You can offer a service to a VMware Tanzu Application Service for VMs (TAS for VMs) services Marketplace.
For information about consuming these services, see Managing App Requests with Route Services.
TAS for VMs app developers might want to apply transformation or processing to requests before they reach an app. Common use cases include authentication, rate limiting, and caching services.
Route services are a kind of Marketplace service that you can use to apply various transformations to app requests by binding an app’s route to a service instance. Through integrations with service brokers and, optionally, with the TAS for VMs routing tier, providers can offer these services to developers with a familiar, automated, self-service, and on-demand user experience.
The procedures in this topic use the Cloud Foundry Command Line Interface (cf CLI). You can also manage route services using Apps Manager. For more information, see the Manage Route Services section of the Managing Apps and Service Instances Using Apps Manager topic.
Architecture
TAS for VMs supports the following models for route services, each of which is described in this topic:
In each model, you configure a route service to process traffic addressed to an app.
Fully-brokered service
In the fully-brokered service model, the TAS for VMs router receives all traffic to apps in the deployment before any processing by the route service. You can bind a route service to any app, and if an app is bound to a route service, the TAS for VMs router sends the traffic to the service. After the route service processes requests, it sends it back to the load balancer in front of the TAS for VMs router. The second time through, the TAS for VMs router recognizes that the route service has already handled them, and forwards them directly to app instances.
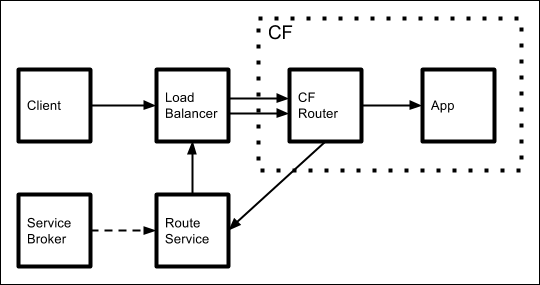
The route service can run inside or outside of TAS for VMs, as long as it fulfills the Service Instance responsibilities to integrate it with the TAS for VMs router.
A service broker publishes the route service to the TAS for VMs marketplace, and makes it available to developers.
You can then create an instance of the service and bind it to your apps with the following commands:
cf create-service BROKER-SERVICE-PLAN SERVICE-INSTANCE
cf bind-route-service YOUR-APP-DOMAIN SERVICE-INSTANCE [--hostname HOSTNAME] [--path PATH]
Developers configure the service either through the service provider’s web interface or by passing arbitrary parameters to their cf create-service call through the -c flag.
Advantages:
-
Developers can use a Service Broker to dynamically configure how the route service processes traffic to specific apps.
-
Adding route services requires no manual infrastructure configuration.
- Traffic to apps that do not use the service makes fewer network hops because requests for those apps do not pass through the route service.
Disadvantages:
- Traffic to apps that use the route service makes additional network hops, as compared to the static model.
Static, brokered service
In the static, brokered service model, an operator installs a static routing service, which might be a piece of hardware, in front of the load balancer. The routing service runs outside of TAS for VMs and receives traffic to all apps running in the TAS for VMs deployment. The service provider creates a service broker to publish the service to the TAS for VMs marketplace. As with a fully-brokered service, you can use the service by instantiating it with cf create-service and binding it to an app with cf bind-route-service.
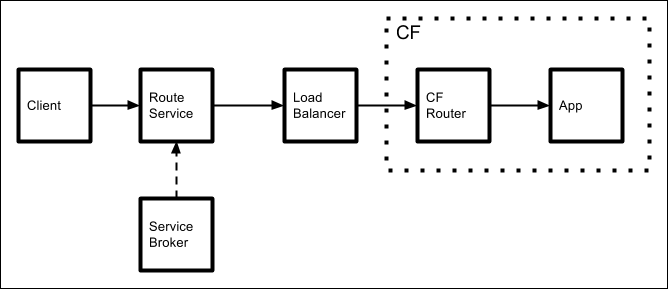
In this model, you configure route services on an app-by-app basis. When you bind a service to an app, the service broker directs the routing service to process that app’s traffic rather than passing the requests through unchanged.
Advantages:
-
Developers can use a service broker to dynamically configure how the route service processes traffic to specific apps.
-
Traffic to apps that use the route service takes fewer network hops.
Disadvantages:
- Adding route services requires manual infrastructure configuration.
- Traffic to apps that do not use the route service make unnecessary network hops. Requests for all apps hosted by the deployment pass through the route service component.
User-provided service
If a route service is not listed in the TAS for VMs marketplace by a broker, a developer can still bind it to their app as a user-provided service. The service can run anywhere, either inside or outside of TAS for VMs, but it must fulfill the integration requirements described in Service Instance responsibilities. The service also needs to be reachable by an outbound connection from the TAS for VMs router.
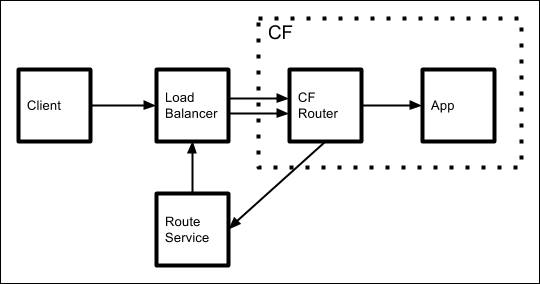
This model is identical to the fully-brokered service model, except without the broker. You can configure the service manually, outside of TAS for VMs.
You can then create a user provided service instance and bind it to your app with the following commands,that supply the URL of their route service:
This model is identical to the fully-brokered service model, except without the broker. Developers configure the service manually, outside of TAS for VMs. They can then create a user-provided service instance and bind it to their app with the following commands, supplying the URL of their route service:
cf create-user-provided-service SERVICE-INSTANCE -r ROUTE-SERVICE-URL
cf bind-route-service DOMAIN SERVICE-INSTANCE [--hostname HOSTNAME]
Advantages:
- Adding route services requires no manual infrastructure configuration.
- Traffic to apps that do not use the service makes fewer network hops because requests for those apps do not pass through the route service.
Disadvantages:
- Developers must manually provision and configure route services out of the context of TAS for VMs because no service broker automates these operations.
- Traffic to apps that use the route service makes additional network hops, as compared to the static model.
Architecture comparison
The previous models require the broker and service instance responsibilities summarized in the following table:
| Route Services Architecture | Fulfills TAS for VMs Service Instance Responsibilities (1) | Fulfills TAS for VMs Broker Responsibilities (2) |
|---|---|---|
| Fully-Brokered | Yes | Yes |
| Static Brokered | No | Yes |
| User-Provided | Yes | No |
2 - See Broker Responsibilities
Service instance
The following information applies only when a broker returns route_service_url in a bind response.
Binding a service instance to a route associates the route_service_url with the route in the TAS for VMs router. All requests for the route are proxied to the URL specified by route_service_url.
The TAS for VMs router includes the X-CF-Forwarded-Url header containing the originally requested URL, as well as the X-CF-Proxy-Signature and X-CF-Proxy-Metadata headers used by the router to validate that the route-service sent the request. These headers are described in the Headers section, below.
Service instance responsibilities
The route service must handle requests by either:
- Accepting the request by making a new request to the originally requested URL, or to another location, and then responding to the originating requestor
- Rejecting the request by responding with a non-
2xxHTTP status code
When forwarding a request to the originally requested URL, the route service must forward the X-CF-Forwarded-Url, X-CF-Proxy-Signature, and X-CF-Proxy-Metadata headers on the request. If it doesn’t, it is rejected. When forwarding a request to a location other than the originally requested URL, the route service should strip these headers.
Headers
The following HTTP headers are added by the Gorouter to requests forwarded to route services.
X-CF-Forwarded-Url
The X-CF-Forwarded-Url header contains the originally requested URL. The route service may choose to forward the request to this URL or to another.
X-CF-Proxy-Signature
When the Gorouter receives a request with this header, it will accept and forward the request to the app only if the URL of the request matches the one associated with the token, and if the request was received on time. Otherwise, the request is rejected.
X-CF-Proxy-Signature also signals to the Gorouter that a request has transited a route service. If this header is present, the Gorouter does not forward the request to a route service. The route-service needs to forward these headers in subsequent requests to the orignally requested URL, so that it knows not to send the request back to the route service but to the app. The headers should NOT be sent in the HTTP reponse to the GoRouter, only in the new HTTP request to the GoRouter.
The X-CF-Proxy-Signature header is an access token. Anyone possessing your X-CF-Proxy-Signature token can bypass the route service. Do not share your your X-CF-Proxy-Signature token with anyone. CF-hosted Route Services cannot be chained: If the route service forwards the request to a URL which resolves to a route for a different app on TAS for VMs, the route must not have a bound route service. Otherwise, the request is rejected as the requested URL does not match the one in the forwarded `X-CF-Proxy-Signature` header. #### X-CF-Proxy-Metadata The `X-CF-Proxy-Metadata` header aids in the encryption and description of `X-CF-Proxy-Signature`. ### SSL certificates When TAS for VMs is deployed in a development environment, certificates hosted by the load balancer are self-signed, and not signed by a trusted Certificate Authority. When the route service finishes processing an inbound request and makes a call to the value of `X-CF-Forwarded-Url`, be prepared to accept the self-signed certificate when integrating with a non-production deployment of TAS for VMs. ### Timeouts Route services must forward the request to the app route within 60 seconds. In addition, all requests must respond in 900 seconds. ## Broker responsibilities ### Catalog endpoint Brokers must include `requires: ["route_forwarding"]` for a service in the catalog endpoint. If this is not present, TAS for VMs does not permit users to bind an instance of the service to a route. ### Binding endpoint When users bind a route to a service instance, TAS for VMs sends a bind request to the broker, including the route address with `bind_resource.route`. A route is an address used by clients to reach apps mapped to the route. The broker may return `route_service_url`, containing a URL where TAS for VMs should proxy requests for the route. This URL must have an `https` scheme, or the Cloud Controller rejects the binding. `route_service_url` is optional, and not returning this field enables a broker to dynamically configure a network component already in the request path for the route, requiring no change in the TAS for VMs router. For more information about bind requests, see the [Binding](https://github.com/openservicebrokerapi/servicebroker/blob/v2.13/spec.md#binding) section of the _Open Service Broker API (v2.13)_ spec on GitHub. ## Route services examples - [Logging Route Service](https://github.com/cloudfoundry/cf-acceptance-tests/tree/release-candidate/assets/logging-route-service): This route service can be pushed as an app to TAS for VMs. It fulfills the service instance responsibilities noted previously and logs requests received and sent. It can be used to see the route service integration in action by tailing its logs. - [Rate Limiting Route Service](https://github.com/cloudfoundry-samples/ratelimit-service): This example route service is a simple TAS for VMs app that provides rate limiting to control the rate of traffic to an app. * [Spring Boot examples] (https://github.com/in28minutes/spring-boot-examples). ## Tutorial The following instructions show how to use the Logging Route Service described in [Route Services examples](#examples) to verify that when a route service is bound to a route, requests for that route are proxied to the route service. For a video of this tutorial, see [Route Services in Pivotal Cloud Foundry 1.7](https://youtu.be/VaaZJE2E4jI) on YouTube. These commands requires the Cloud Foundry Command Line Interface (cf CLI) v6.16 or later. To use the logging route service: 1. Push the logging route service as an app by running: ``` cf push logger ``` 1. Create a user-provided service instance, and include the route of the logging route service you pushed as `route_service_url`. Be sure to use `https` for the scheme. Run: ``` cf create-user-provided-service mylogger -r https://logger.cf.example.com ``` 1. Push a sample app like [Spring Music](https://github.com/cloudfoundry-samples/spring-music). By default, this creates a route `spring-music.cf.example.com`. Run: ``` cf push spring-music ``` 1. Bind the user-provided service instance to the route of your sample app. The `bind-route-service` command takes a route and a service instance; the route is specified in the following example by domain `cf.example.com` and hostname `spring-music`. Run: ``` cf bind-route-service cf.example.com mylogger --hostname spring-music ``` 1. Tail the logs for your route service by running: ``` cf logs logger ``` 1. Send a request to the sample app and view in the route service logs that the request is forwarded to it by running: ``` curl spring-music.cf.example.com ```