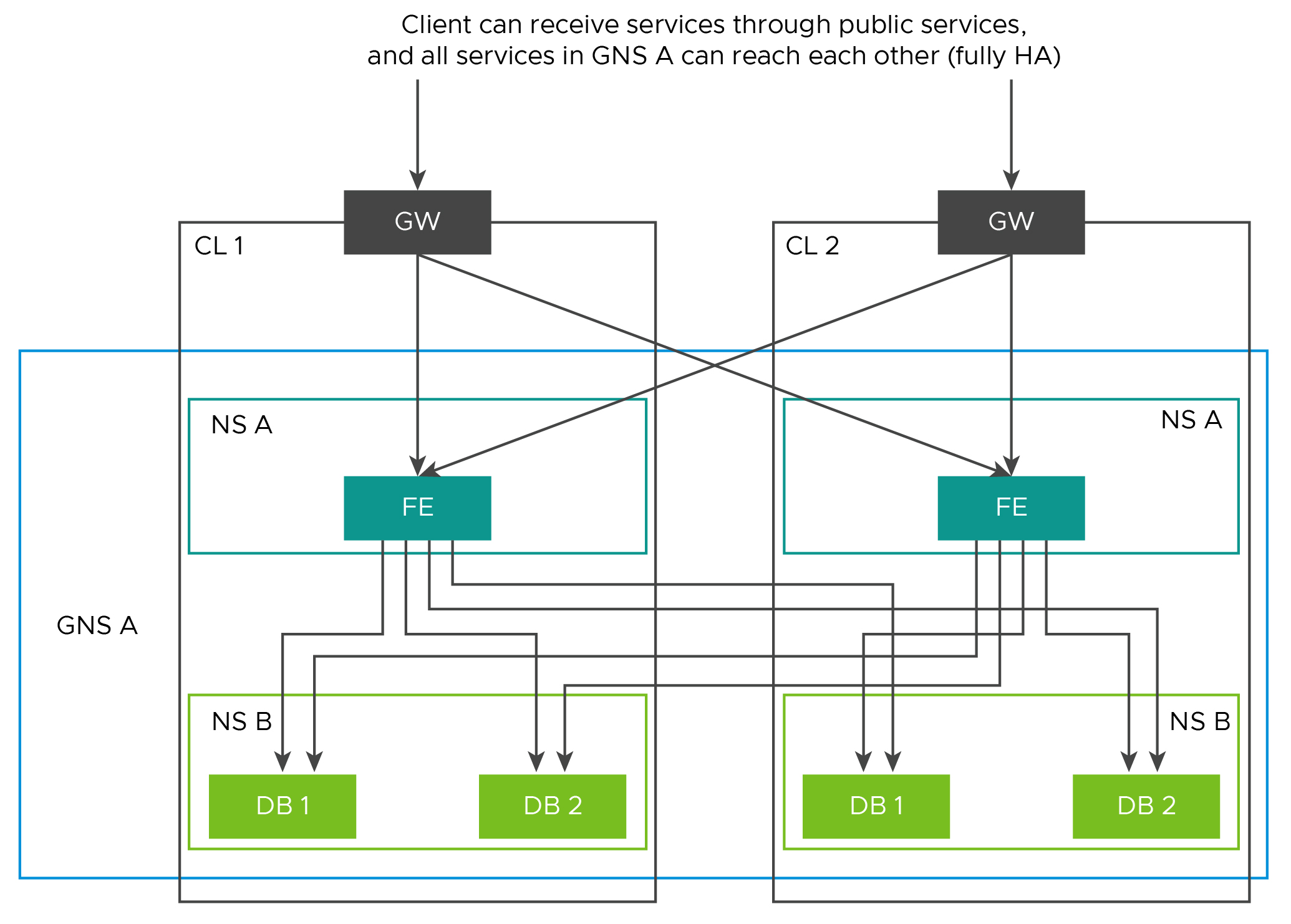
Global namespace, a unique concept in Tanzu Service Mesh, defines an application boundary. A global namespace connects the resources and workloads that make up the application into one virtual unit to provide consistent traffic routing, connectivity, resiliency, and security for applications across multiple clusters and clouds. Each global namespace is an isolated domain that provides automatic service discovery and manages service identities within that global namespace.
A global namespace manages the following functions for all resources that are part of it regardless of where they are located:
Identity. The global namespace defines how a resource can be identified and authenticated to another. Each global namespace has its own certificate authority (CA) that provisions identities for the resources inside that global namespace.
Discovery (DNS). The global namespace controls how one resource can locate another and provides a registry.
Connectivity. The global namespace defines how communication can be established between resources and how traffic within the global namespace and external to the global namespace is routed between resources.
Security. The global namespace manages security for its resources. In particular, the global namespace can enforce that all traffic between the resources is encrypted using Mutual Transport Layer Security authentication (mTLS). For more information, see the section mTLS Encryption in Global Namespaces.
Observability. Tanzu Service Mesh aggregates telemetry data, such as metrics for services, clusters, and nodes, inside the global namespace. Tanzu Service Mesh provides a GraphQL endpoint through which you can query telemetry data. Additionally, you can distribute telemetry data to external endpoints using plugins on your clusters (for example, Wavefront Adapter for Istio).

Global namespaces also offer isolated environments that can be assigned to different teams that manage different applications and data. Teams can use global namespaces to separate services between development, test, or production environments.
Global namespaces decouple your applications from the underlying infrastructure of the container-orchestration system (such as Kubernetes), while providing consistent traffic management and security policies, regardless of where your workloads are running. You can move applications across environments more easily with global namespaces. You can have as many global namespaces as you need, completely decoupled from the underlying clusters.
mTLS Encryption in Global Namespaces
Application operators and security engineers can use global namespaces to encrypt all HTTP and gRPC traffic that travels between services from one or more clusters inside a global namespace, using mTLS. This helps protect data in flight for all traffic within the service mesh for data protection and compliance needs.
Since a global namespace can include services from one or more clusters, Tanzu Service Mesh enforces mTLS end-to-end encryption of all traffic that travels between services within the same cluster or from services in one cluster to services in a different cluster.
You can specify an encryption mode for all global namespaces within your service mesh:
Strict. Only encrypted traffic is allowed (HTTPS only).
Permissive. Plain-text (HTTP) and encrypted (HTTPS) traffic is allowed.
Off. Only plain-text (HTTP) traffic is allowed.
Traffic between global namespaces is always encrypted regardless of the mode.
From the service details page for a specific service, you can see whether mTLS encryption is enabled for that service and which encryption mode is used. The service graph in the console shows whether mTLS is configured for the application running in the global namespace.
For more information about how Tanzu Service Mesh supports the use case of encrypting in-flight data, see Encryption for Data in Flight.
Multiple Namespace Support in a Single Global Namespace
Application operators can onboard their applications in a kubernetes namespace into a global namespace. Tanzu Service Mesh enables users to select one or more namespaces (multiple namespaces) from a Kubernetes cluster and add them to a global namespace.
Multiple namespace feature of Tanzu Service Mesh supports public service and cross cluster routing; however, traffic management, SLOs and autoscaling are not supported.
GNS multinamespaces provide the following capabilities:
The deployment of an application can be done on a single cluster or across multiple clusters.
It is possible to select services from multiple namespaces to be published as public services.
Access control policies can be defined for these services.
With a multinamespace GNS, you can also use features supported by GNS.
Global Namespace allows you to onboard external services, and internal services should be able to connect to them.