Virtual machines are the logical containers in which applications and guest operating systems run. By design, all VMware virtual machines are isolated from one another. This isolation enables multiple virtual machines to run securely while sharing hardware, and provides both their ability to access hardware and their uninterrupted performance.
Even a user with system administrator privileges on a virtual machine's guest operating system cannot breach this layer of isolation to access another virtual machine without privileges explicitly granted by the ESXi system administrator. As a result of virtual machine isolation, if a guest operating system running in a virtual machine fails, other virtual machines on the same host continue to run. Users can still access other virtual machines, and the performance of other virtual machines is not affected.
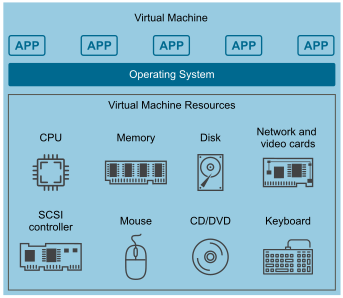
Each virtual machine is isolated from other virtual machines running on the same hardware. Although virtual machines share physical resources such as CPU, memory, and I/O devices, a guest operating system on an individual virtual machine can only detect the virtual devices that you make available to it.
The VMkernel mediates all physical resources. All physical hardware access takes place through the VMkernel and virtual machines cannot circumvent this level of isolation.
Just as a physical machine communicates with other machines in a network through a network card, a virtual machine communicates with other virtual machines running on the same host through a virtual switch. Further, a virtual machine communicates with the physical network, including virtual machines on other ESXi hosts, through a physical network adapter.
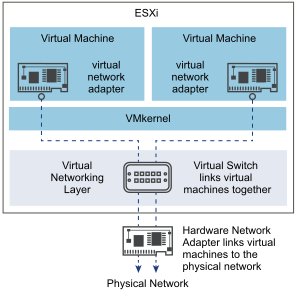
Virtual networking is also affected by virtual machine isolation.
If a virtual machine does not share a virtual switch with any other virtual machine, it is completely isolated from virtual machines within the host.
If no physical network adapter is configured for a virtual machine, the virtual machine is completely isolated. This includes isolation from any physical or virtual networks.
Virtual machines are as secure as physical machines if you protect them from the network with firewalls, antivirus software, and so on.
You can further protect virtual machines by setting up resource reservations and limits on the host. For example, you can use resource allocation to configure a virtual machine so that it always receives at least 10 percent of the host's CPU resources, but never more than 20 percent.
Resource reservations and limits protect virtual machines from performance degradation that might result if another virtual machine consumed excessive shared hardware resources. For example, if one of the virtual machines on a host is incapacitated by a denial-of-service (DoS) attack, a resource limit on that machine prevents the attack from taking up so much of the hardware resources that the other virtual machines are also affected. Similarly, a resource reservation on each of the virtual machines ensures that in the event of high resource demands by the virtual machine targeted by the DoS attack, all the other virtual machines have enough resources to operate.
By default, ESXi imposes a form of resource reservation by applying a distribution algorithm that divides the available host resources equally among the virtual machines while keeping a certain percentage of resources for use by other system components. This default behavior provides a degree of natural protection from DoS and distributed denial-of-service (DDoS) attacks. Specific resource reservations and limits are set on an individual basis to customize the default behavior so that the distribution is not equal across the virtual machine configuration.