How do I create a compliance policy
To secure your infrastructure assets with Tanzu Salt, you must start by defining policies.
Tanzu Salt provides different industry benchmarks to choose from including checks for Center for Internet Security (CIS) and more. Each benchmark includes a collection of security checks. You can choose to apply all available checks for a given benchmark, or use only a subset of available checks. Using a subset of checks is useful for customizing Tanzu Salt Compliance for your unique infrastructure needs, for example if remediating a given check poses the risk of breaking a known dependency.
When creating your policy, you must select a target to apply the policy to, along with which benchmarks and checks to run against your system.
To connect to the SDK directly, see the Tanzu Salt developer documentation.
What are targets
A target is the group of minions, across one or many Salt masters, that a job’s Salt command applies to. A Salt master is managed similarly to a minion and can be a target if it is running the minion service. When creating a policy and selecting a target, you are defining the nodes that the security checks are run against. You can choose an existing target or create a new one.
What are benchmarks
Tanzu Salt simplifies the process of defining your security policy by grouping security checks by benchmark.
Benchmarks are category of security checks. Tanzu Salt benchmarks are defined by widely-accepted experts, while custom benchmarks are defined by your own organization’s standards. You can use benchmarks to help create a range of different policies optimized for different groups of nodes. For example, you might create an Oracle Linux policy that applies CIS checks to your Oracle Linux minions, and a Windows policy that applies CIS checks to your Windows minions. For more information on creating custom content, see Creating custom compliance components.
Note: Specifically for Windows Server benchmarks, the CIS content for certain benchmarks (notated with a tooltip ![]() ) is distributed across three different benchmarks:
) is distributed across three different benchmarks:
- Domain master content
- Member content
- Domain master and member content
If you want to include all Member content, you must select both the benchmarks for Member and benchmarks for Domain master and member.
What are checks
A check is a security standard that Tanzu Salt assesses for compliance. The Tanzu Salt library updates checks frequently as security standards change. In addition to checks included the Tanzu Salt content library, you can create your own custom checks. Custom checks are indicated by a user icon ![]() , instead of the
, instead of the ![]() built-in-checks-shield-icon. For more information on creating custom content, see Creating custom compliance components. Each check includes several information fields.
built-in-checks-shield-icon. For more information on creating custom content, see Creating custom compliance components. Each check includes several information fields.
| Information field | Description |
|---|---|
| Description | Description of the check. |
| Action | Description of the action that is performed during remediation. |
| Break | Used for internal testing only. For more information, contact your administrator. |
| Global Description | Detailed description of the check. |
| Osfinger | List of osfinger values that the check is implemented for. Osfinger is found in grains items for each minion to identify the minion’s operating system and major release version. Grains are collected for the operating system, domain name, IP address, kernel, OS type, memory, and other system properties. |
| Profile | List of configuration profiles for different benchmarks. |
| Rationale | Description of rationale for implementing the check. |
| Refs | Compliance cross-references between benchmarks. |
| Remediate | Values that indicate if Tanzu Salt is capable of remediating noncompliant nodes, as not all checks include specific, actionable remediation steps. |
| Remediation | Description of how any noncompliant systems are remediated, if applicable. |
| Scored | CIS benchmark Scored value. Score recommendations impact the target’s benchmark score, while recommendation that are not scored do not affect the score. True indicates scored and false indicates not scored. |
| State file | Copy of the Salt state that is applied to perform the check and if applicable, the subsequent remediation. |
| Variables | Variables in Tanzu Salt used to pass values into the Salt states that make up security checks. For best results, use the default values. For more information, see How do I use Salt states. |
| Schedules | Select the schedule frequency from Recurring, Repeat Date & Time, Once, or Cron Expression. Additional options are available, depending on the scheduled activity, and on the schedule frequency you choose. |
Note:
You can exempt checks and minions from remediation by clicking Add Exemption, entering the reason for exemption and clicking Add Exemption again to confirm. Remediation is skipped for exempted items.
Create a compliance policy
-
On the Tanzu Salt home page, click Create Policy.
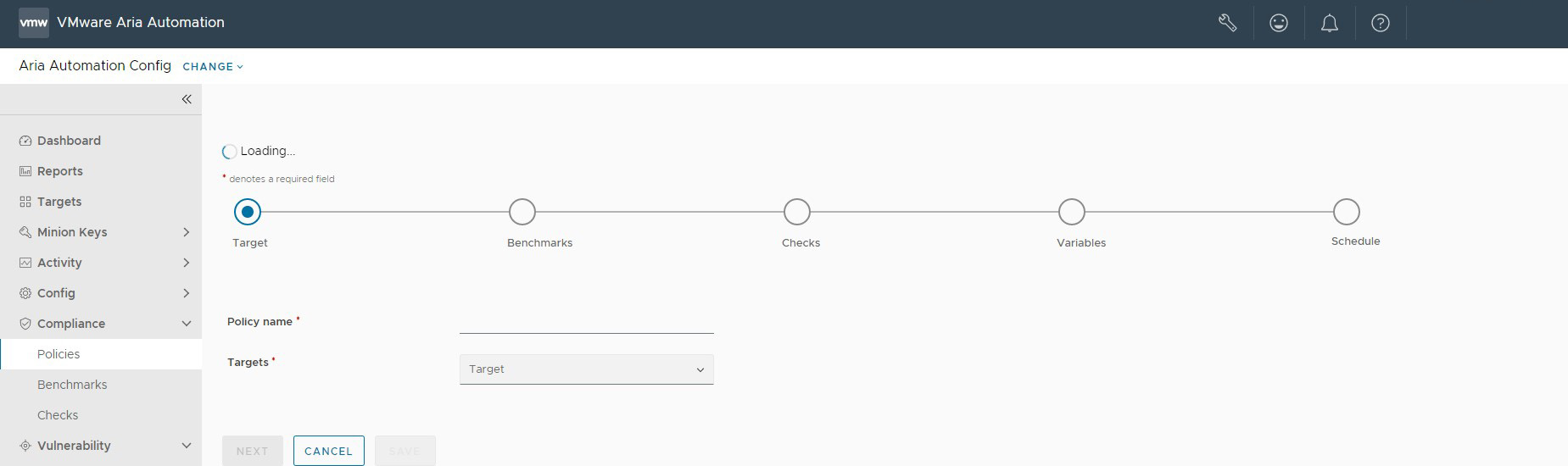
-
Enter the policy name and select a target to apply the policy. Click Next.
-
On the Benchmarks tab, select all benchmarks you want to include in the policy and then click Next.
Note:
If no benchmarks are available, you might need to download compliance content. You can update and download content to the security library by clicking >Administration > Secure Hosts on the side menu, and then selecting Compliance Content - Secure Hosts > Check for updates. -
On the Checks tab, select all checks that you would like to include in the policy. The available checks are determined by the benchmarks you selected in step 3. Click Next.
-
On the Variables tab, enter or modify variables as needed. You can also choose to accept the default values (recommended). Click Next.
-
On the schedule page, define the schedule frequency and click Save.
-
(Optional) To run an assessment immediately after saving your policy, select Run assessment on save.
-
Click Save.
The policy is saved. If you selected Run assessment on save, the assessment is run immediately after saving.
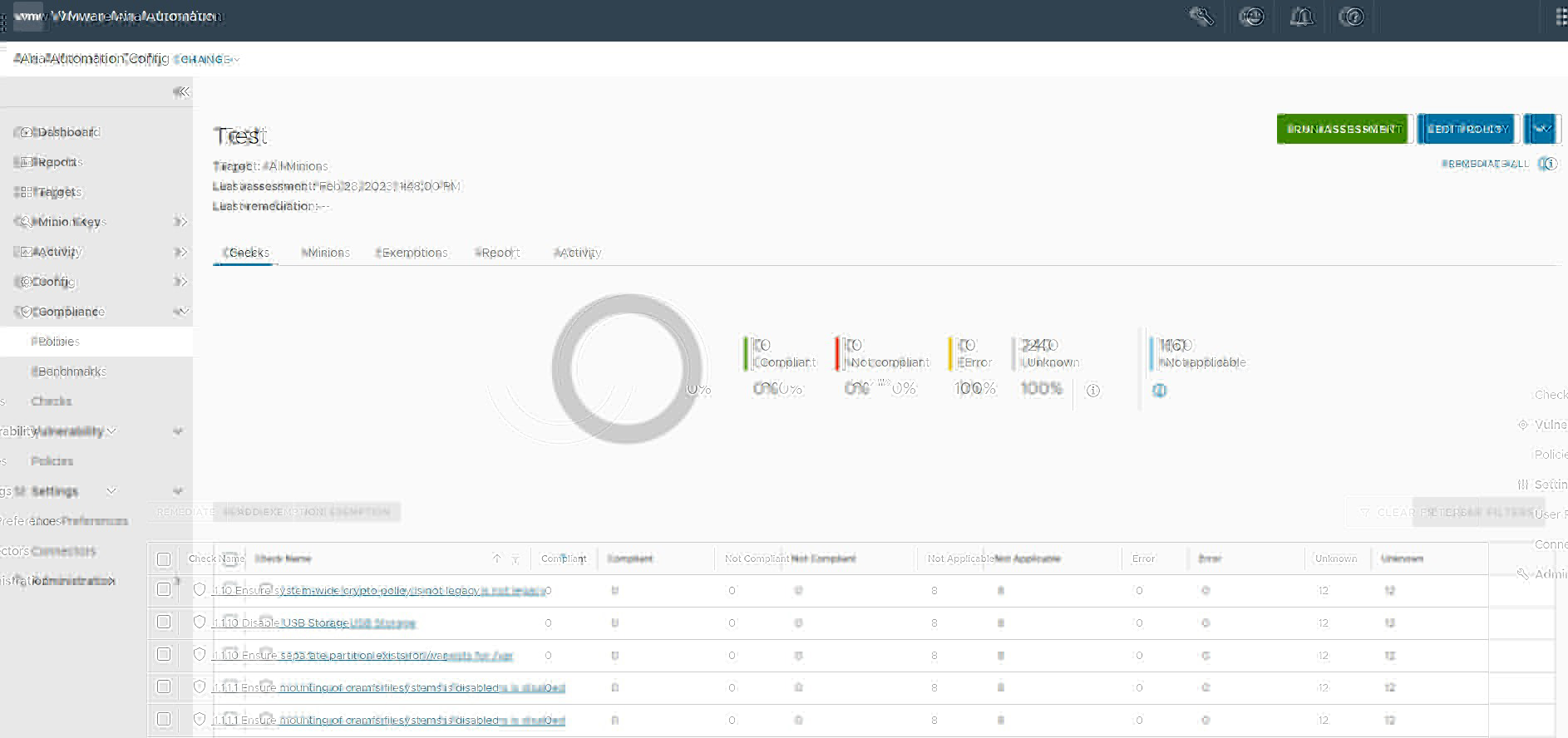
The compliance policy is saved and used to run an assessment. You can edit the policy by selecting the policy from the home page, and clicking Edit Policy.
What to read next
-
Creating and testing custom compliance components
Custom Compliance content allows you to define your own security standards that supplement the library of security benchmarks and checks built into Tanzu Salt.
-
Building your custom content library
After creating your custom checks and benchmarks, you can create a custom content library.