - Docker Hub has the form
kp_default_repository: "my-dockerhub-user/build-service"orkp_default_repository: "index.docker.io/my-user/build-service". - Google Cloud Registry has the form
kp_default_repository: "gcr.io/my-project/build-service".
- Harbor has the form
-
KP-DEFAULT-REPO-SECRETis the secret with user credentials that can write toKP-DEFAULT-REPO. You candocker pushto this location with this credential.- For Google Cloud Registry, use
kp_default_repository_username: _json_key. - You must create the secret before the installation. For example, you can use the
registry-credentialssecret created earlier.
- For Google Cloud Registry, use
-
KP-DEFAULT-REPO-SECRET-NAMESPACEis the namespace whereKP-DEFAULT-REPO-SECRETis created. -
SERVER-NAMEis the host name of the registry server. Examples:- Harbor has the form
server: "my-harbor.io". - Docker Hub has the form
server: "index.docker.io". - Google Cloud Registry has the form
server: "gcr.io".
- Harbor has the form
-
REPO-NAMEis where workload images are stored in the registry. If this key is passed through the shared section earlier and AWS ECR registry is used, you must ensure that theSERVER-NAME/REPO-NAME/buildserviceandSERVER-NAME/REPO-NAME/workloadsexist. AWS ECR expects the paths to be pre-created. -
Images are written to
SERVER-NAME/REPO-NAME/workload-name. Examples:- Harbor has the form
repository: "my-project/supply-chain". - Docker Hub has the form
repository: "my-dockerhub-user". - Google Cloud Registry has the form
repository: "my-project/supply-chain".
- Harbor has the form
-
EXTERNAL-REGISTRY-FOR-LOCAL-SOURCEis where the developer’s local source is uploaded when using Tanzu CLI to use Local Source Proxy for workload creation.If an AWS ECR registry is being used, ensure that the repository already exists. AWS ECR expects the repository path to already exist. This destination is represented as
REGISTRY-SERVER/REPOSITORY-PATH. For more information, see Install Local Source Proxy. -
EXTERNAL-REGISTRY-FOR-LOCAL-SOURCE-SECRETis the name of the secret with credentials that allow pushing to theEXTERNAL-REGISTRY-FOR-LOCAL-SOURCErepository. -
EXTERNAL-REGISTRY-FOR-LOCAL-SOURCE-SECRET-NAMESPACEis the namespace in whichEXTERNAL-REGISTRY-FOR-LOCAL-SOURCE-SECRETis available. -
SSH-SECRETis the secret name for https authentication, certificate authority, and SSH authentication. See Git authentication for more information. -
MAVEN-CREDENTIALSis the name of the secret with maven creds. This secret must be in the developer namespace. You can create it after the fact. -
GIT-CATALOG-URLis the path to thecatalog-info.yamlcatalog definition file. You can download either a blank or populated catalog file from the Broadcom Support Portal (file name Tanzu Application Platform Developer Portal Blank Catalog or Tanzu Application Platform Developer Portal Yelb Catalog). Otherwise, you can use a Backstage-compliant catalog you’ve already built and posted on the Git infrastructure. -
GITLABURLis the host name of your GitLab instance. -
GITLAB-USERis the user name of your GitLab instance. -
GITLAB-PASSWORDis the password for theGITLAB-USERof your GitLab instance. This can also be theGITLAB-TOKEN. -
GITLAB-TOKENis the API token for your GitLab instance. -
MY-DEV-NAMESPACEis the name of the developer namespace. SCST - Store exports secrets to the namespace, and SCST - Scan deploys theScanTemplatesthere. This allows the scanning feature to run in this namespace. If there are multiple developer namespaces, usens_for_export_app_cert: "*"to export the SCST - Store CA certificate to all namespaces. To install Grype in multiple namespaces, use a namespace provisioner. See Namespace Provisioner. -
TARGET-REGISTRY-CREDENTIALS-SECRETis the name of the secret that contains the credentials to pull an image from the registry for scanning.
NoteThe
appliveview_connector.backend.sslDisabledkey is deprecated and renamed toappliveview_connector.backend.sslDeactivated.
If you use custom CA certificates, you must provide one or more PEM-encoded CA certificates under the ca_cert_data key. If you configured shared.ca_cert_data, Tanzu Application Platform component packages inherit that value by default.
TLS is enabled by default on Application Live View back end using ClusterIssuer. Set the ingressEnabled key to true for TLS to be enabled on Application Live View back end using ClusterIssuer. This key is set to false by default.
The appliveview-cert certificate is generated by default and its issuerRef points to the .ingress_issuer value. The ingress_issuer key consumes the value shared.ingress_issuer from tap-values.yaml by default when you don’t specify the ingress_issuer in tap-values.yaml.
When ingressEnabled is true, an HTTPProxy object is created in the cluster and appliveview-cert certificate is generated by default in the app_live_view namespace. The secretName appliveview-cert stores this certificate.
To verify the HTTPProxy object with the secret, run:
kubectl get httpproxy -A
Expected output:
NAMESPACE NAME FQDN TLS SECRET STATUS STATUS DESCRIPTION
app-live-view appliveview appliveview.192.168.42.55.nip.io appliveview-cert valid Valid HTTPProxy
The appliveview_connector.backend.host key is the back end host in the view cluster. The appliveview_connector.backend.caCertData key is the certificate retrieved from the HTTPProxy secret exposed by Application Live View back end in the view cluster. To retrieve this certificate, run the following command in the view cluster:
kubectl get secret appliveview-cert -n app-live-view -o yaml | yq '.data."ca.crt"' | base64 -d
Install your Tanzu Application Platform package
Follow these steps to install the Tanzu Application Platform package:
-
Install the package by running:
tanzu package install tap -p tap.tanzu.vmware.com -v $TAP_VERSION --values-file tap-values.yaml -n tap-installWhere
$TAP_VERSIONis the Tanzu Application Platform version environment variable you defined earlier. -
Verify the package install by running:
tanzu package installed get tap -n tap-installThis may take 5-10 minutes because it installs several packages on your cluster.
-
Verify that all the necessary packages in the profile are installed by running:
tanzu package installed list -A