Tanzu Kubernetes Grid 2.2 Compliance and Hardening
Tanzu Kubernetes Grid Compliance and Hardening recommends a baseline security posture for an environment on which you deploy Tanzu Kubernetes Grid (TKG) and provides guidance for hardening TKG to achieve Authority to Operate (ATO).
TKG releases are continuously validated against the Defense Information Systems Agency (DISA) Kubernetes Security Technical Implementation Guide (STIG), NSA/CISA Kubernetes Hardening Guide, and the National Institute of Standards and Technology (NIST) guidelines.
Disclaimer
Following the hardening guidance provided in this document may not be effective in all cases and could impact the functionality of your software and applications. It is your responsibility to test STIG settings and hardening results to ensure that your application still functions properly as it maintains system security.
Intended audience
This publication is intended for the Information System Security Officer/Manager (ISSO/ISSM) who is responsible for implementing security controls. Its content enables the ISSO/ISSM to understand and authorize best-practice decisions to enable security plans and perform risk analysis.
This publication also links to hardened images and security updates, for use by security administrators.
Risk management framework
The Risk Management Framework (RMF) provides a process that integrates security, privacy, and cyber supply chain risk management activities into the system development lifecycle. The diagram below shows the RMF workflow that you would follow to reach ATO.
To facilitate the RMF process and the creation of your accreditation package, VMware supports the following steps and provides artifacts for them as shown below.
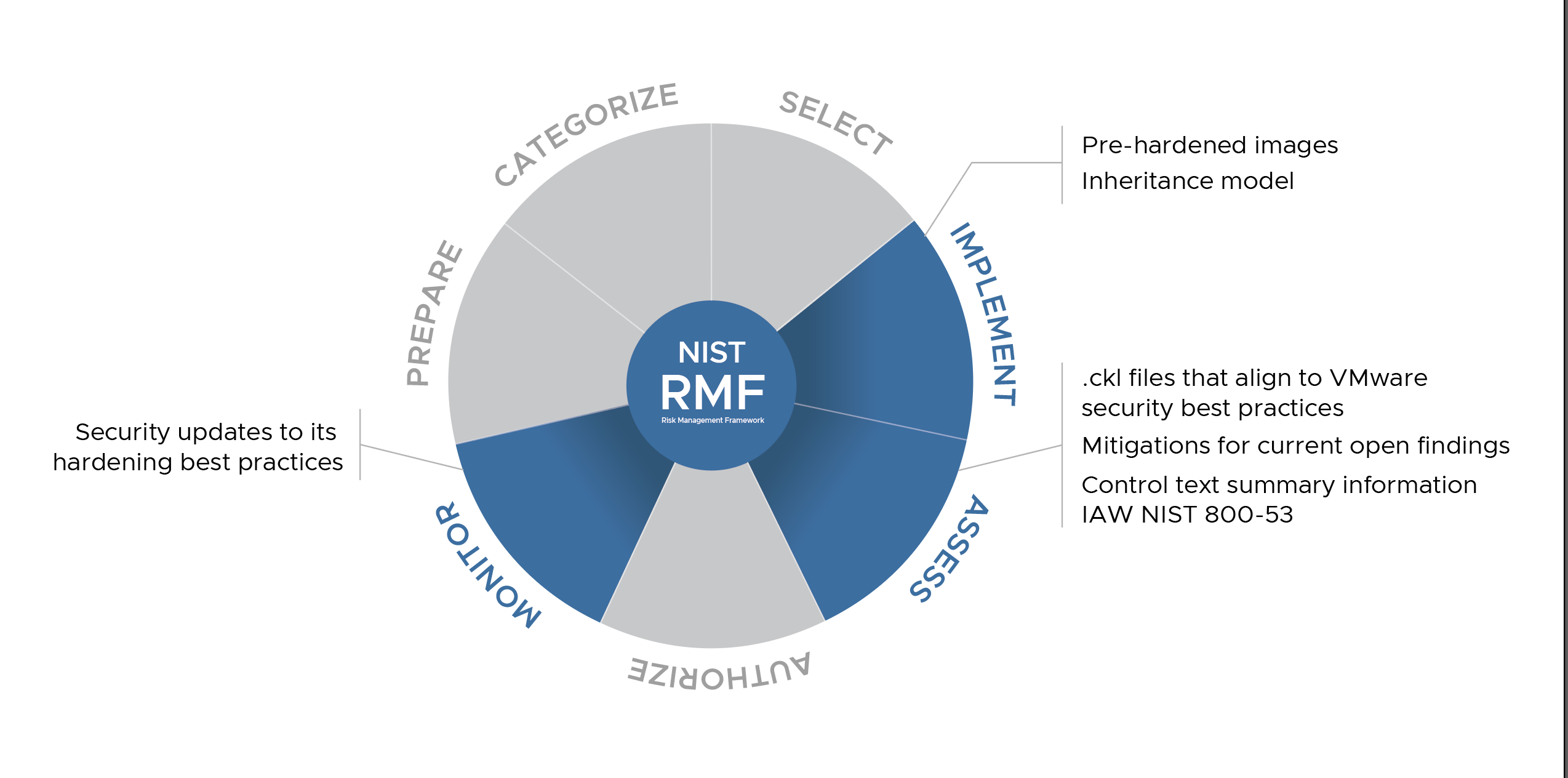
Implement
The following topics cover how-to information for hardening TKG clusters to address STIG and NSA/CISA standards, hardening results and exceptions, and artifacts for use to achieve your compliance goals.
- STIG hardening for TKG Ubuntu hosts
- STIG hardening for TKG clusters
- NSA/CISA hardening for TKG clusters
- NIST 800-53 Inheritance Model (.xlsx)
- This model applies to TKG v2.1 and v2.2.
NoteFor STIG compliance, the method you use to harden your cluster depends on whether the cluster is class-based or plan-based. For information about class-based and plan-based clusters, see Workload Cluster Types in the Tanzu Kubernetes Grid documentation.
Assess
TKG is hardened to the following STIG benchmarks:
During the RMF Assess step, cybersecurity personnel can use mitigation and control text from the following checklists (.ckl) to fill out their accreditation package. This data represents VMware best practices, and your individual implementation may differ. Verify all security settings in your production environment to support the functionality of your system.
Results of hardening TKG to VMware best practices
The following checklist files align to VMware security best practices:
- Ubuntu 20.04 STIG checklist
- Control plane Kubernetes STIG checklist
- Worker node Kubernetes STIG checklist
These checklists apply to TKG v2.1 and v2.2.
Mitigation for current open findings
The following exceptions and control responses provide mitigations for open findings:
- Ubuntu 20.04 STIG exceptions
- Kubernetes STIG exceptions
- Control text summary information IAW NIST 800-53 (.xlsx)
- This information applies to TKG v2.1 and v2.2.
Ports
For information about ports, see Ports, protocols, and services management(PPSM).
Monitor
VMware continuously monitors our products for security-relevant events and configuration changes that negatively affect security posture. For security updates, see TKG release notes.