Automation for Secure Hosts is a compliance and vulnerability management application that can automate security remediation.
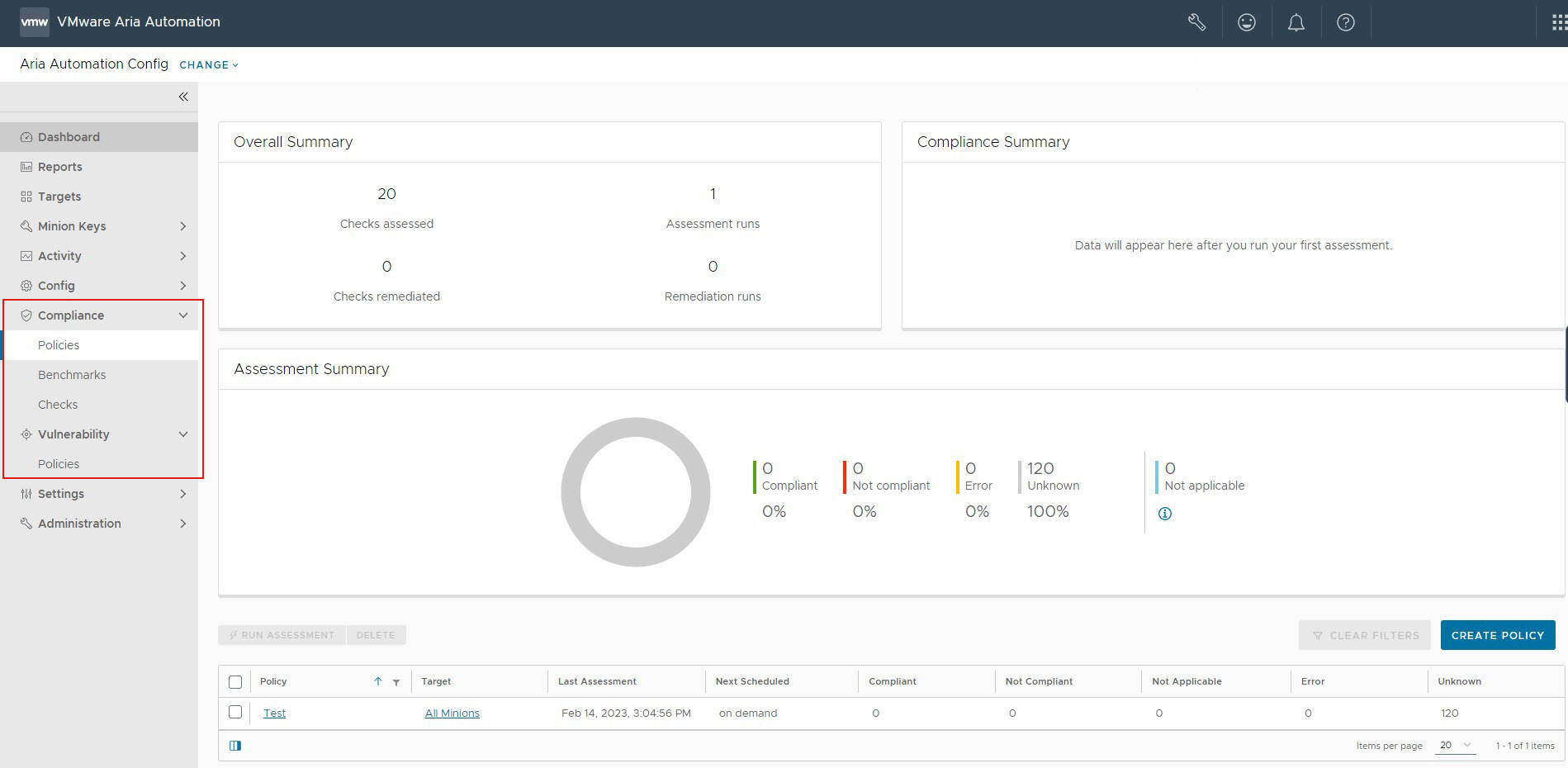
Automation for Secure Hosts allows you to scan your system for compliance against various security benchmarks, detect system vulnerabilities, and remediate your results. Automation for Secure Hosts includes both Automation for Secure Hosts Compliance and Automation for Secure Hosts Vulnerability services.
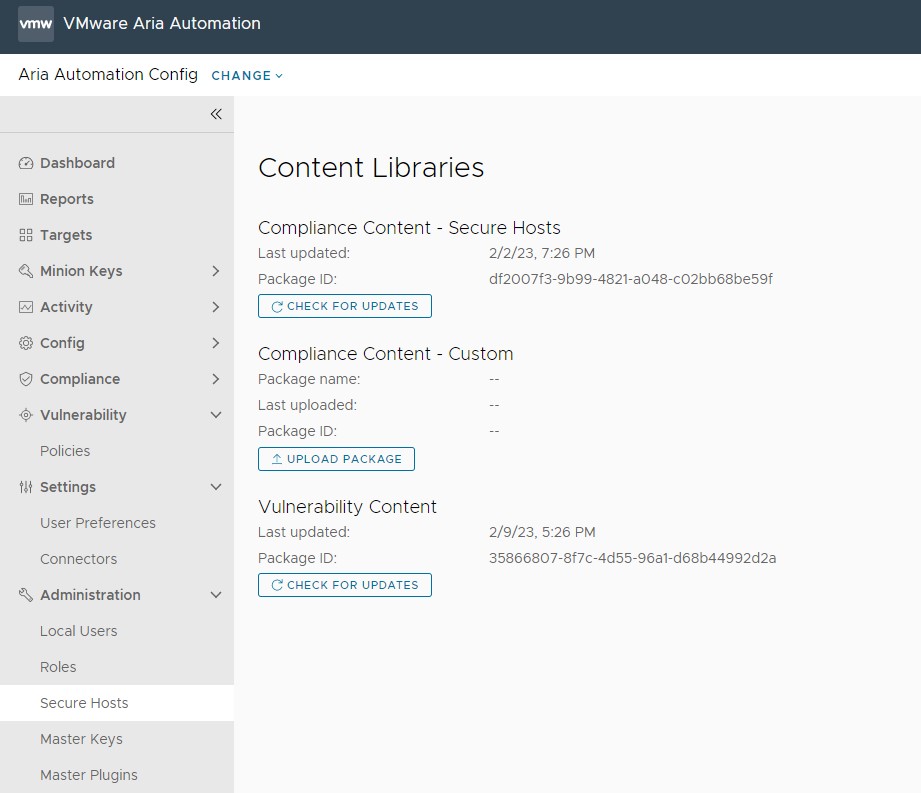
- Compliance Content Library - Built-in security content
- Compliance Content Custom Library - Custom checks and benchmarks defined and uploaded by your organization.
Automation for Secure Hosts Vulnerability scans your system for common vulnerabilities and exposures (CVEs), and then remediates any identified advisories. It includes a built-in advisories vulnerability library.
Content libraries are updated regularly as security standards change. You can also configure content to download automatically as updates become available, or download content manually. To manually check for updates and download content, click and click either Check for Updates or Upload Package underneath the desired content library.