You can configure an F5 BIG-IP Local Traffic Manager (LTM) as a load balancer for VMware Tanzu Application Service for VMs (TAS for VMs).
These instructions assume you are familiar with the following concepts:
- Deploying an F5 physical/virtual appliance
- F5 UI and F5 Traffic Management Shell (
tmsh) - Creating admin users on the F5 load balancer
- Creating F5 self-IPs, VLANs, and routes
For guidance about the previous topics, see AskF5.
You must configure your F5 load balancer before you install TAS for VMs.
To use your F5 deployment as a load balancer, you must configure it to forward unencrypted HTTP following these steps. This procedure assumes that you are running F5 v12.1.2 or v13.0.0.
The following TAS for VMs configuration option forwards unencrypted traffic to the Gorouter. It assumes an external load balancer is configured to forward unencrypted traffic.
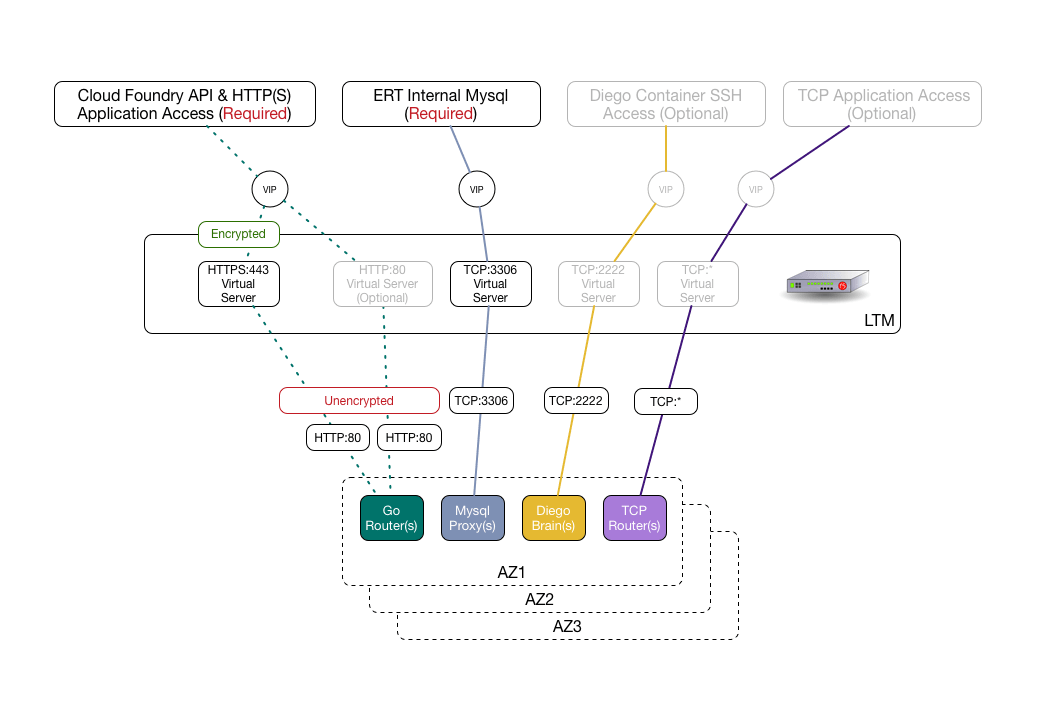
This configuration stops client SSL at the F5 and forward standard HTTP traffic to the backend Gorouters from the LTM. All TCP back ends accept forwarded traffic from the LTM:
-
In the F5 UI, go to Local Traffic.
-
Go to iRules and click iRule List.
-
Create the following rules:
- Name:
cf-xforward-forDefinition:when HTTP_REQUEST { HTTP::header insert X-Forwarded-For [IP::remote_addr] } - Name:
cf-xforward-proto-httpsDefinition:when HTTP_REQUEST { HTTP::header insert X-Forwarded-Proto "https" } - Name:
cf-xforward-proto-httpDefinition:when HTTP_REQUEST { HTTP::header insert X-Forwarded-Proto "http" }
- Name:
-
Go to System, then File Management, and click SSL Certificate List.
- Import your TAS for VMs certificate and name it
pcf-pas-cert. - Import your TAS for VMs certificate key and name it
pcf-pas-key.
- Import your TAS for VMs certificate and name it
-
Go to Local Traffic and click Monitors.
- Create a
gorouterhealth monitor and give it the following parameters:- Name:
gorouter_mon - Type:
HTTP - Send String:
GET /health HTTP/1.0\r\n - Alias Service Port:
8080 - Receive String:
ok
- Name:
- Create a
sshproxyhealth monitor and give it the following parameters:- Name:
diegobrain_mon - Type:
TCP - Alias Service Port:
2222
- Name:
- Create a
tcprouterhealth monitor and give it the following parameters:- Name:
tcprouter_mon - Type:
HTTP - Send String:
GET /health - Alias Service Port:
80
- Name:
- Create a
-
Create all required nodes:
- Go to Local Traffic, then Nodes, and click Node List.
- Create the desired number of
gorouternodes, one for each Gorouter in your TAS for VMs deployment, and give it the following parameters:- Name:
gorouter-# - Address:
[IP-ADDRESS-OF-GOROUTER] - State:
enabled - Health Monitors:
Node Default
- Name:
- Create the desired number of
diegobrainnodes, one for each Diego Brain in your TAS for VMs deployment, and give it the following parameters:- Name:
diegobrain-# - Address:
[IP-ADDRESS-OF-DIEGOBRAIN] - State:
enabled - Health Monitors:
Node Default
- Name:
- Create the desired number of
tcprouternodes, one for each TCP Router in your TAS for VMs deployment, and give it the following parameters:- Name:
tcprouter-# - Address:
[IP-ADDRESS-OF-TCPROUTER] - State:
enabled - Health Monitors:
Node Default
- Name:
-
Create three member pools:
- Go to Local Traffic and click Pools.
- Create a
gorouterpool and give it the following parameters:- Name:
gorouter_pool - Health Monitors:
gorouter_mon - Load Balancing Method:
Least Connections - Add all
gorouter-#nodes.- Service Port:
80
- Service Port:
- Name:
- Create a
diegobrainpool and give it the following parameters:- Name:
diegobrain_pool - Health Monitors:
diegobrain_mon - Load Balancing Method:
Least Connections - Add all
diegobrain-#nodes.- Service Port:
2222
- Service Port:
- Name:
- Create a
tcprouterpool and give it the following parameters:- Name:
tcprouter_pool - Health Monitors:
tcprouter_mon - Load Balancing Method:
Least Connections - Add all
tcprouter-#nodes.- Service Port:
*/0
- Service Port:
- Name:
-
Create an SSL client profile.
- Go to Local Traffic, then Profiles, then SSL, and click Client.
- Create an SSL client profile and give it the following parameters:
- Name:
pcf-ssl-client-certs-profile - Parent Profile:
clientssl - Custom:
[TRUE] - Add a certificate key chain.
- Certificate:
pcf-pas-cert - Key:
pcf-pas-key
Your deployment might require additional root or intermediate certificates. You can select them here. Additionally, you can also enter passphrases for certificates.
- Certificate:
- Name:
-
Create four LTM virtual servers. One is required, while three are optional.
- Go to Local Traffic, click Virtual Servers, and click Virtual Server List.
- (Required) Create a virtual server for HTTPS access to Cloud Foundry API and apps and give it the following parameters:
- Name:
pcf-https - Type:
Standard - Source Address:
0.0.0.0/0 - Destination Address/Mask:
YOUR-PCF-VIP
This VIP must be DNS-resolvable to your system domain and default apps domains.
- Service Port:
443 - State:
Enabled - Protocol:
TCP - Protocol Profile (Client):
tcp_lan_optimized - Protocol Profile (Server): (Use Client Profile)
- HTTP Profile:
http - SSL Profile:
pcf-ssl-client-certs-profile - VLAN and Tunnel Traffic:
Enabled on YOUR-CONFIGURED-F5-VPN - Source Address Translation:
Auto Map
This must be set in one-arm configurations.
- Default Pool:
gorouter_pool - iRules:
cf-xforward-forandcf-xforward-proto-https
- Name:
- (Optional) Create a virtual server for HTTP access to apps and give it the following parameters:
- Name:
pcf-http - Type:
Standard - Source Address:
0.0.0.0/0 - Destination Address/Mask:
YOUR-PCF-VIP
This VIP must be DNS-resolvable to your system domain and default apps domains.
- Service Port:
80 - State:
Enabled - Protocol:
TCP - Protocol Profile (Client):
tcp_lan_optimized - Protocol Profile (Server): (Use Client Profile)
- HTTP Profile:
http - SSL Profile:
[NONE] - VLAN and Tunnel Traffic:
Enabled on YOUR-CONFIGURED-F5-VPN - Source Address Translation:
Auto Map
This must be set in one-arm configurations.
- Default Pool:
gorouter_pool - iRules:
cf-xforward-forandcf-xforward-proto-http
- Name:
-
(Optional) Create a virtual server for
sshproxy. This virtual server allows developers to SSH into Diego containers.Give it the following parameters:- Name:
pcf-sshproxy - Type:
Standard - Source Address:
0.0.0.0/0 - Destination Address/Mask:
YOUR-SSH-PROXY-VIP
This VIP must be DNS resolvable to ssh.[YOUR-PCF-PAS-SYSTEM-DOMAIN].
- Service Port:
2222 - State:
Enabled - Protocol:
TCP - Protocol Profile (Client):
tcp_lan_optimized - Protocol Profile (Server): (Use Client Profile)
- HTTP Profile:
[NONE] - SSL Profile:
[NONE] - VLAN and Tunnel Traffic:
Enabled on YOUR-CONFIGURED-F5-VPN - Source Address Translation:
Auto Map
This must be set in one-arm configurations.
- Default Pool:
diegobrain_pool
- Name:
- (Optional) Create a virtual server for
tcprouter. This virtual server allows access to the TCP app. Give it the following parameters:- Name:
pcf-tcprouter - Type:
Standard - Source Address:
0.0.0.0/0 - Destination Address/Mask:
[YOUR-TCP-ROUTER-VIP]
This VIP must be DNS-resolvable to tcp.[YOUR-CONFIGURED-TCP-DOMAIN].
- Service Port:
*/0 - State:
Enabled - Protocol:
TCP - Protocol Profile (Client):
tcp_lan_optimized - Protocol Profile (Server): (Use Client Profile)
- HTTP Profile:
[NONE] - SSL Profile:
[NONE] - VLAN and Tunnel Traffic:
Enabled on YOUR-CONFIGURED-F5-VPN - Source Address Translation:
Auto Map
This must be set in one-arm configurations.
- Default Pool:
tcprouter_pool
- Name:
Once you complete the configuration, verify that everything in Network Map located in Local Traffic Menu is green.
F5 single configuration files
Single configuration files (SCFs) are single files containing a complete F5 configuration for F5 v11.x and v12.x. This section contains sample SCF files for functional reference configurations. Often, presenting a reference SCF “template” to an F5 admin can provide all necessary configuration information for configuring an F5 load balancer for TAS for VMs.
You can create SCFs by using tmsh Run:
save /sys config file SCF-FILENAME no-passphrase
Where SCF-FILENAME is the name of the SCF you want to create.
You can also edit SCFs and use them as a template to replicate configurations across multiple F5s by using tmsh. Run:
load /sys config file SCF-FILENAME
Where SCF-FILENAME is the name of the SCF you want to edit.
For more information, see Overview of Single Configuration Files (11.x - 13.x).
For a sample SCF, see pcf-f5-recipe1-scf.txt in the PCF F5 Cookbook repository on GitHub.
Additional F5 resources
For information about F5 iRules that can be useful when configuring an F5 load balancer for TAS for VMs, see the VMware Tanzu CF iRules For F5 repository on GitHub.