This section explains the NSX Advanced Load Balancer DNS features.
Visibility and Analytics
Navigate to and click the name of a virtual service configured for DNS. Click the pencil icon to view analytics, logs, health, security, events, alerts, and DNS records details.
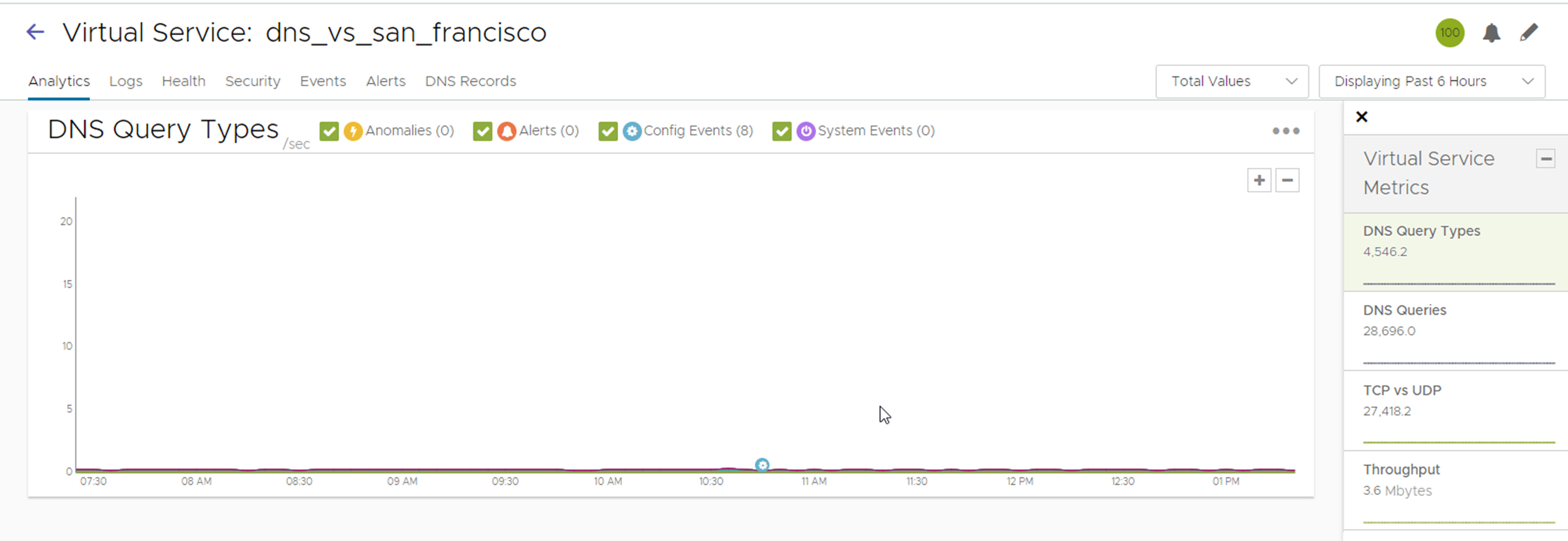
The Analytics tab displays the required metrics.
The Logs tab provides detailed information about DNS queries from clients, including FQDN, query-type, significant errors, responses such as IP addresses, CNAME, SRV, and so on.
Non-significant logs must be enabled with caution, since a large number of DNS queries typically reach a DNS service, and this would result in too many logs entries.
Categorization of non-significant logs is also very important. If certain errors are typical in a certain deployment, these errors must be excluded from significant logs.
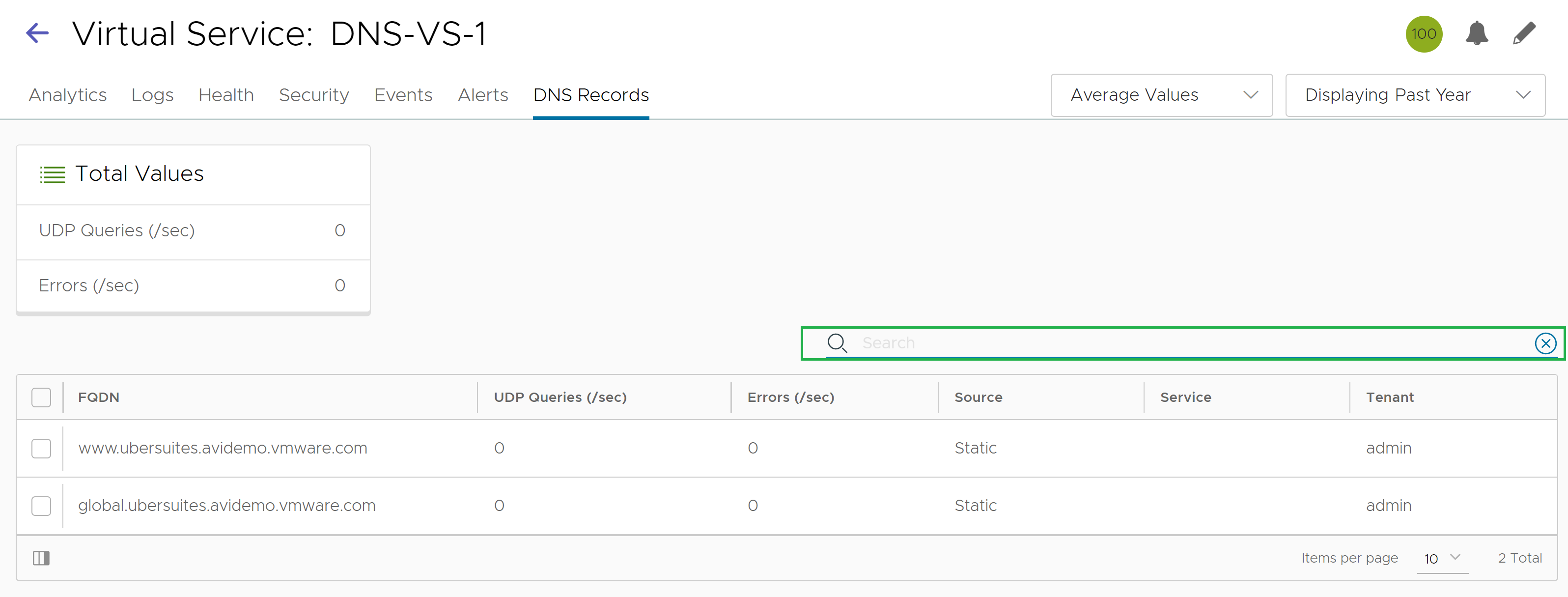
The DNS Records tab is unique to this kind of a virtual service.
DNS health monitors in Health tab can be configured to monitor the health of DNS servers that are configured as DNS service pool members. For complete information, see DNS Health Monitor section.
Detailed analytics is not available for TCP.
DNS requests can be filtered by sub-domain name.
NO-DATA may occasionally appear when a metric tile is selected. This typically implies “Not Applicable”. For instance, a GSLB service name may not be applicable for the DNS proxy or a static entry.
DNS Record Search Option
Starting with NSX Advanced Load Balancer 22.1.3, the option to search DNS records for a DNS virtual service is available on the NSX Advanced Load Balancer UI. This option is useful when multiple records are present and it becomes difficult to find the specific entry and check if it is registered and receiving requests.
Additional Features
The following are the additional features:
Domain filtering drops requests for any domains that are not explicitly configured on the DNS service (Default setting is to allow all domains).
The time-to-live (TTL) can be customized (Default is 30 seconds).
Network security policy can be based on client (source) IP and port.
With full TCP proxy, client spoofing is prevented for TCP DNS queries. SYN flood attacks are mitigated.
You can respond to failed DNS requests by returning a DNS error code or dropping the packets.