Remote Auth requires the assignment of roles and tenants for every user login through the authorization mapping rules. Authorization is assessed on every login, and the user record is updated. Upon successful user login through an external authentication server, all mapping rules are evaluated.Tenant and role pairs are added to the user access list.
NSX Advanced Load Balancer supports user profile mapping for remote users.
Configuring Remote Authentication
By default, a Controller will have only local authentication established (Authentication/Authorization: Local).
To configure remote authentication using the NSX Advanced Load Balancer UI, follow the steps below:
Navigate to .
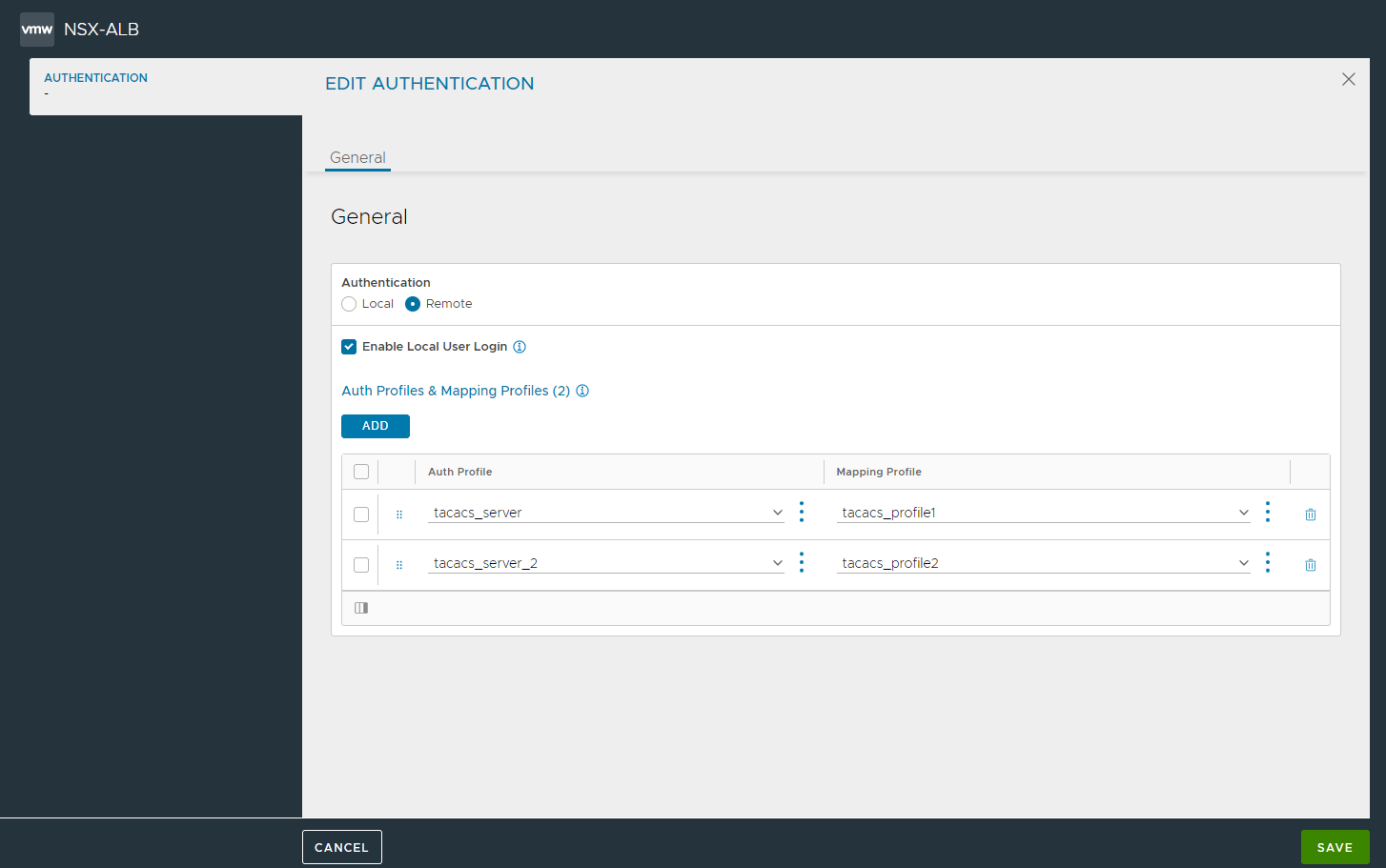
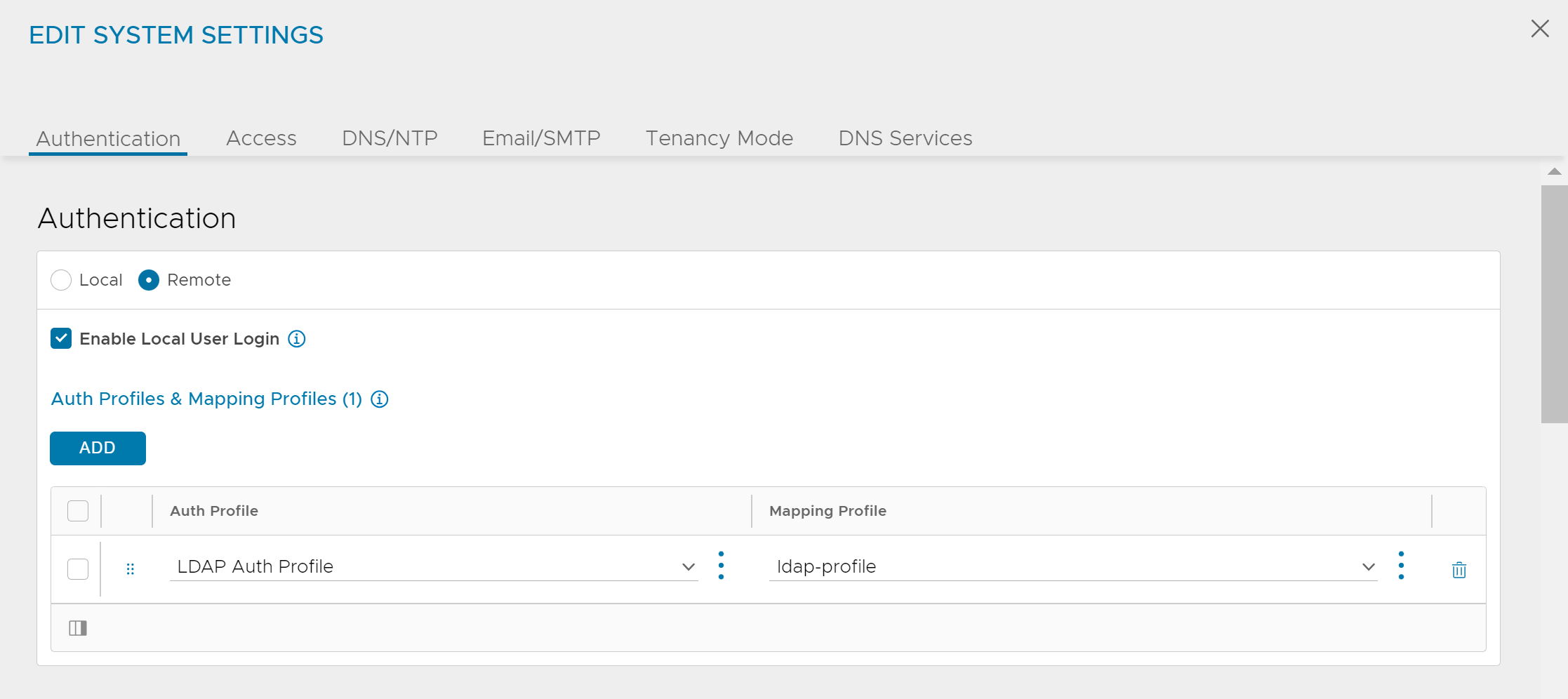
In the Edit System Settings screen, select Remote as the Authentication method.
Select Enable Local User Login to allow users from the local user database to log in with their user credentials.
Under Auth Profiles & Mapping Profiles, click Add.
From the Select Auth Profile, select an existing remote auth profile or click the vertical menu icon (three dots) to create a new auth profile.
Click Save.
Tenant and role mapping are available only with remote authentication.
Multiple remote authentication profiles can be configured using the NSX Advanced Load Balancer UI under the following conditions:
Any number of auth profiles (more than 2) can be created provided they are of the same type. Consider the following examples to understand this further:
Profile Types
Result
Reason
TACACS
TACACS
TACACS
Successful
All profiles are of the same type
TACACS
TACACS
LDAP
Fails with an error
All the profiles are not of the same type
If there are only two auth profiles configured,
The primary auth profile has to be SAML auth profile.
Both profiles cannot be SAMl. So if SAML is the first auth profile, then the second profile has to be any profile other than SAML
Consider the following examples to understand this further:
Primary Auth Profile |
Secondary Auth Profile |
Result |
Reason |
|---|---|---|---|
SAML |
LDAP |
Successful |
The primary and the secondary profiles are of different types. |
SAML |
SAML |
Fails with an error |
The primary and secondary profiles are both of type SAML. |
LDAP |
TACACS |
Fails with an error |
The primary auth profile is not of type SAML. |
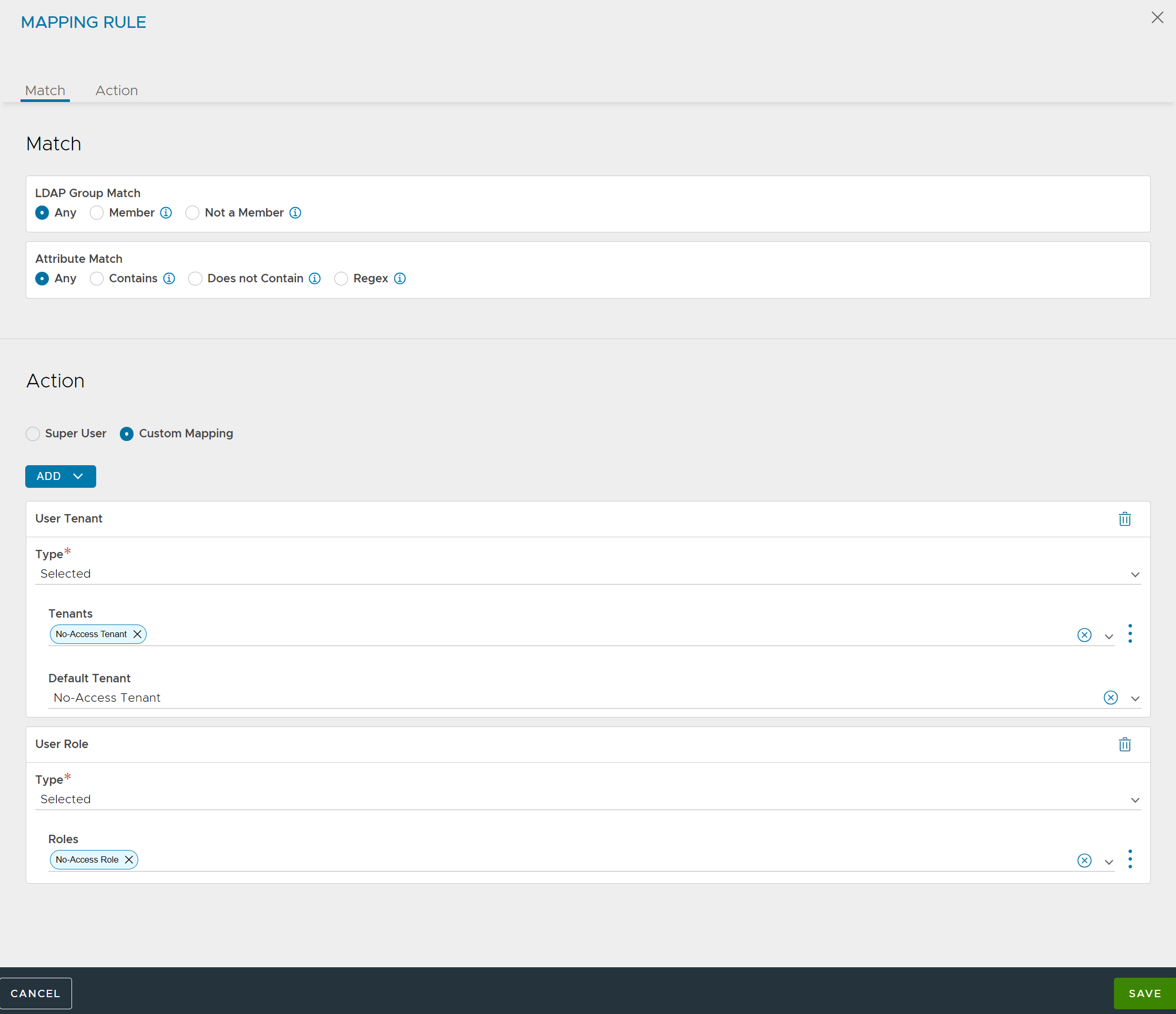
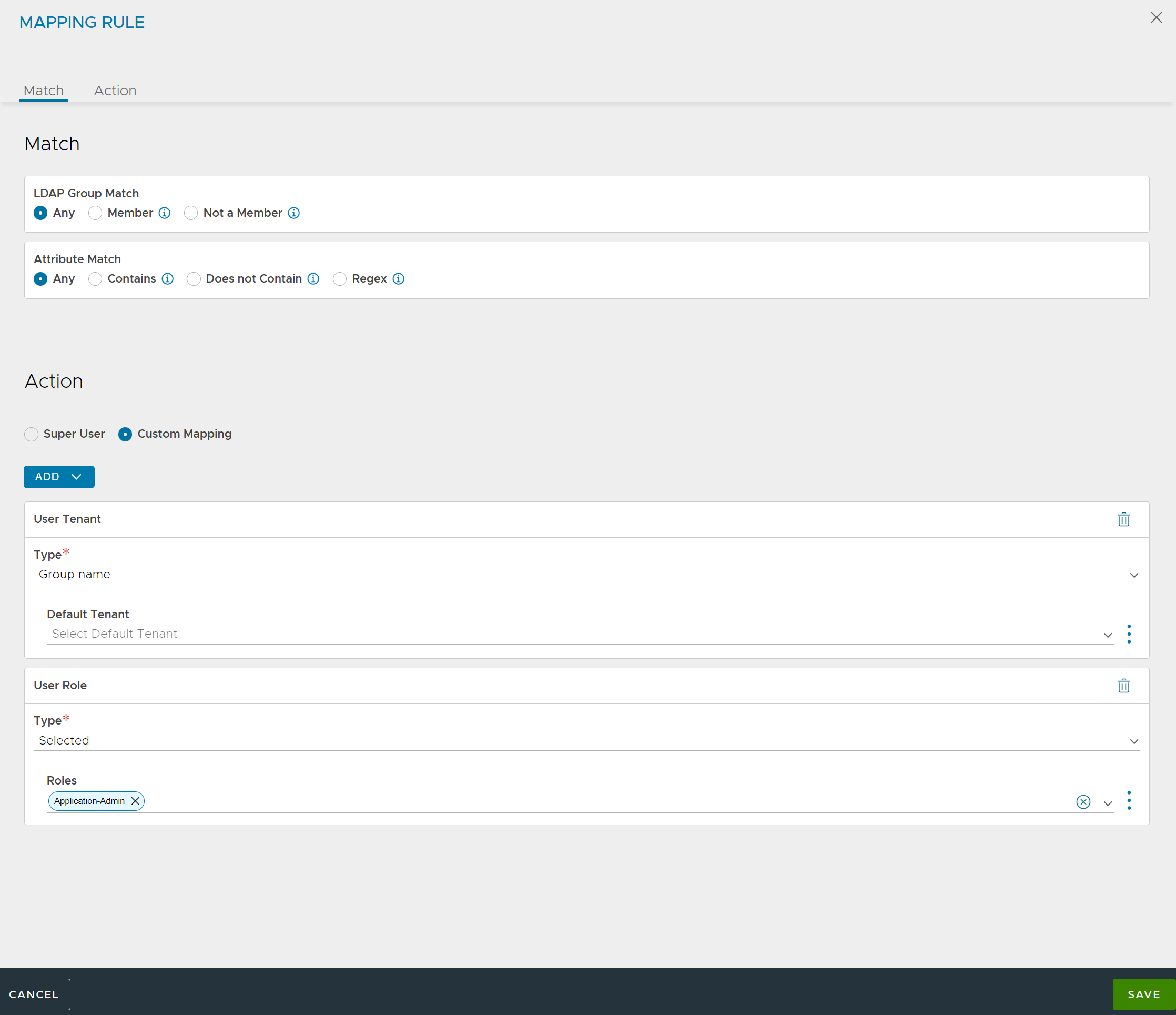
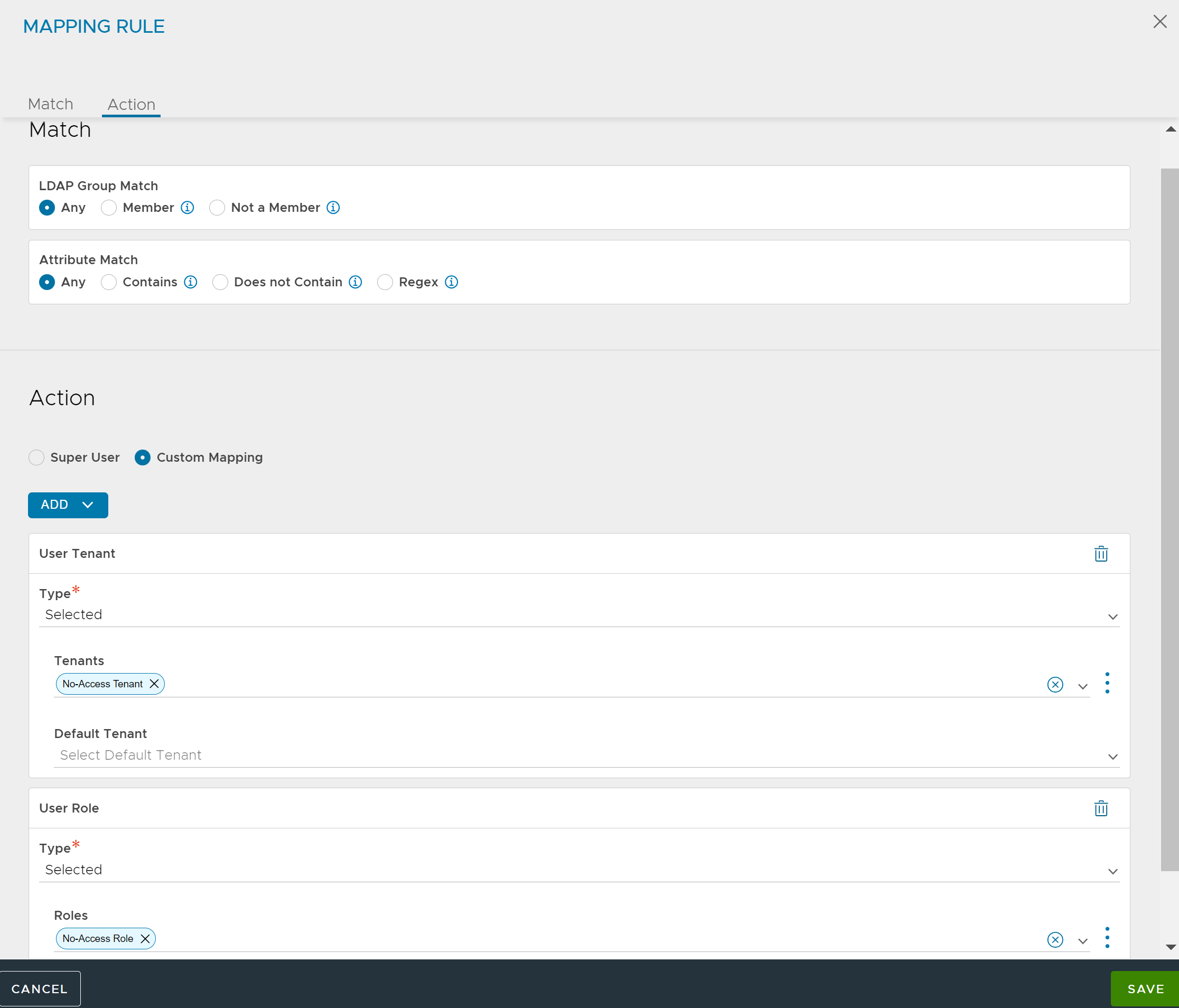
Any Group or Any Attribute Rule
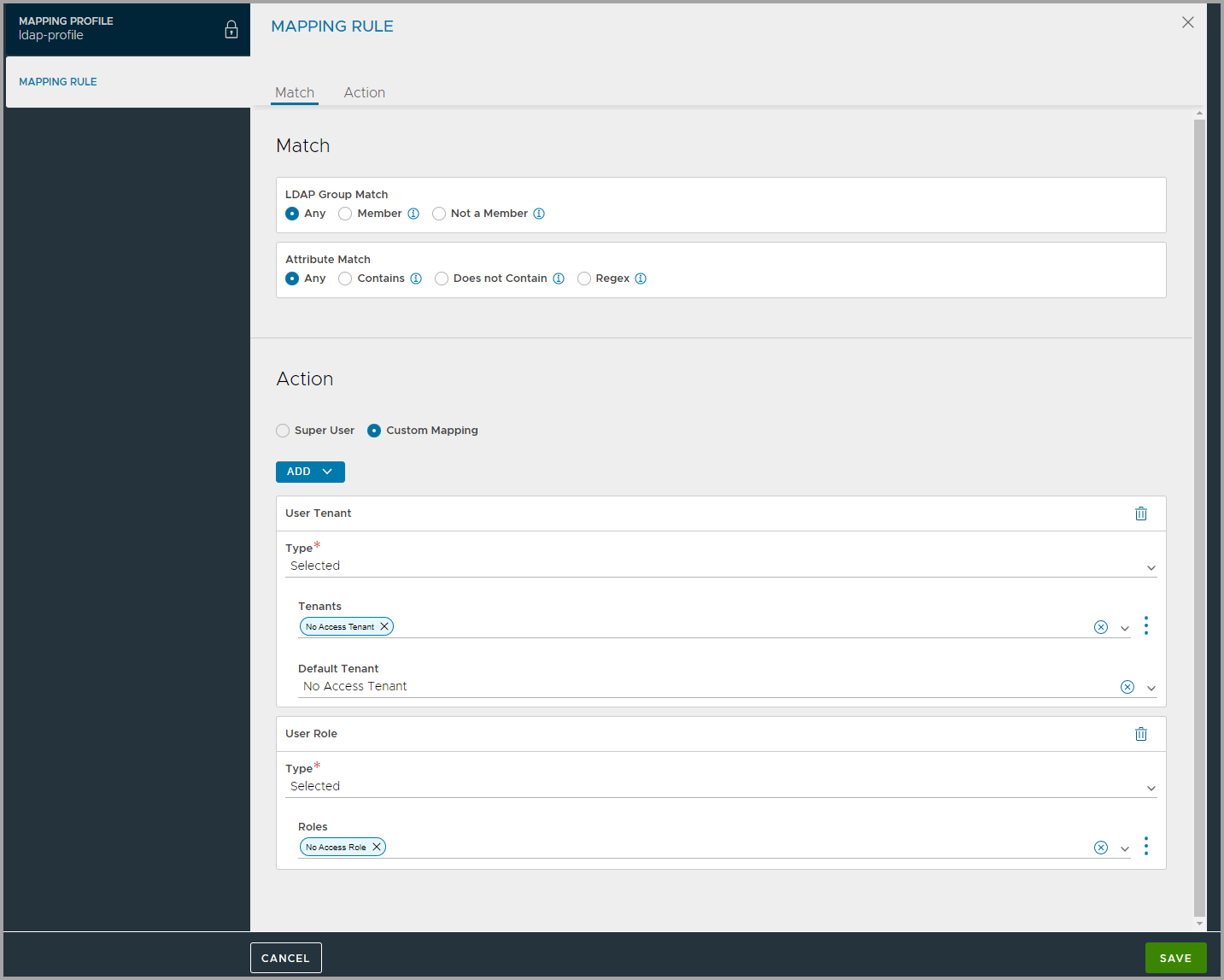
A rule with any group or any attribute applies to all users and can be used as a default option. The rule assigns every user to a least-privileged role and tenant.
The role and tenant need to configured to allow only the least privileges.
If the user is not assigned additional roles or tenant pairs, the least privileged access will take effect after login.
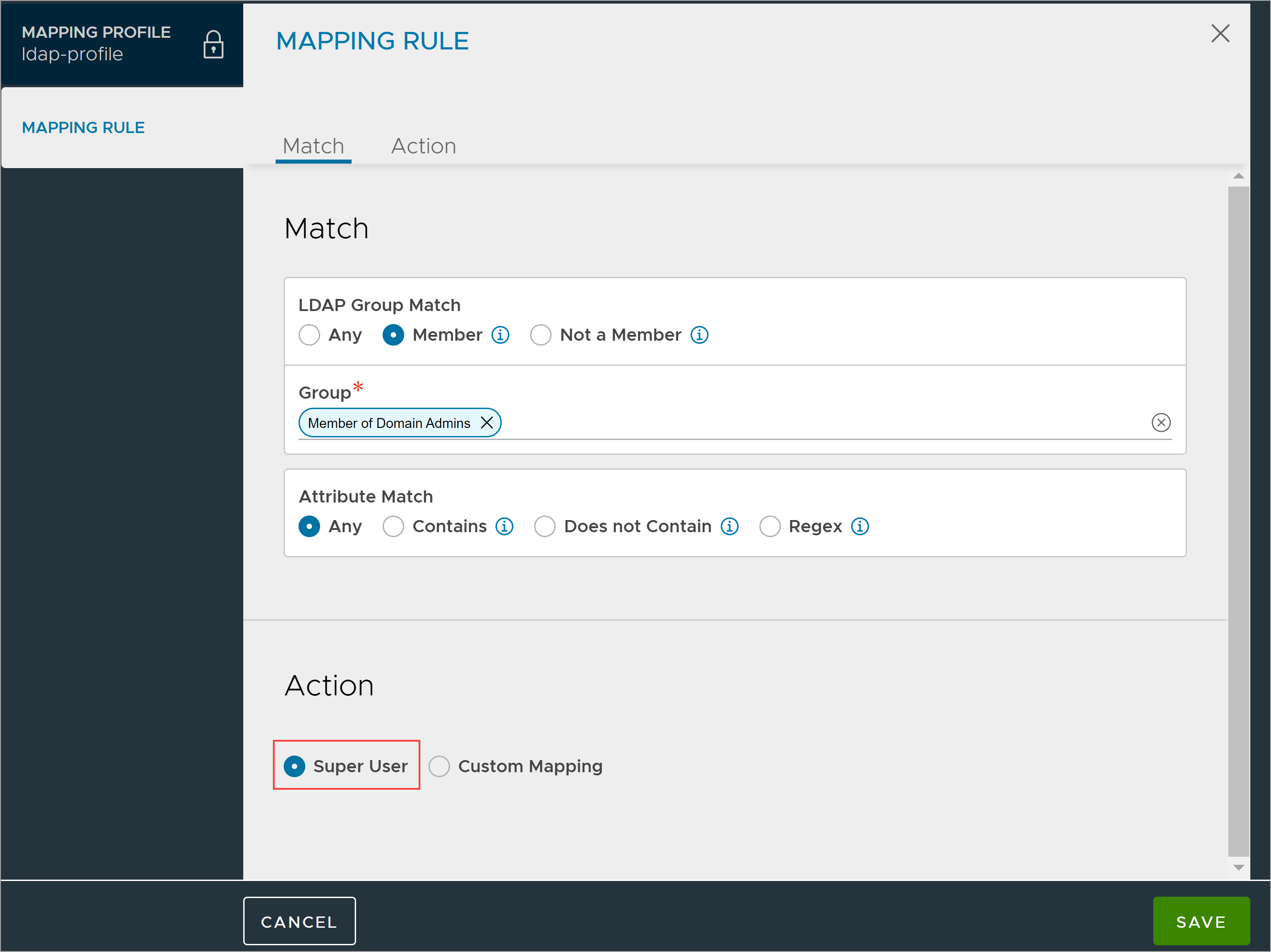
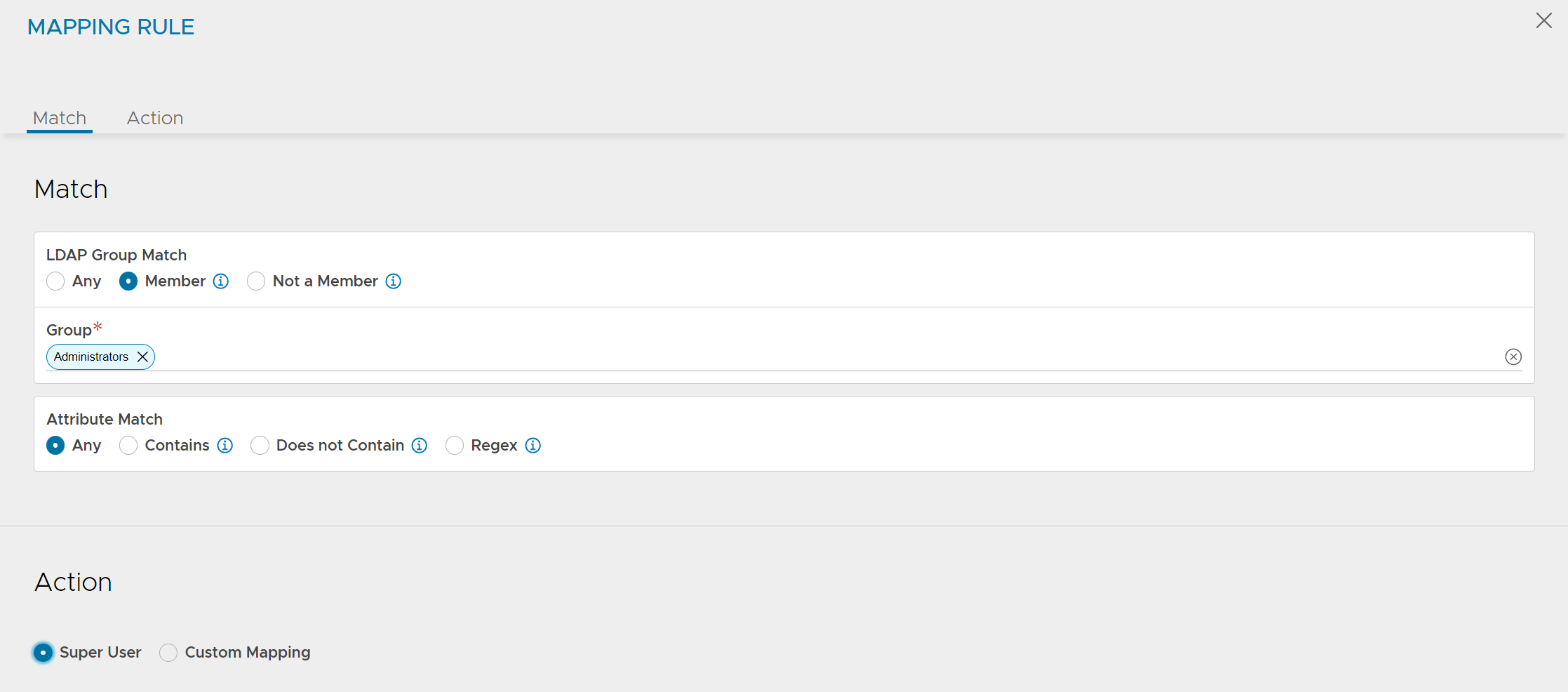
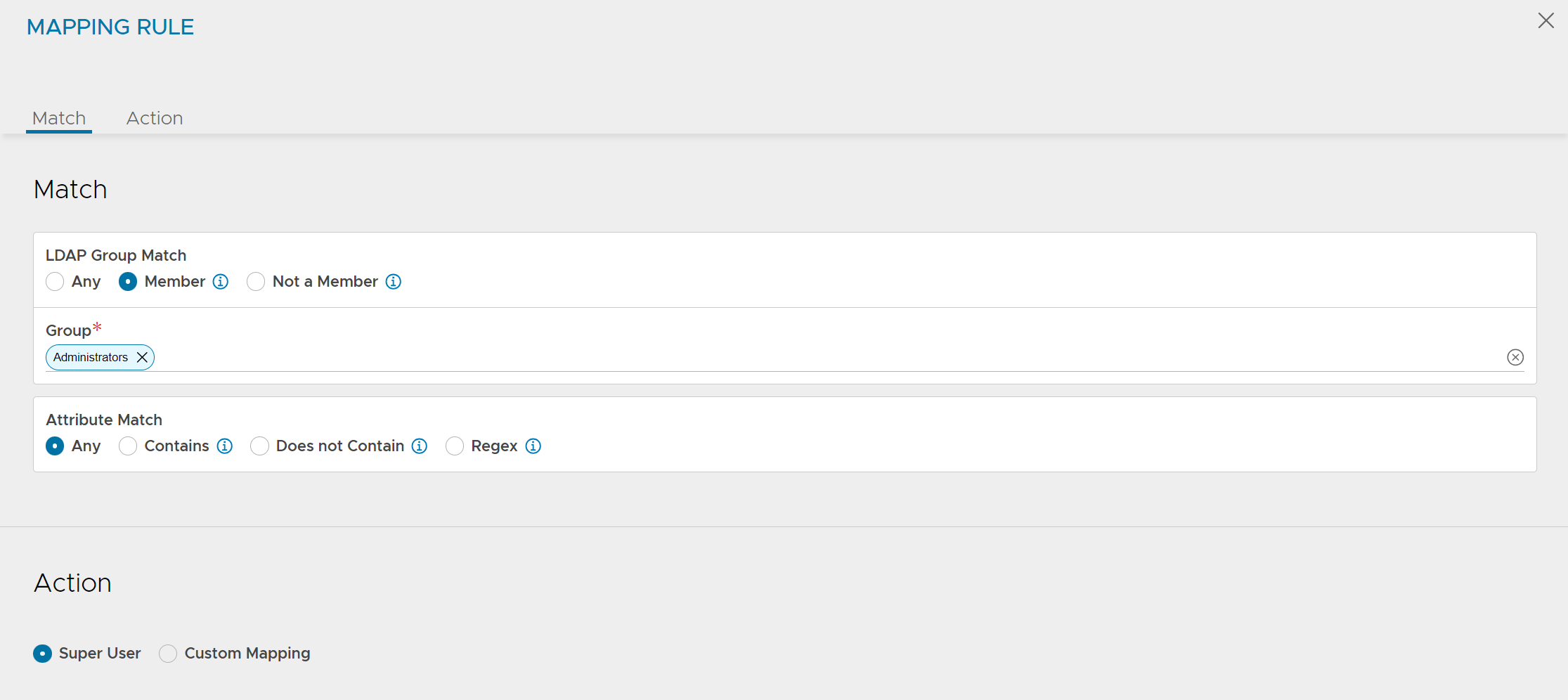
Super User Rule
A rule can be configured to assign Super User privileges to a user. This user will have access to all tenants with the most privileged role. Once a user is super user, no other tenant or role mapping assignments will make a difference to the user’s access.
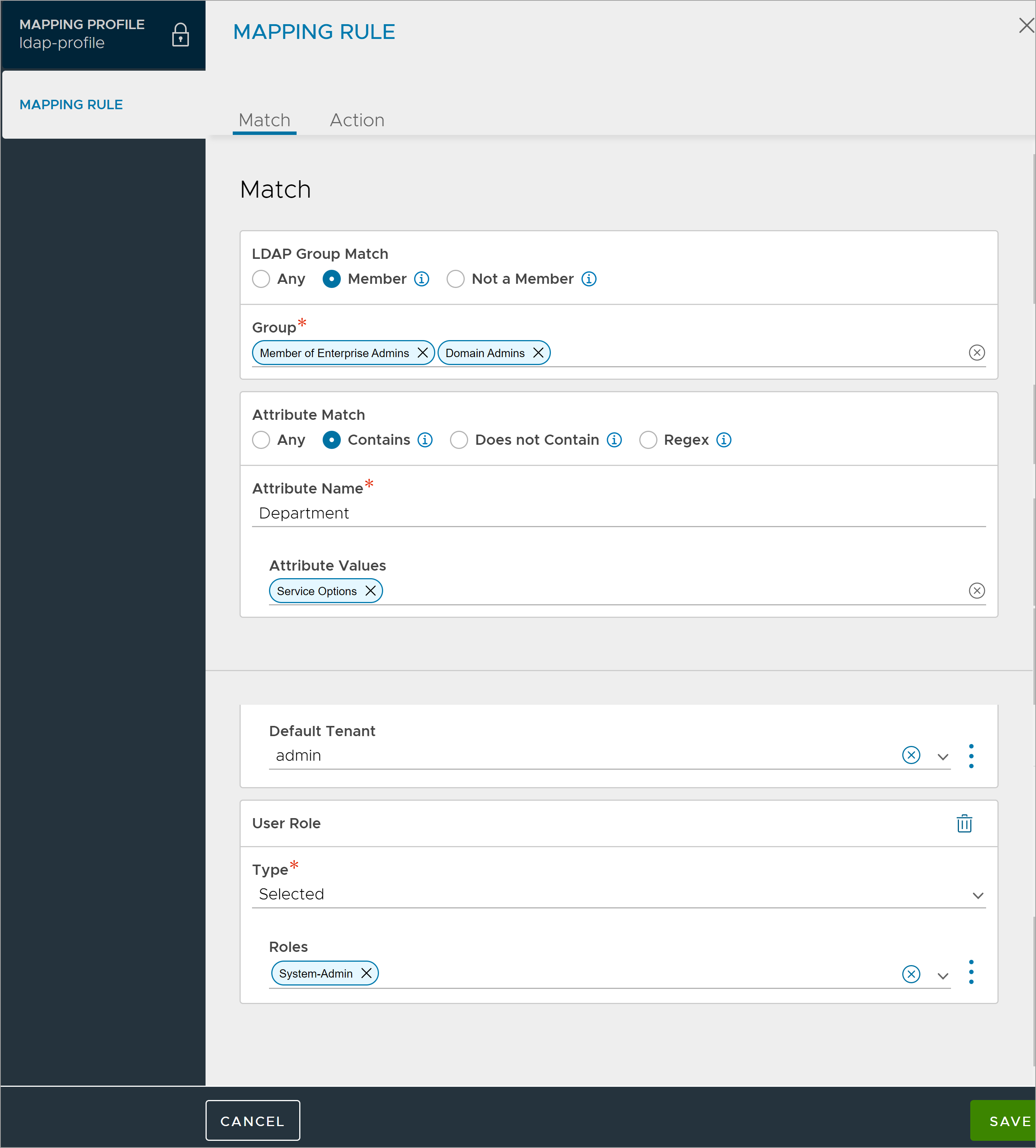
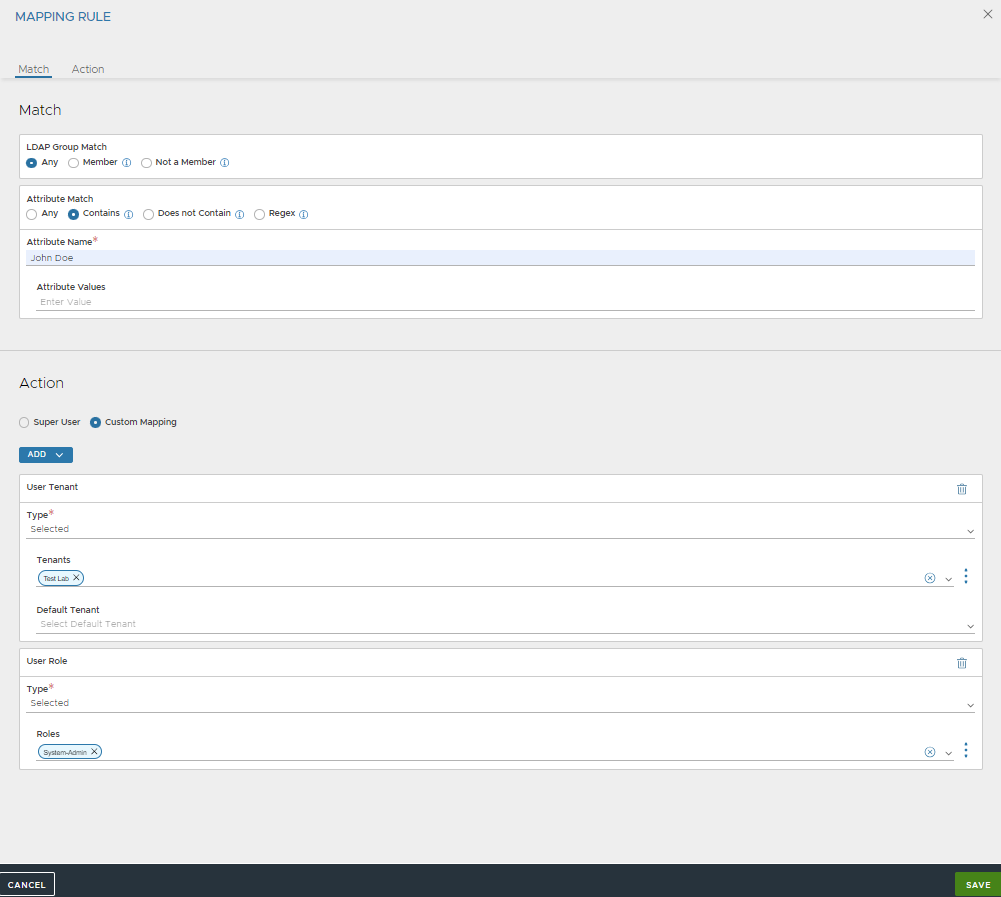
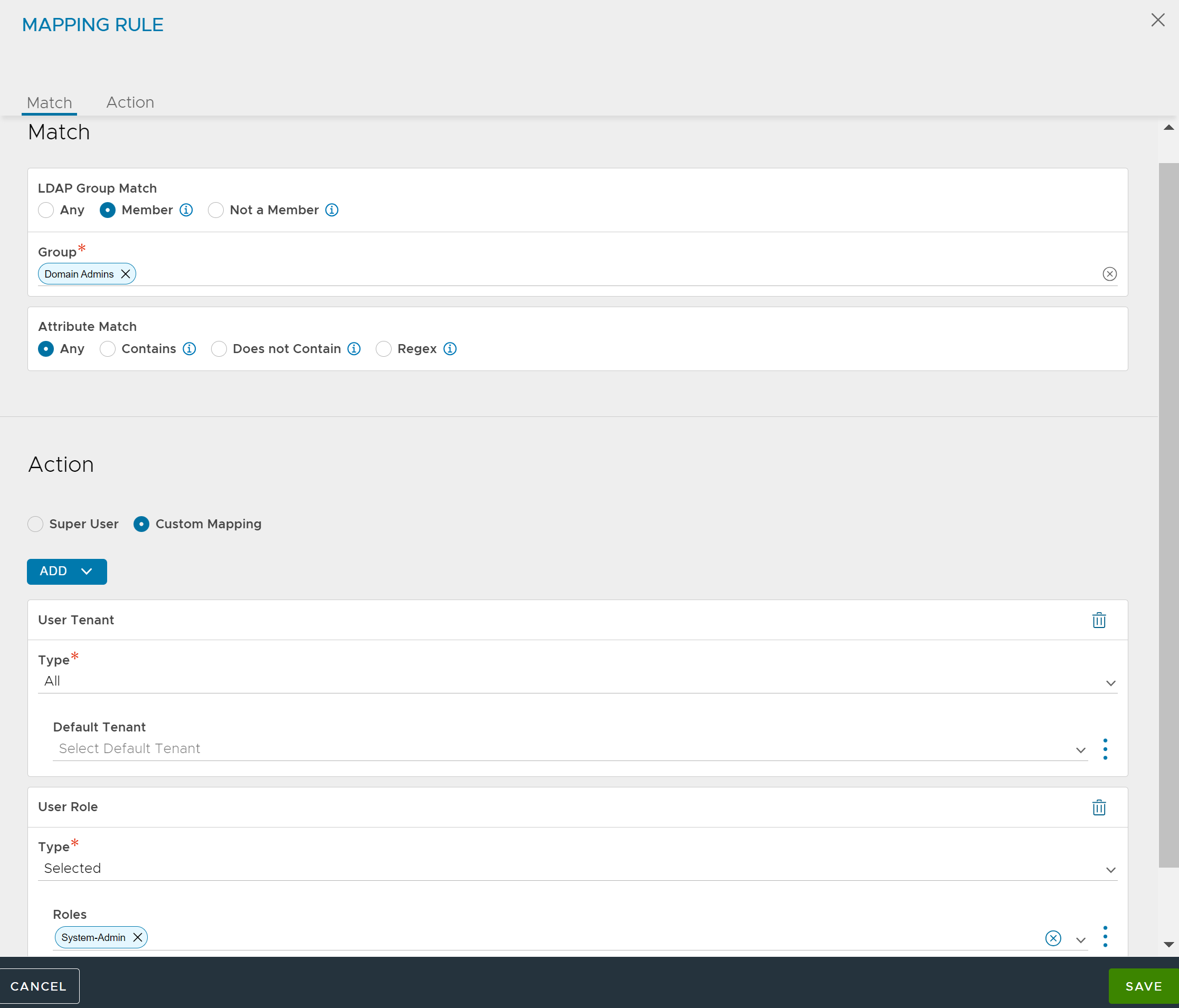
Attribute and Group Match
A mapping rule can be required to match both an attribute and group requirement. It will ensure a more specific assignment of role(s) and tenant(s).
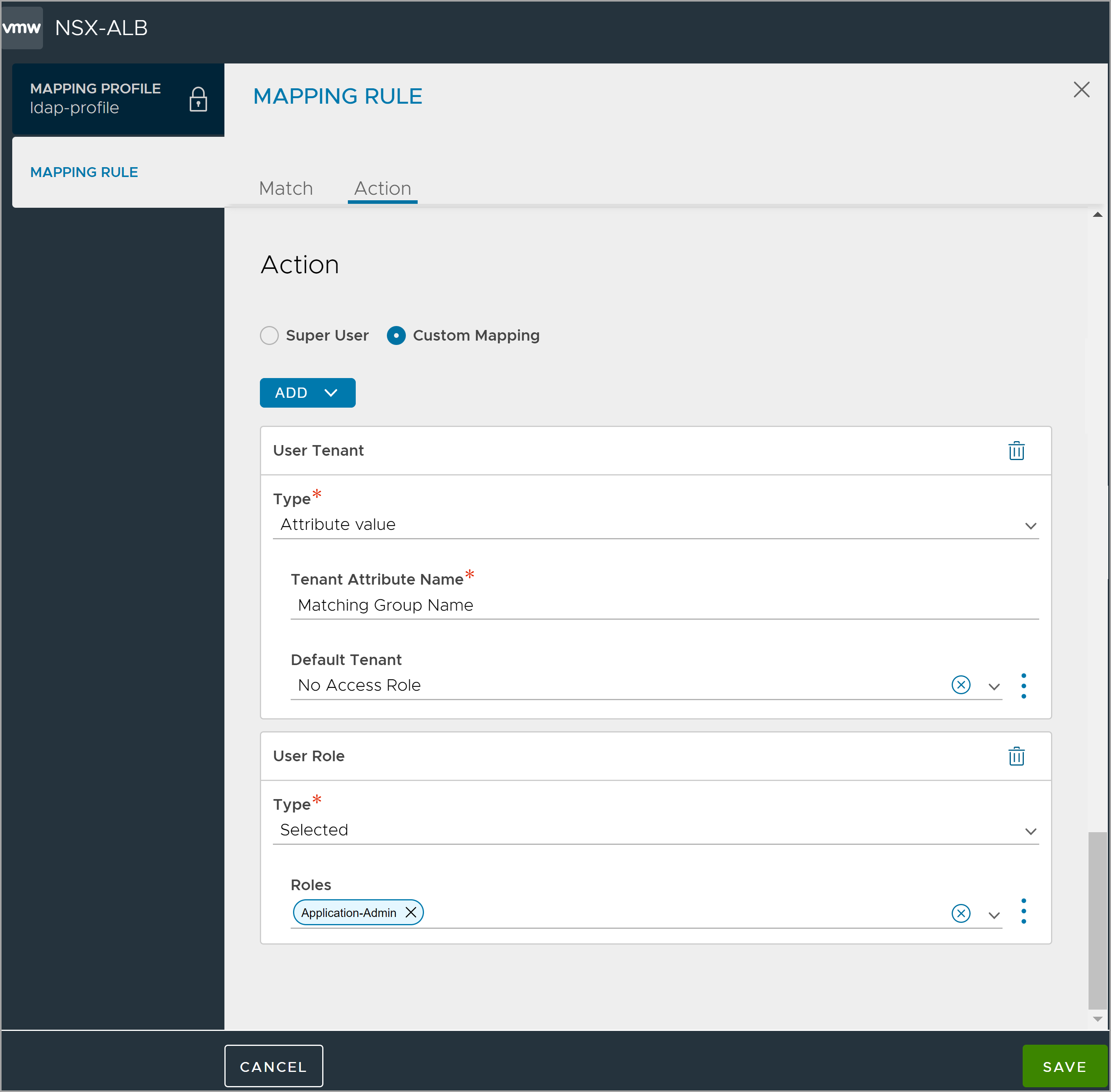
Assign Matching Attribute Values
LDAP/TACACS+ attribute vantageRole for a user can have one or more values. For each value, if there is a configured role with the same name, the role is assigned to the user with access to all tenants. A user session can end up with multiple roles, and the most privileged role will take effect.
Assign Matching Group Names
A user can be a member of multiple LDAP or AD groups. For each group, if there is a configured tenant, the user will be given access to the tenant with any other tenants the user might already have obtained access to using matching rules.
Configuring Default Tenant for Remote Users
When configuring auth mapping rules, you can now select default tenants. When a remote user is created, the tenant selected will be used as the default tenant.
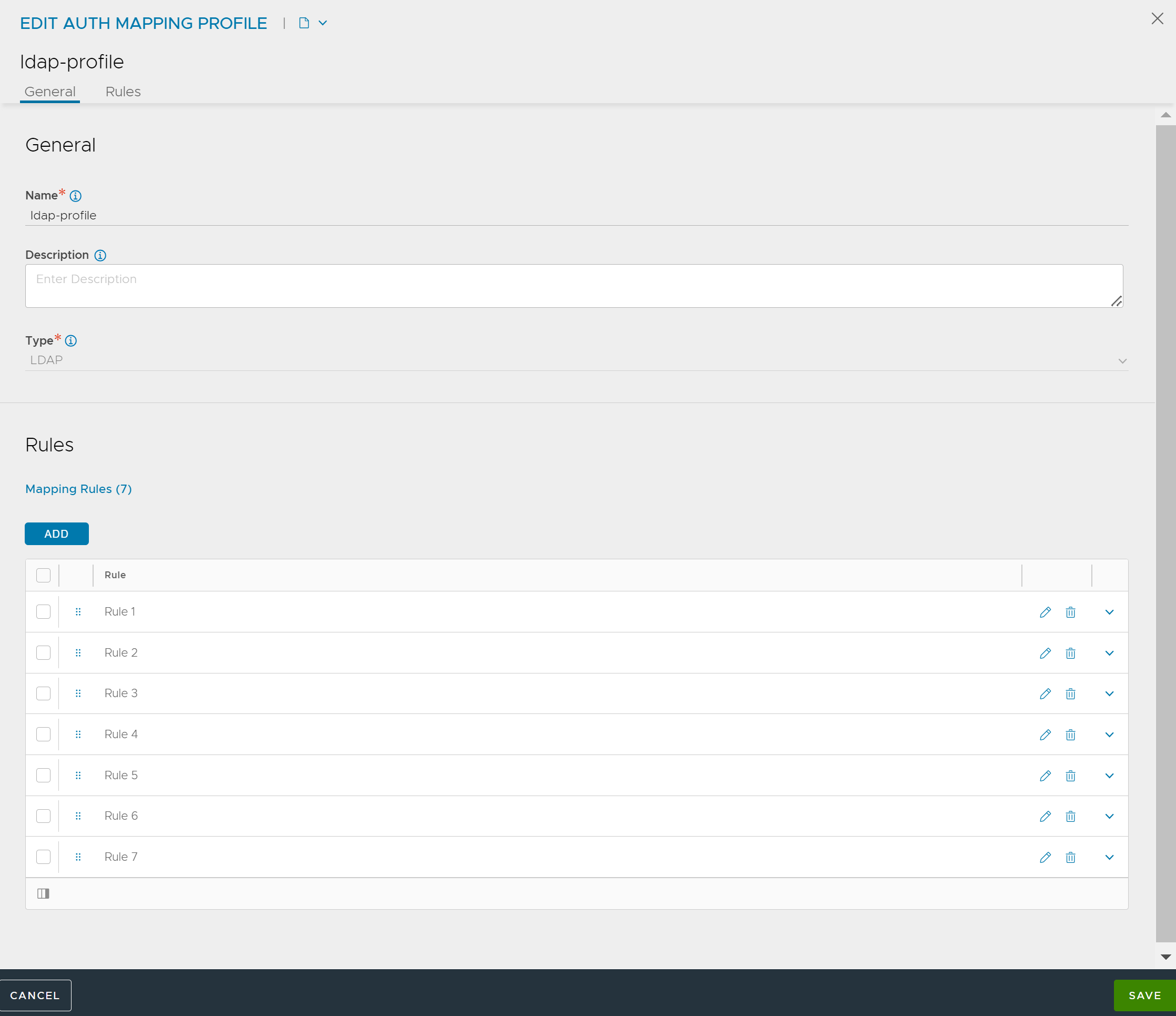
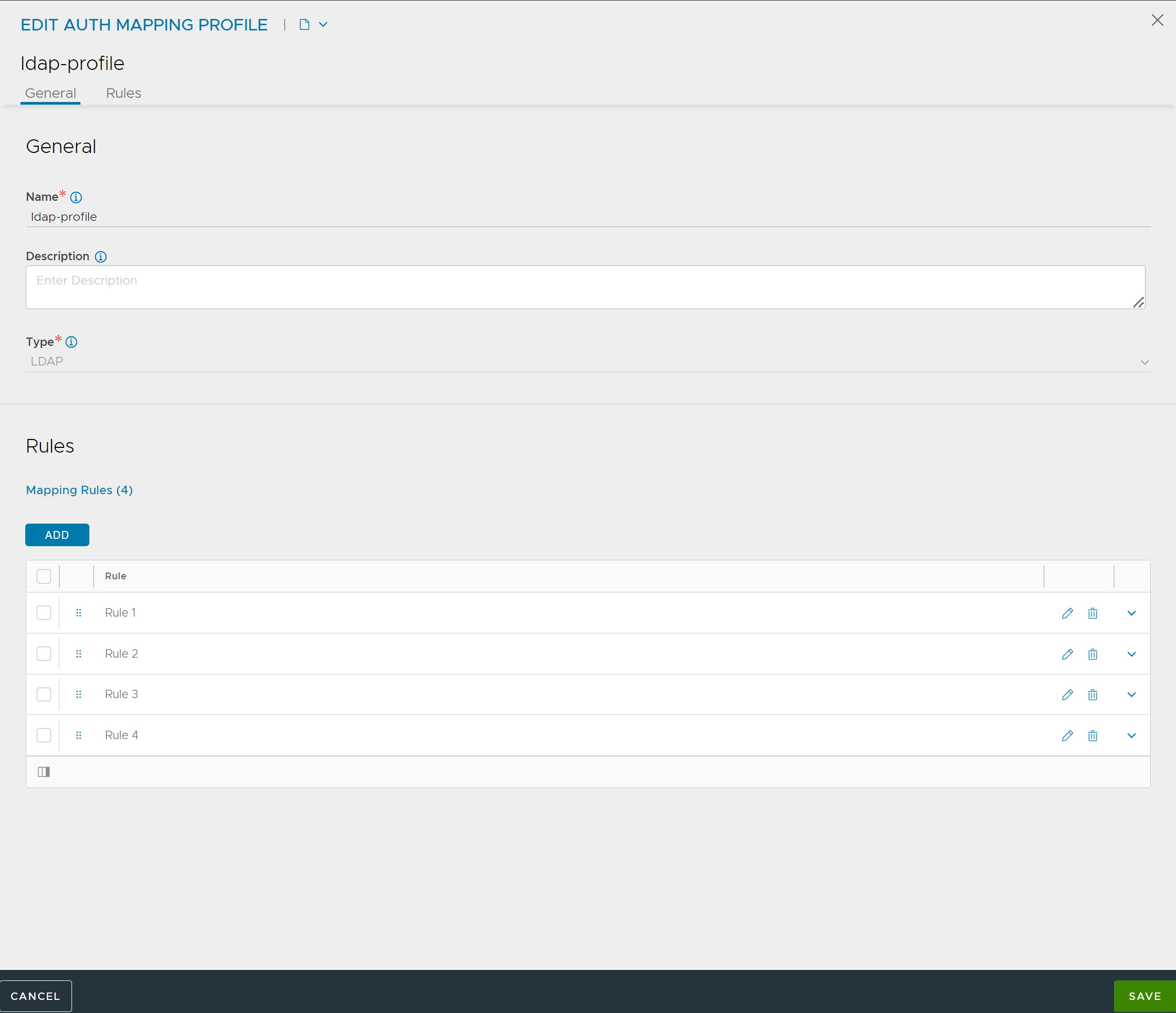
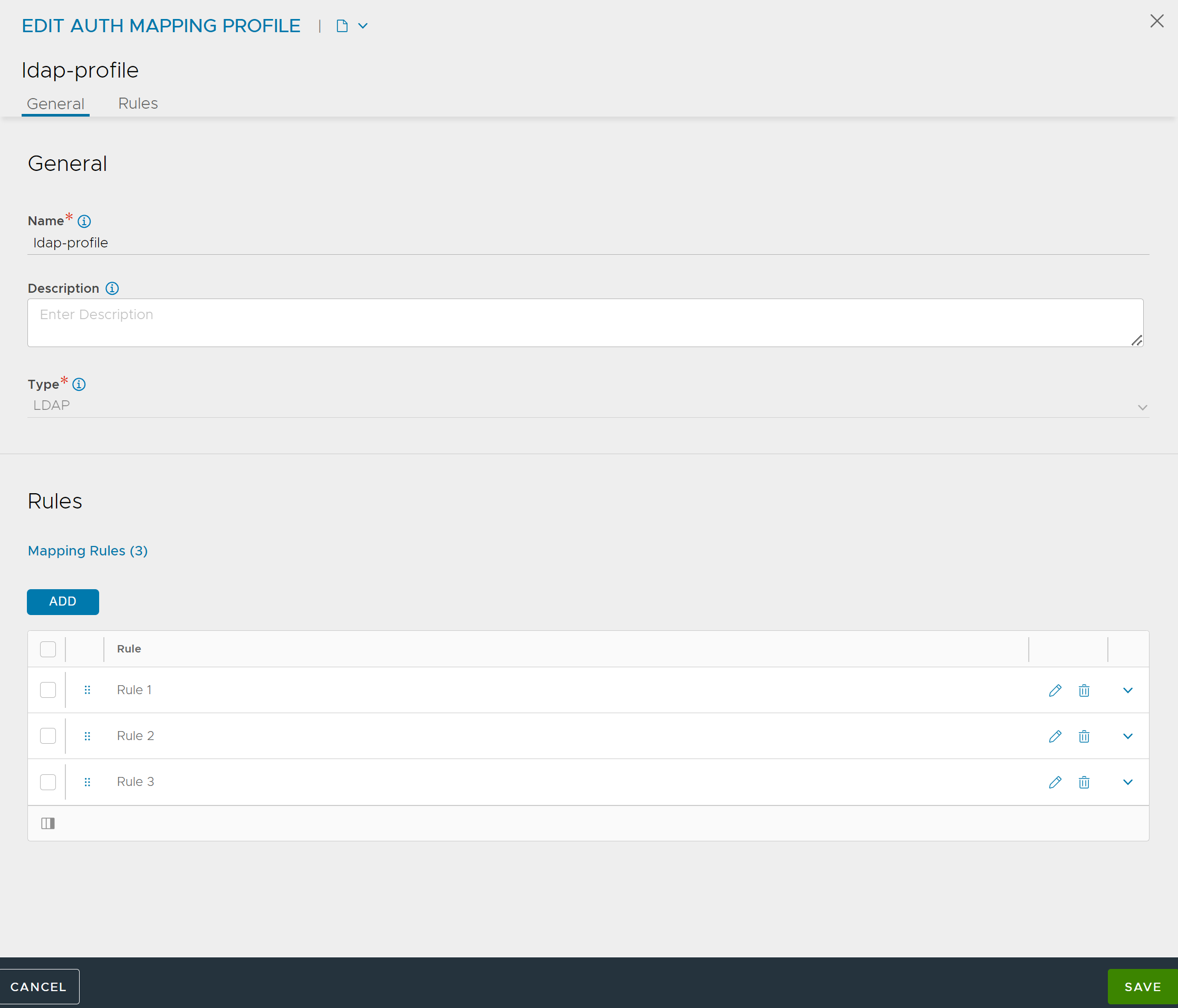
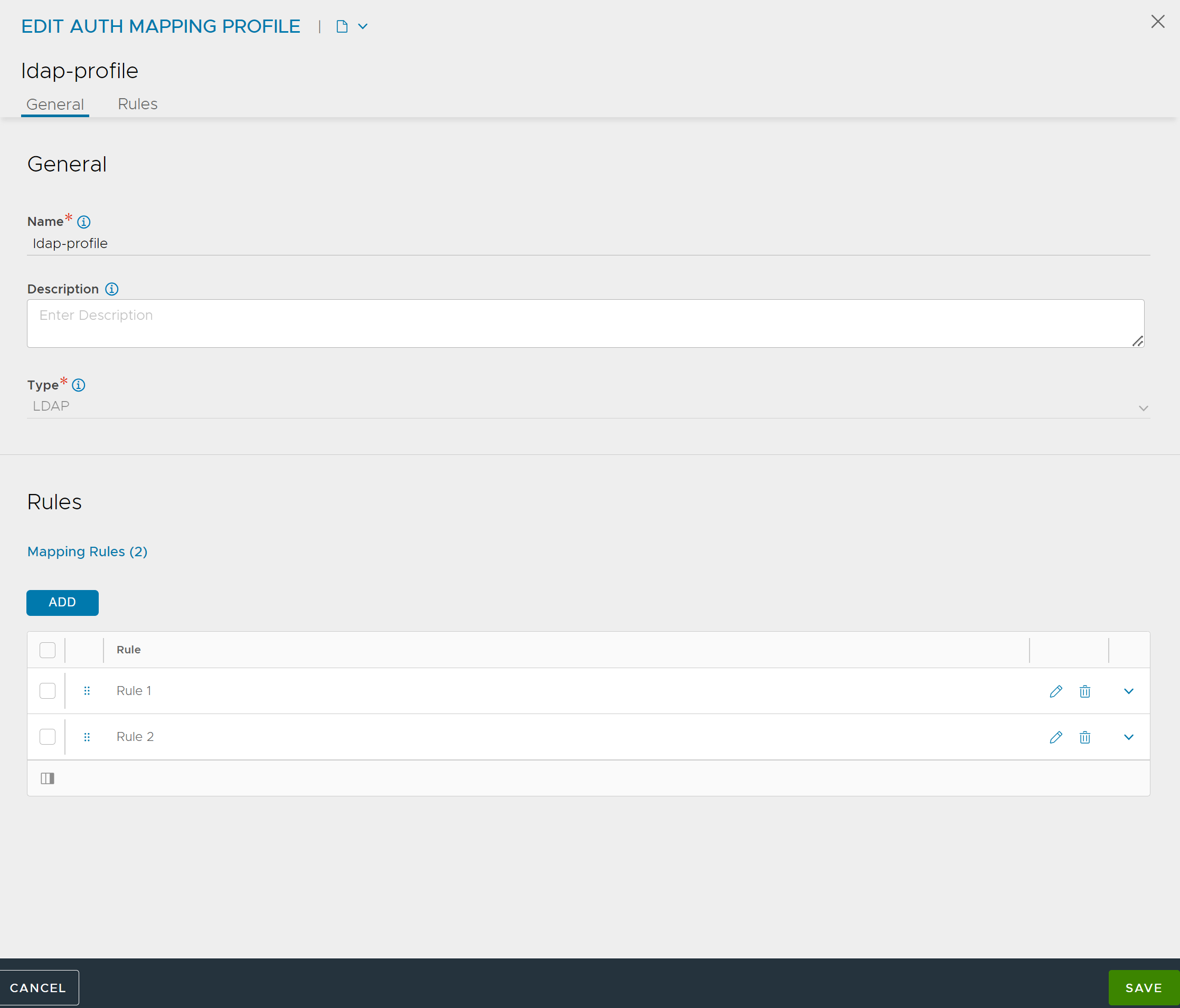
From the NSX Advanced Load Balancer UI, navigate to .
Click CREATE or edit an existing auth mapping rule.
Enter Name and Description.
Select the Type as required.
Under Rules, Click ADD.
Under Action, select Custom Mapping.
Click ADD and select User Tenant drop-down menu
From Type drop-down menu, choose Selected.
Select the required Tenants.
Note:If multiple tenants are created in the mapping rules, the first tenant selected is taken as the default tenant.
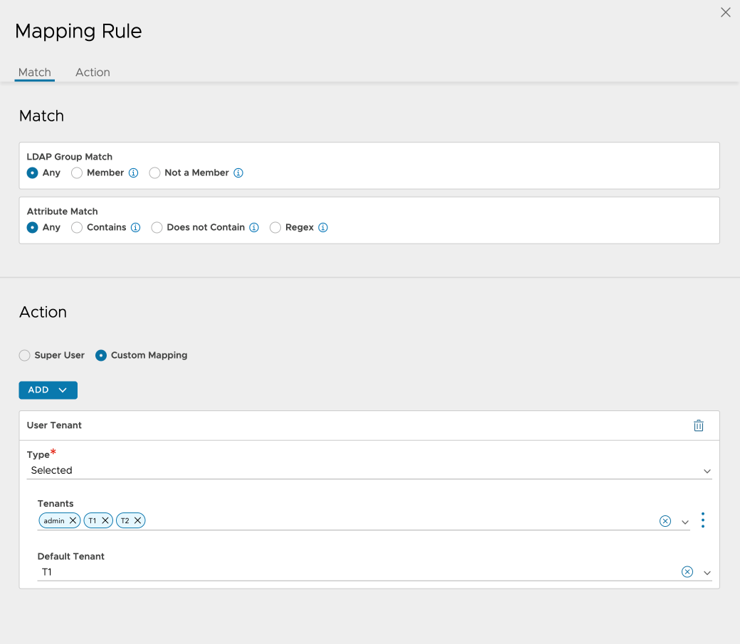
Click Save.
Alternatively, default tenant for remote users can be configured using the field default_tenant_ref through the CLI as shown below:
[admin:10-102-64-241]: authmappingprofile:mapping_rules> default_tenant_ref admin [admin:10-102-64-241]: authmappingprofile:mapping_rules> save [admin:10-102-64-241]: authmappingprofile> save +----------------------+---------------------------------------------------------+ | Field | Value | +----------------------+---------------------------------------------------------+ | uuid | authmappingprofile-46400ba5-9f05-4ec9-9464-e188010ce7b7 | | name | saml | | type | AUTH_PROFILE_SAML | | mapping_rules[1] | | | index | 0 | | is_superuser | True | | default_tenant_ref | admin | | tenant_ref | admin | +----------------------+---------------------------------------------------------+ [admin:10-102-64-241]: >
Default tenant mapping based on the tenant selected, is as shown below:
User Tenant |
Behavior |
Default Tenant |
Description |
|---|---|---|---|
All |
Admin |
All tenant values |
Any user-specified tenant is used. In the absence of user-defined tenants, admin is selected as the default tenant. |
Admin |
Admin |
All tenant values |
Any user-specified tenant is used. In the absence of user-defined tenants, admin is selected as the default tenant. |
Selected |
Tenant ref |
Only selected tenant values |
Any User-specified Tenant that is part of the selected tenant list is used. If not, Must check will display an error while creating a new mapping. For example, if the selected tenant list has T1 and T2 but the user has provided T3 as the default tenant, then the must check will display the following error: Default tenant is not in selected tenants list. If the user has not selected any tenant but has provided default tenant ref, then the error Please add at least one tenant in the selected list is displayed. |
Attribute Regex |
Tenant ref |
All tenant values |
User-specified tenant. |
Attribute value |
Tenant ref |
All tenant values |
User-specified tenant. |
Group name |
Tenant ref |
All tenant values |
User-specified tenant. |
In case of Attribute Regex, Attribute value, Group Name, if the user has entered a tenant that is not part of the user tenant list (retrieved at runtime on the basis of Attribute Regex, Attribute Value, Group Name, Group Regex match), then the first entry in the retrieved list will be assigned as the default tenant from the tenant list. For example, User1 can be assigned T1 and T2, but T3 is provided as the default tenant. Depending on the first entry in the received tenant list, either T1 or T2 will become the default tenant.
Multiple Groups Mapping to Different Roles
This example illustrates the case of an IT team with three user groups — super-admins, app-admins, and operations — where the following applies:
User Groups |
Roles |
|---|---|
Super Admins |
The users can access all tenants and all settings. |
Application Admins |
|
Application Operators |
The users has read-only access. |
Navigate to . Select Type and click ADD under the Rules section.
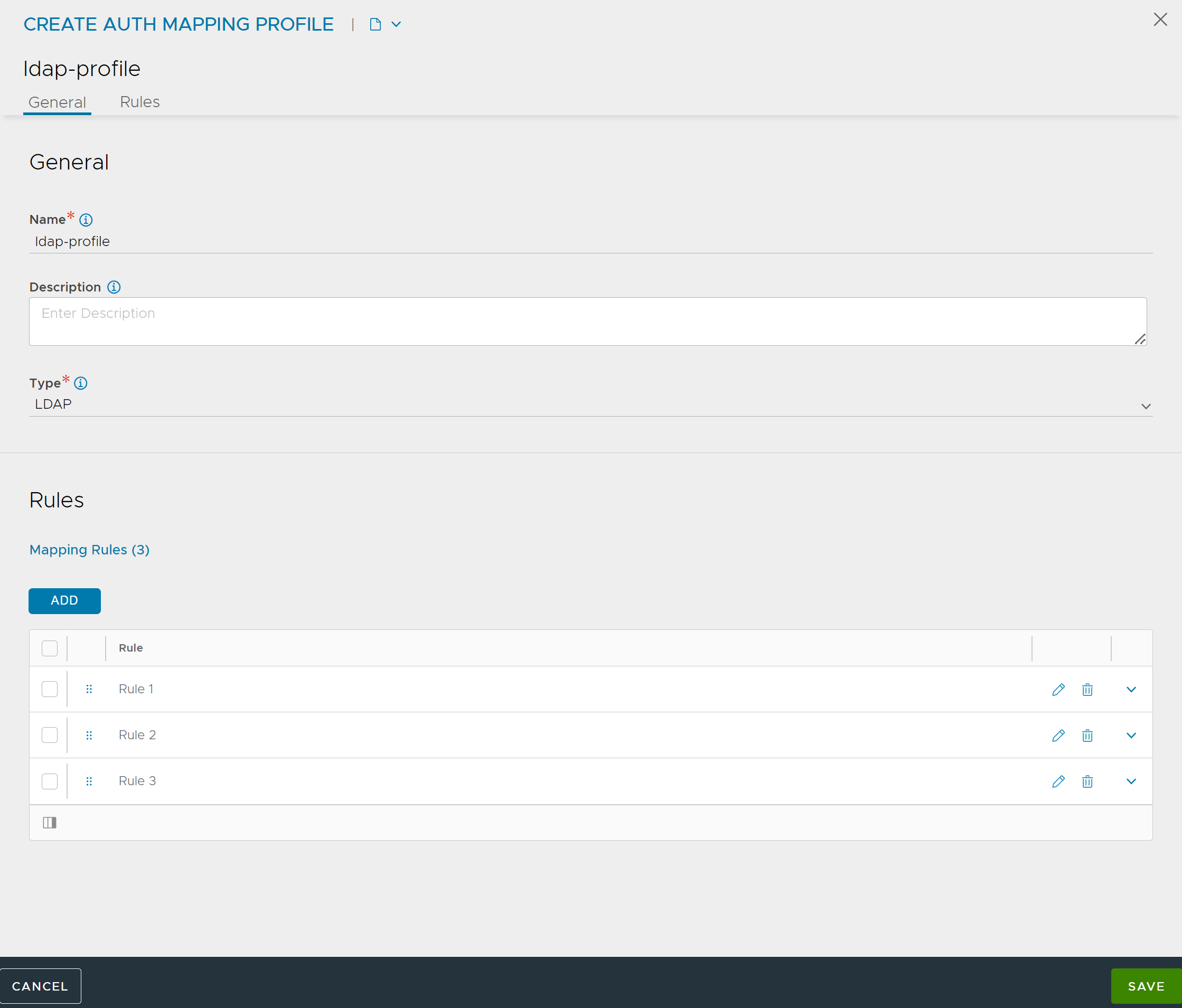
Navigate to . Under
Authentication, select Remote and click ADD.
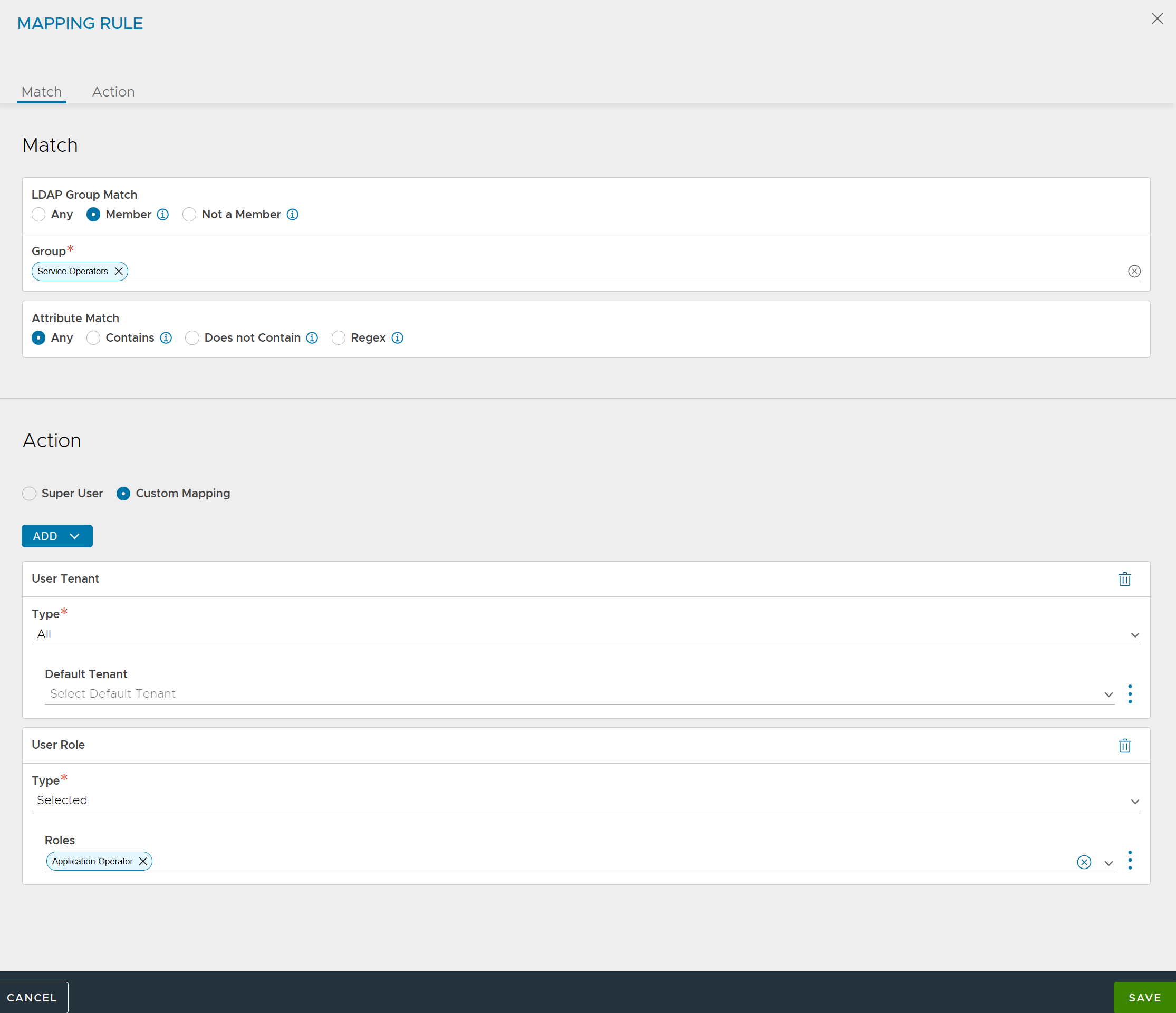
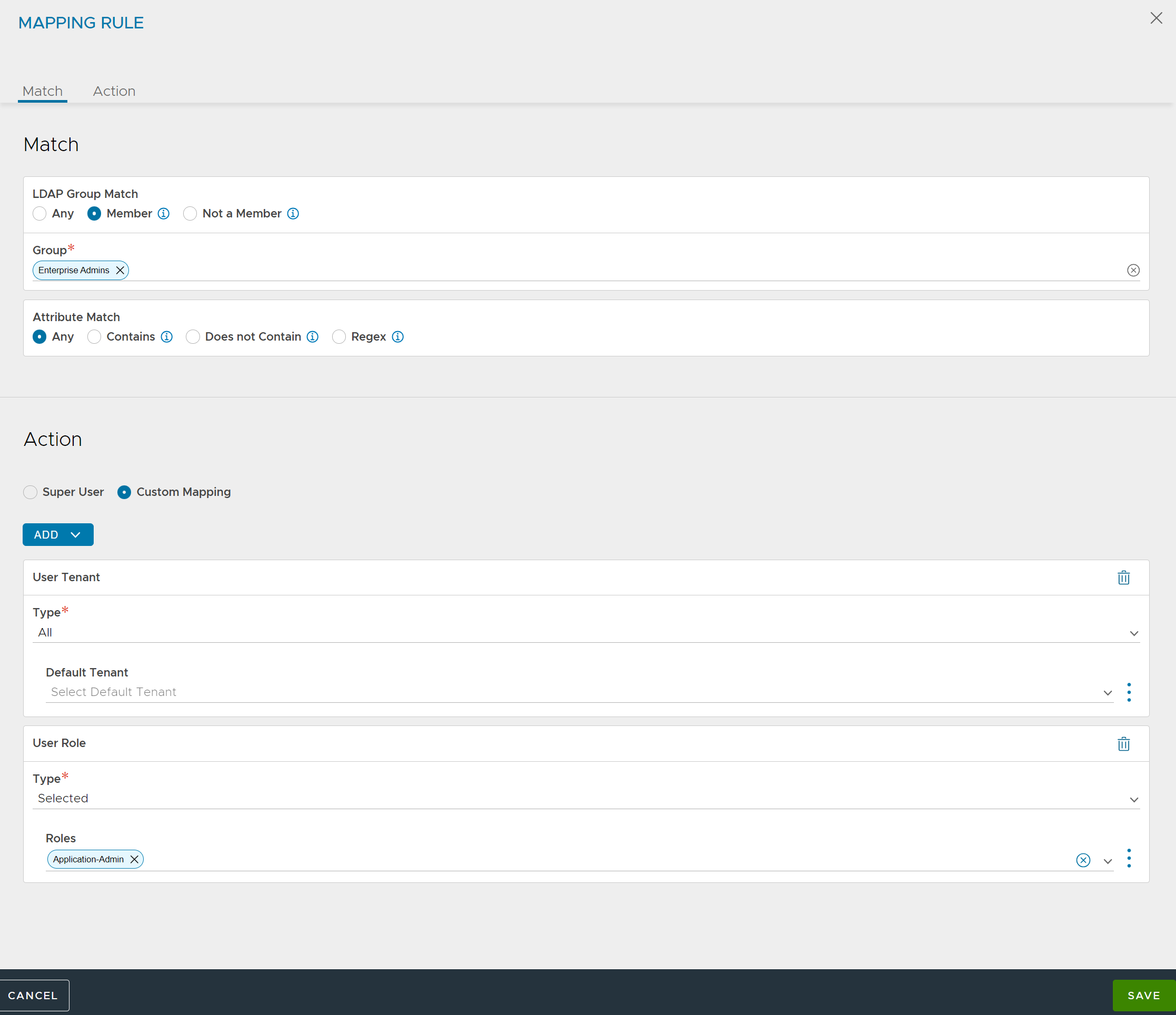
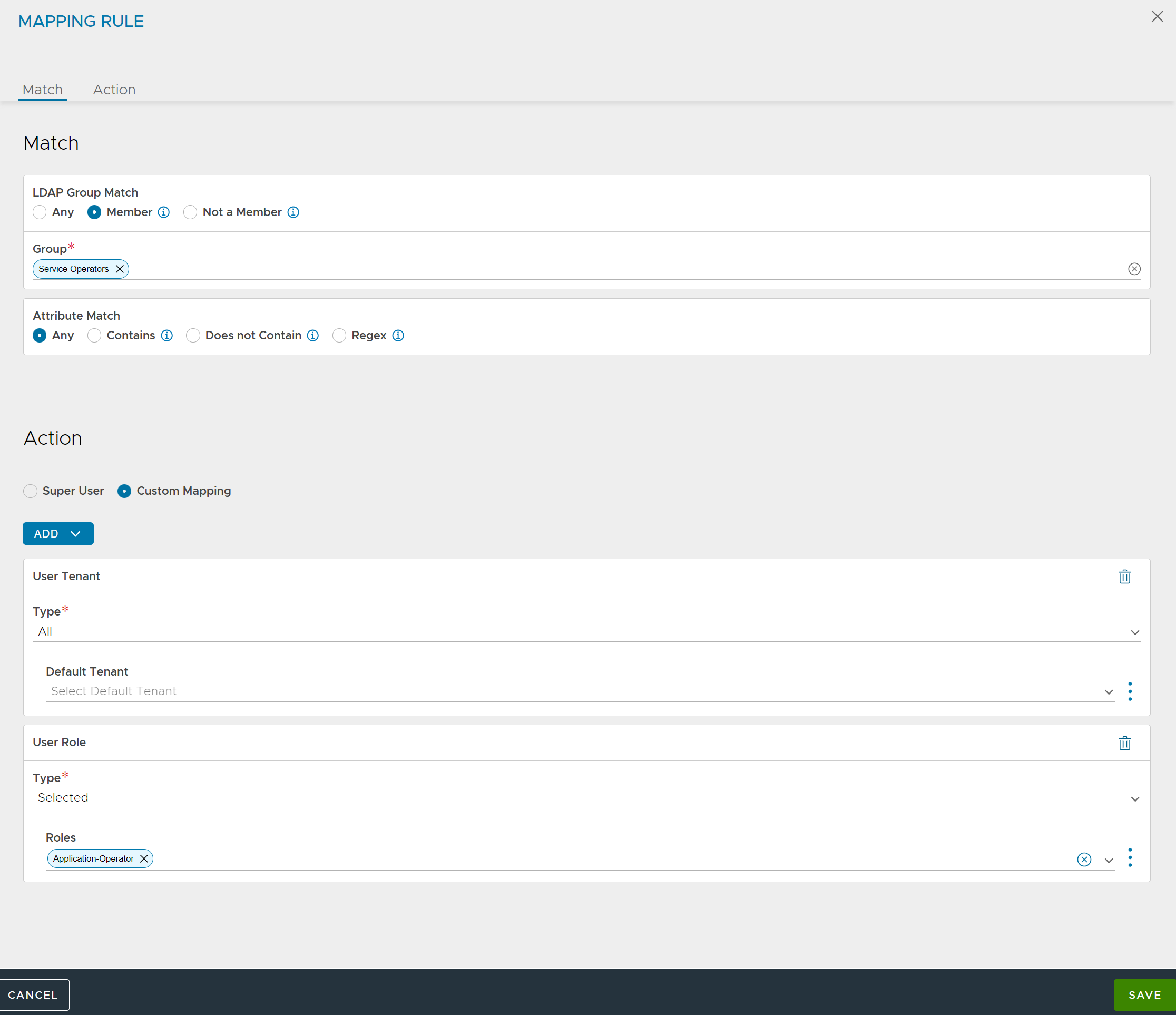
Separate mapping rules are required to map users from each group to different role or tenant assignments.
Multiple Groups Mapping to Different Tenants
This example illustrates settings for an IT team that expects tenant isolation except for a few super users.
User Groups |
Roles |
|---|---|
Super Admins |
The users can access all tenants and all settings. |
Tenant Application Admins |
The users have access to a few tenants — app owner for a few tenants. |
Tenant Application Operators |
The users have access to a few tenants — cannot modify anything. |
Tenant Application Admins or Operators |
The users have access to a few tenants as app owners and other tenants as app operator folks. |
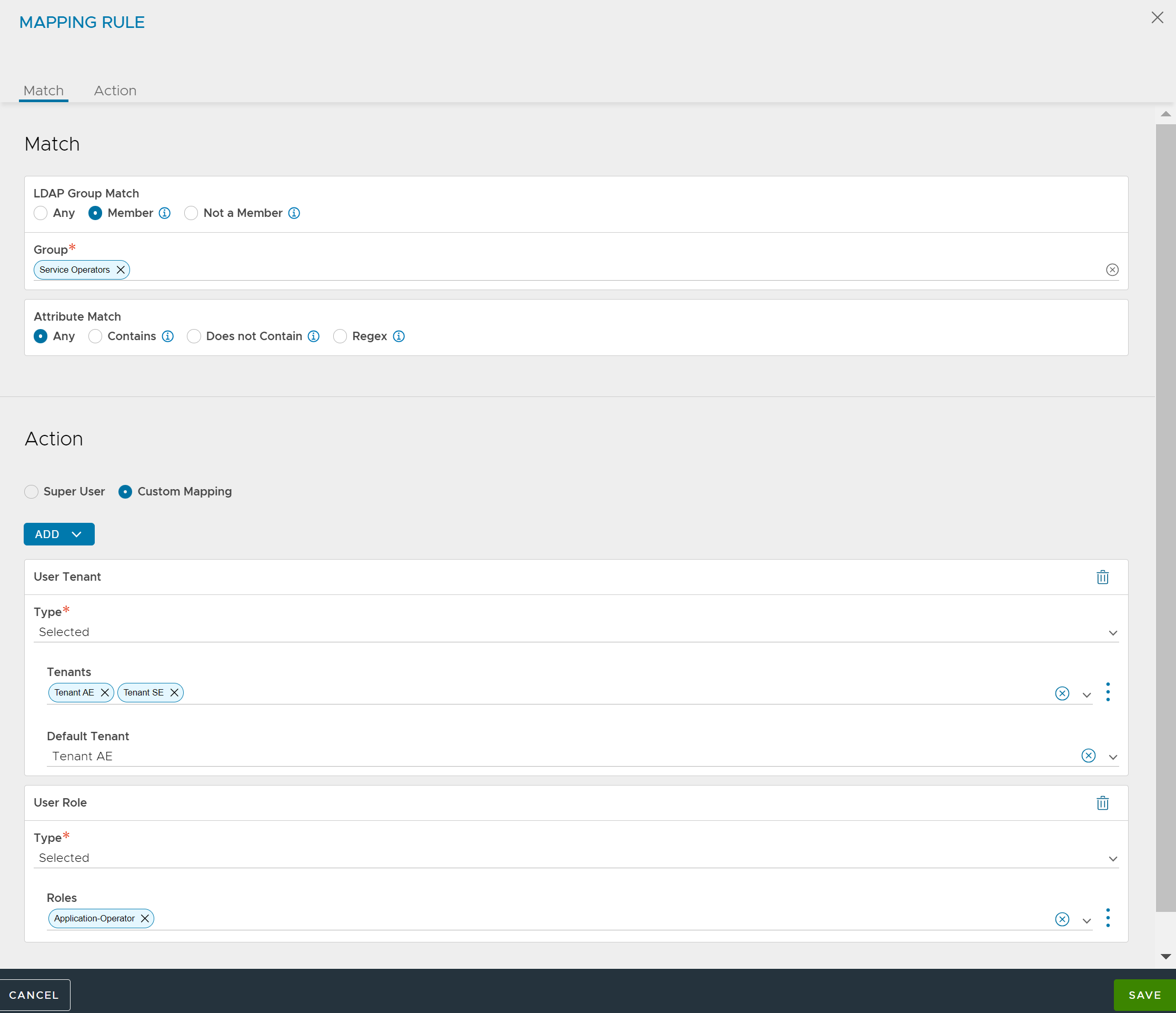
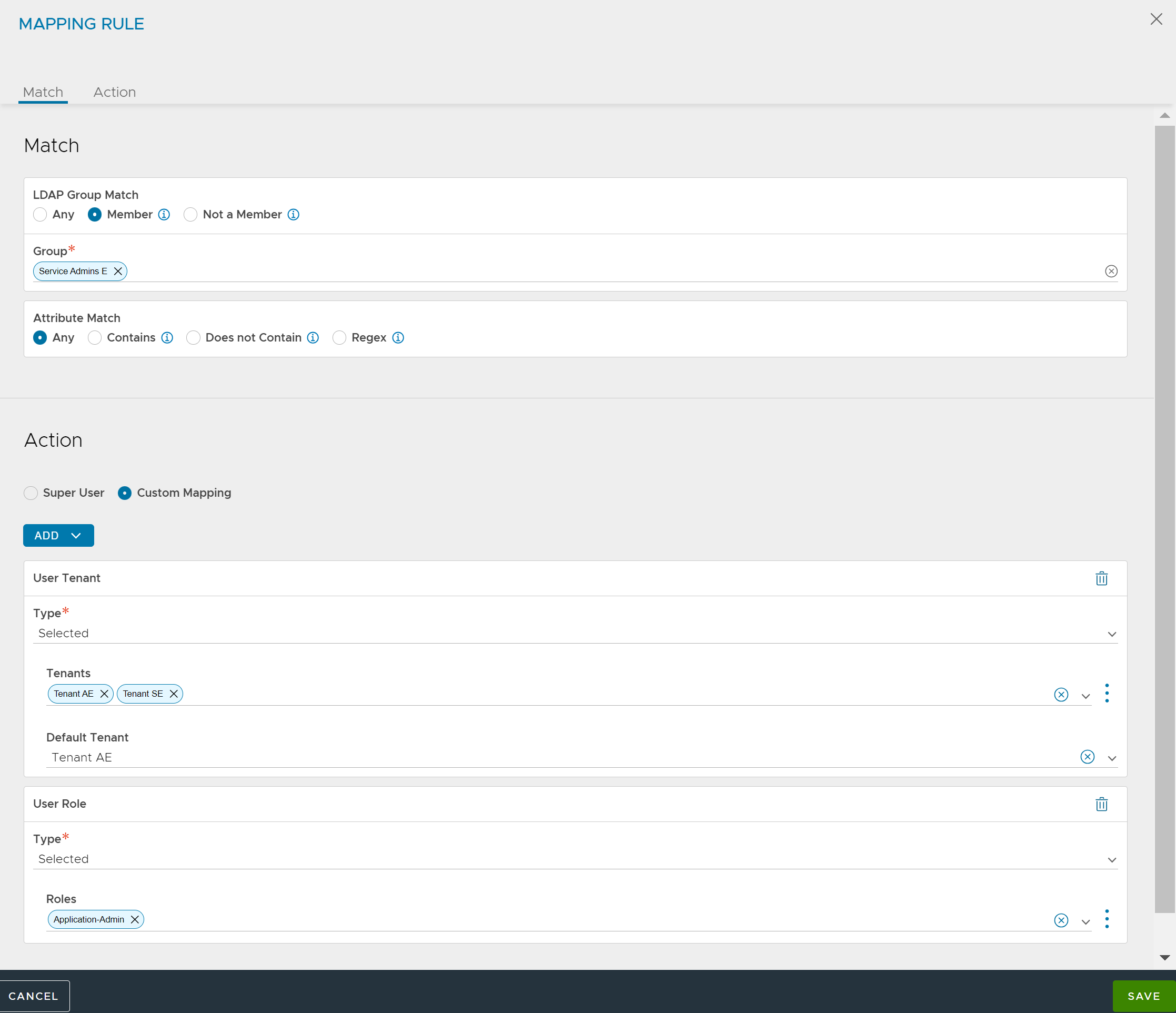
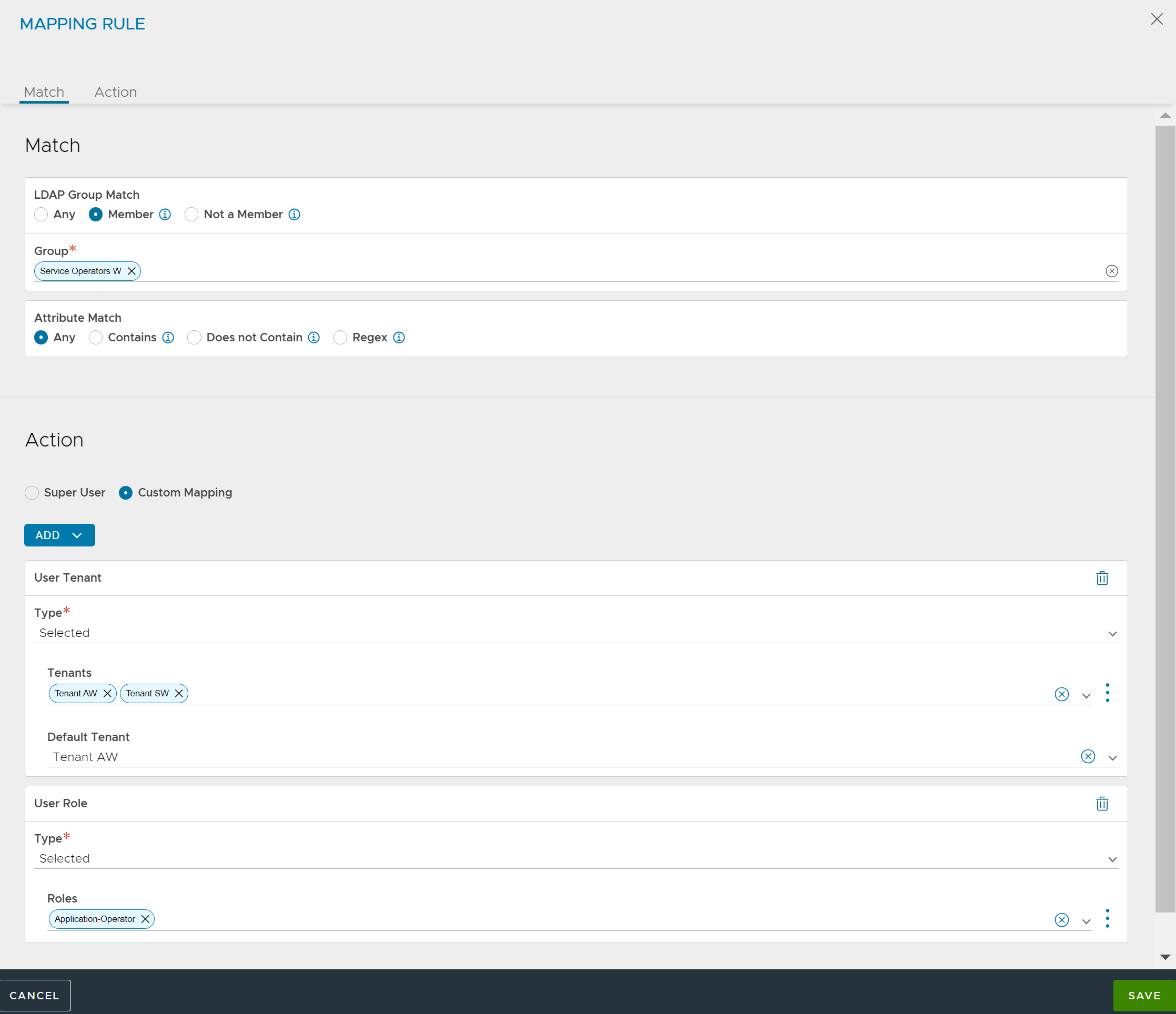
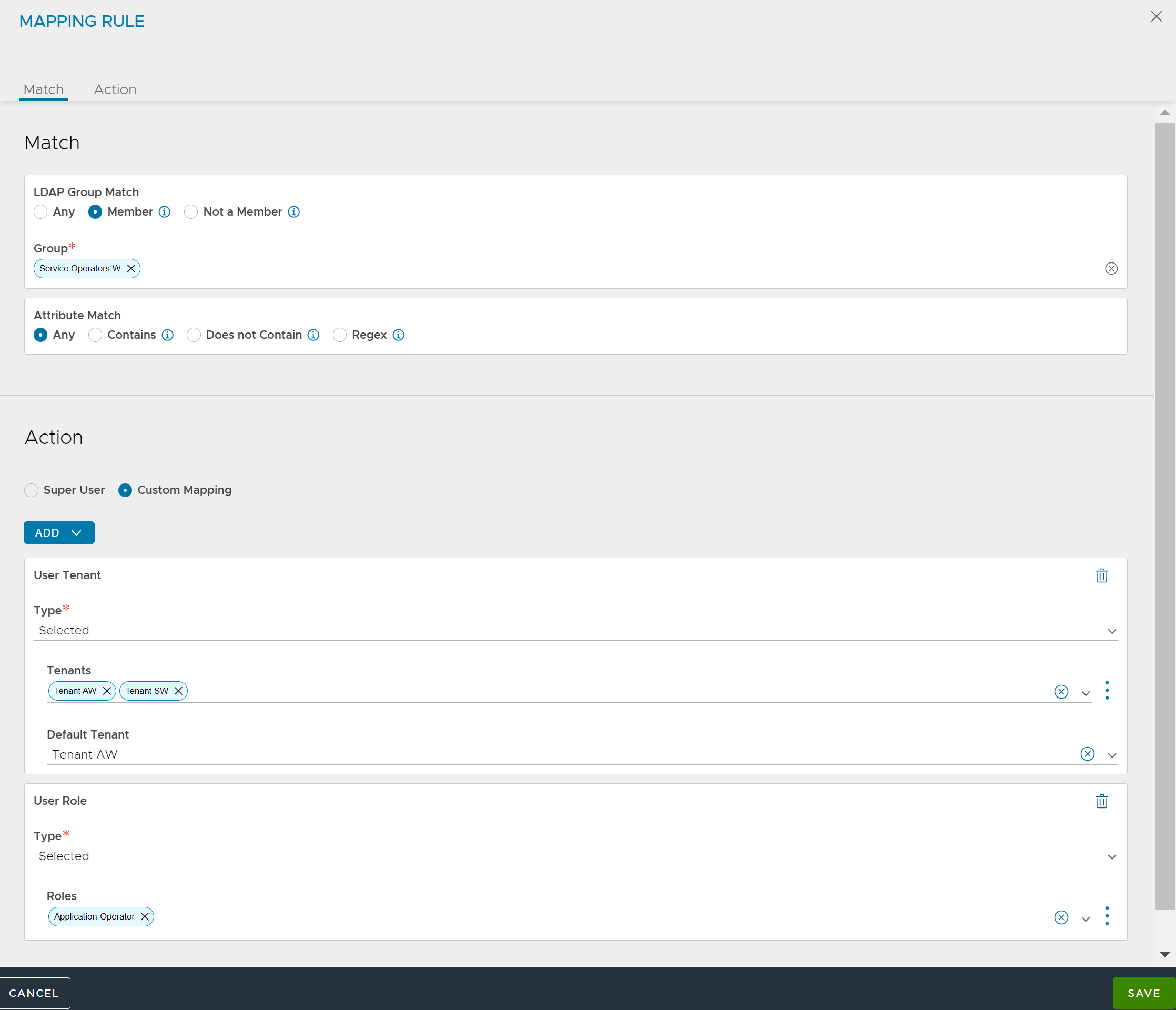
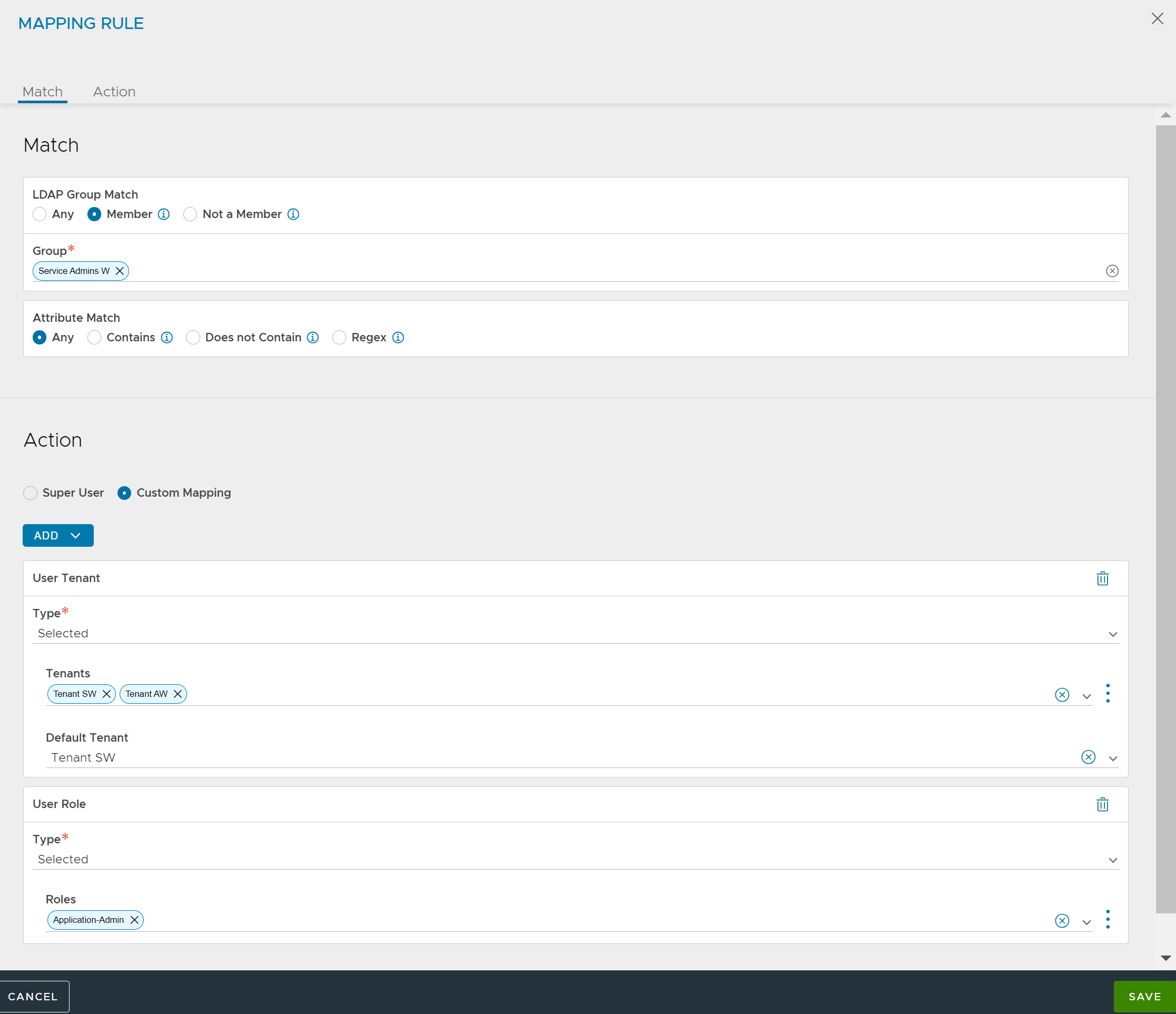
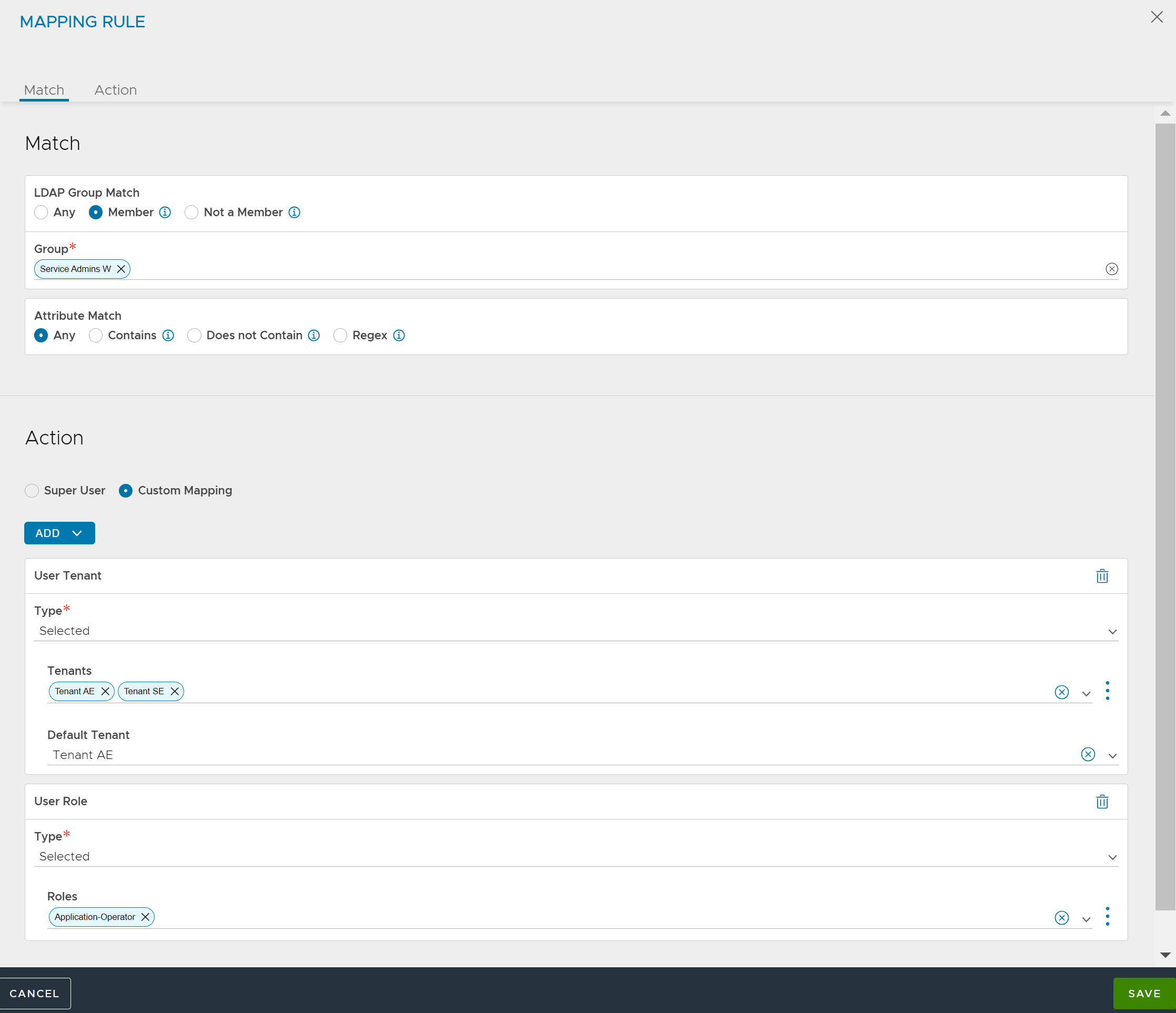
In this example, members of group Service Admins E have read or write access (Application-Admin role) in tenants Tenant AE and Tenant SE, whereas they have read-only access (Application-Operator role) in a few other tenants. Service Operators have only read-only access in their respective tenants.
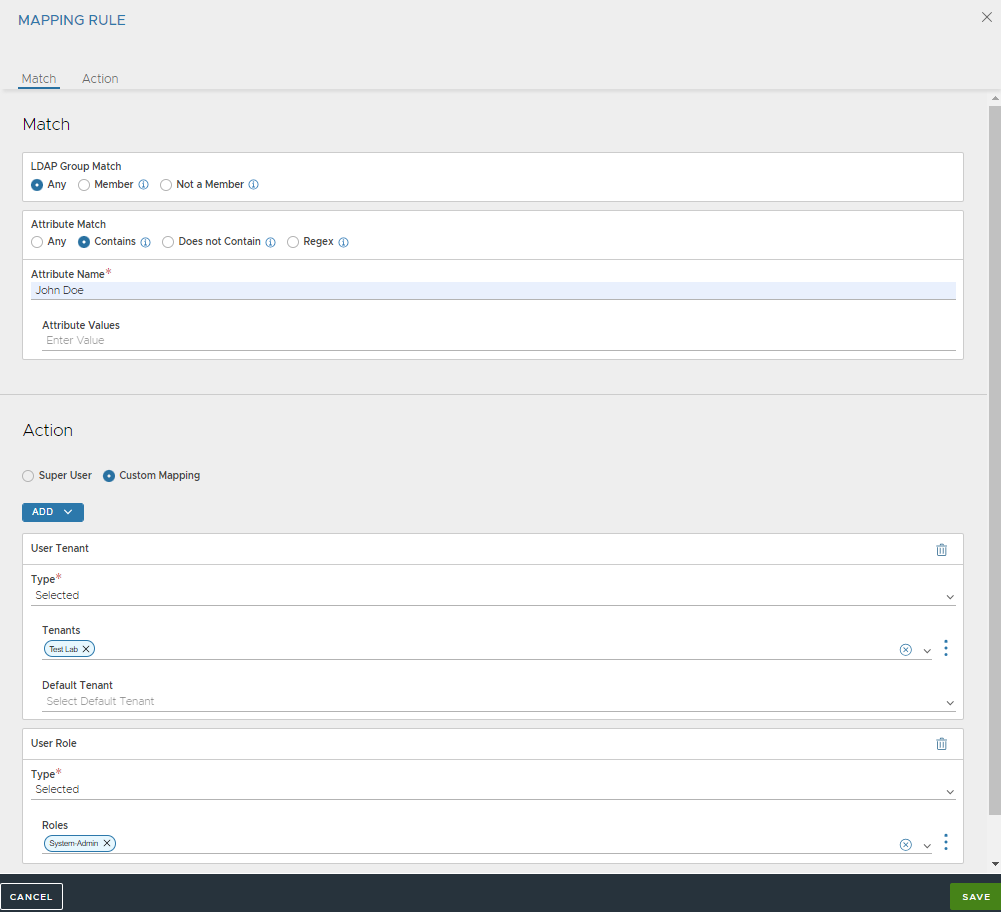
Multiple Authorizations for a Single User
In this example, the login of user John Doe results in the user gaining access through multiple authorization mapping rules.
Multiple mapping rules are configured based on various group and attribute criteria.
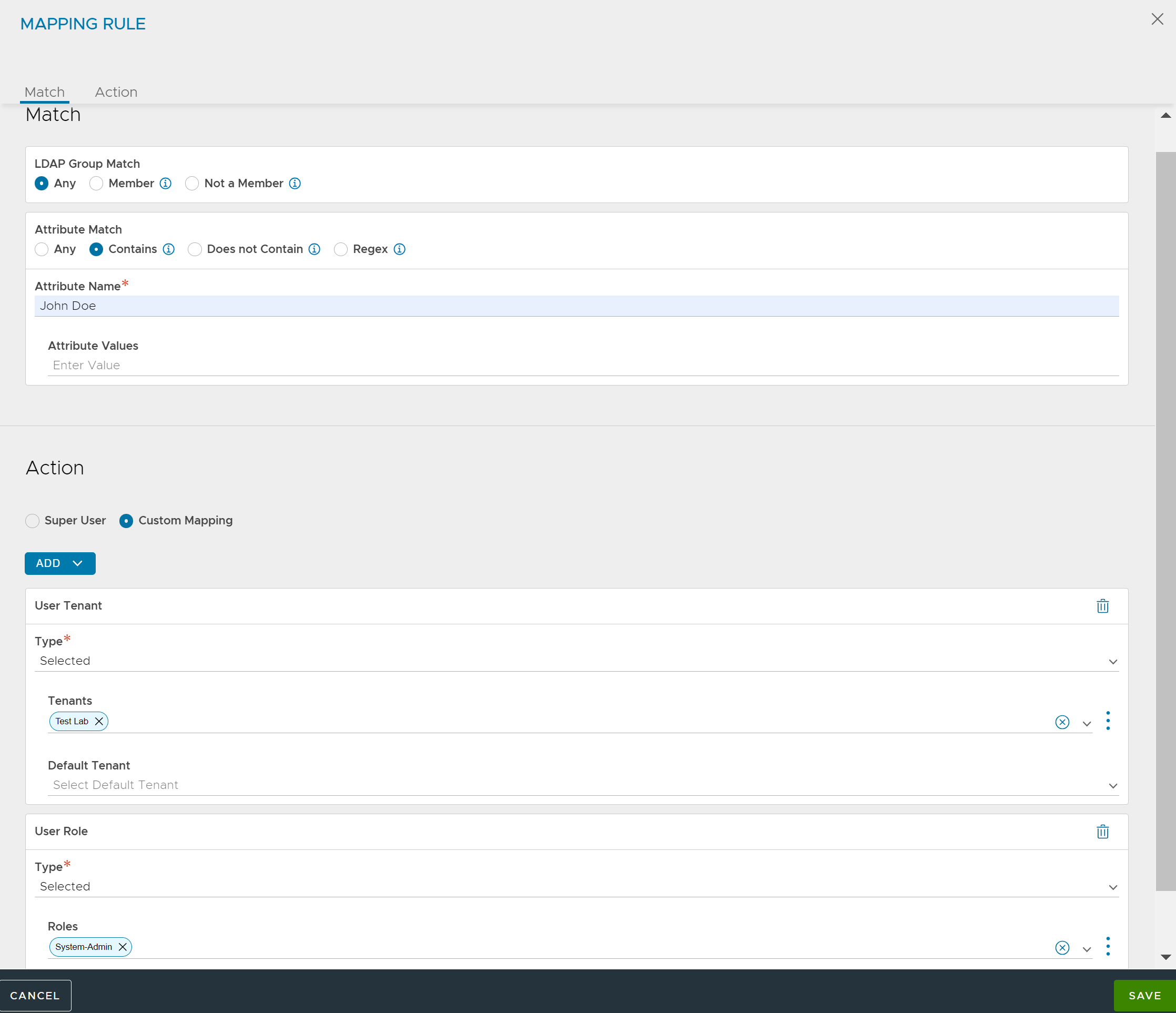
The LDAP server is configured with user John Doe.
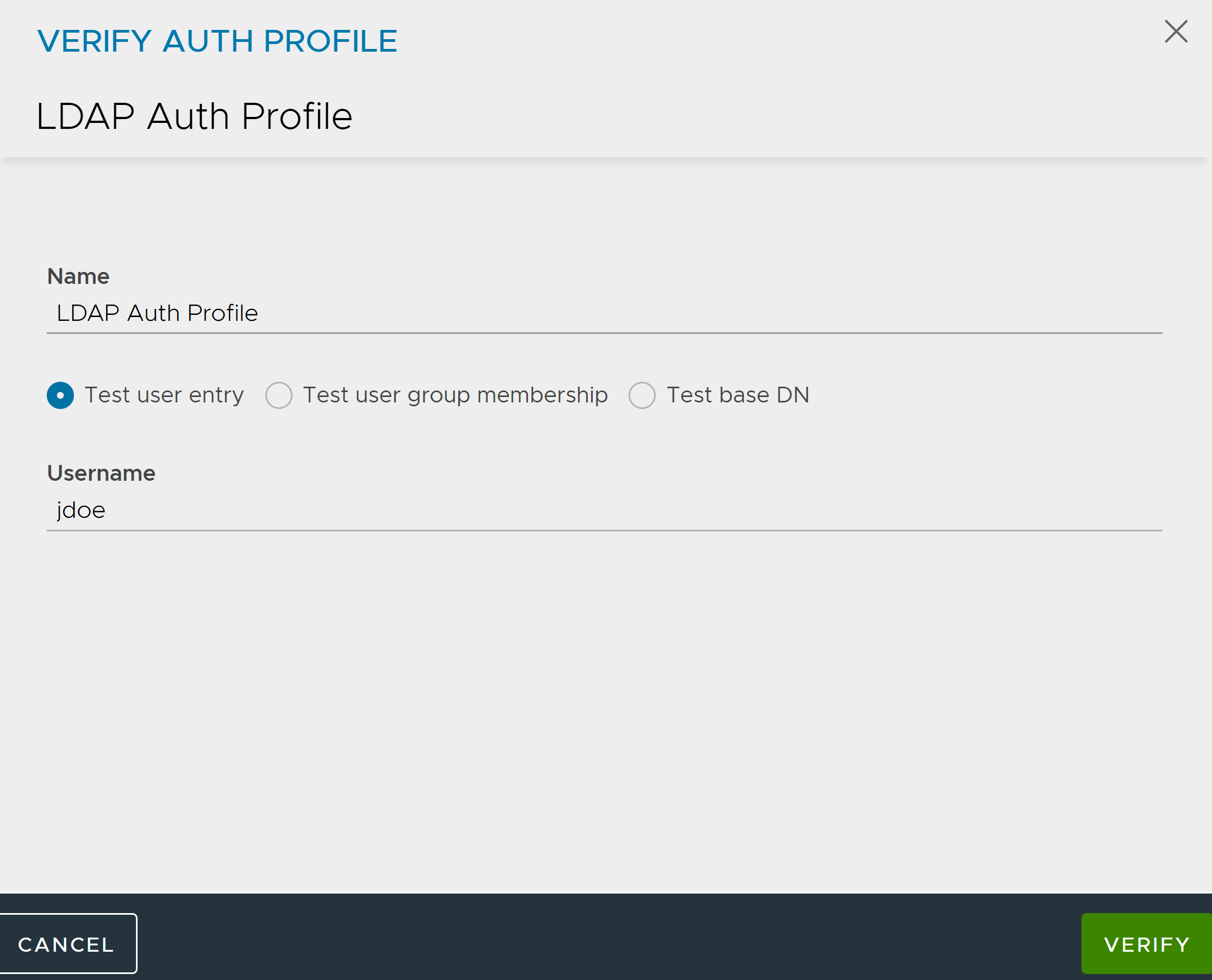
The LDAP server can be configured with John Doe as a member of the groups - Enterprise Admins and Service Operators.
After the user John Doe logs in, and all authorization rules are applied to the user session. Multiple role or tenant combinations are used to determine user privileges during user login. The user record shows the user successfully matched all four rules and role or tenant pairs were appropriately applied.
Multiple Authorizations Resulting in a Super User
In this example, the login of user John Doe results in the user becoming a super user.
Mapping rules make a member of the group Service Operators a super user.
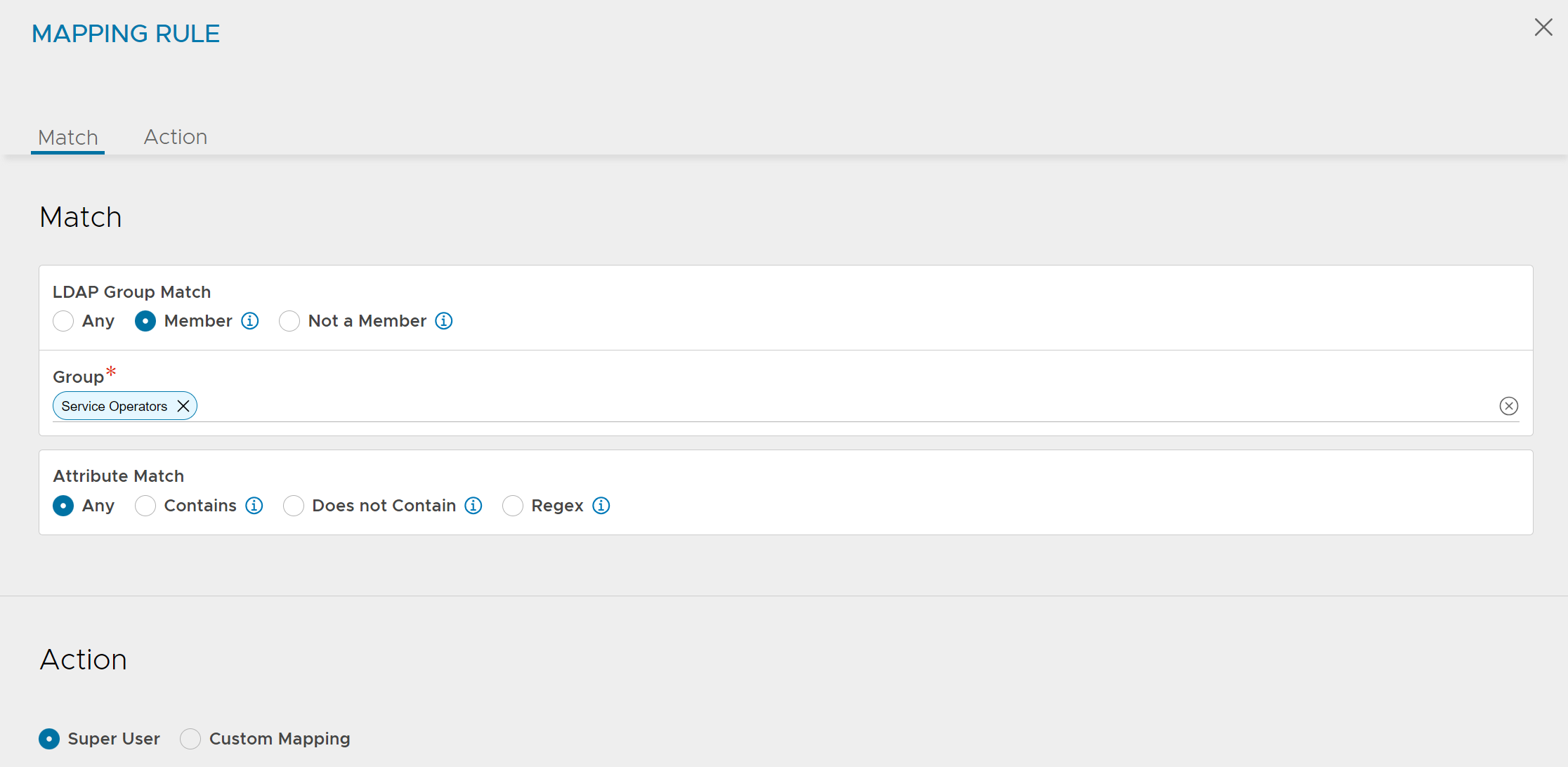
Due to the super user access, user John Doe gets access to all tenants with every role.
No Authorizations for a Single User
In this example, the login of user John Doe results in the user not getting any roles or tenants.
Mapping rules are updated to keep user John Doe from having any privileges.
When user John Doe logs in, the user interface reports no privileges to login.
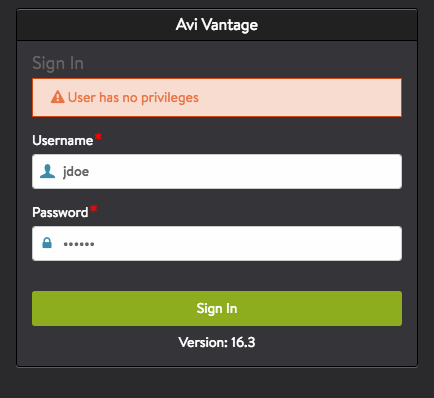
User record does not have any access entries.
[: > show user jdoe +----------------------+-------------------------------------------+ | Field | Value | +----------------------+-------------------------------------------+ | uuid | user-2d4348f3-fcf6-4af3-9c8b-ff54476ad7f6 | | username | jdoe | | name | jdoe | | email | | | is_superuser | False | | last_login_ip | 10.10.221.128 | | last_login_timestamp | 2016-08-07 06:08:42 | | logged_in | True | | local | False | | full_name | John Doe | +----------------------+-------------------------------------------+
Dynamic Tenant and Role Mappings
NSX Advanced Load Balancer supports dynamically mapping tenants and/or roles based on regular expression matching against the user’s group memberships or user LDAP attributes.
The mapping is achieved using regex Named Capture Groups of the form (?P{tenant|role}<match>).
In the following example, the user is a member of the LDAP groups lb_app1234_admin and lb_app7890_admin, where app1234 and app7890 correspond to the names of tenants defined in NSX Advanced Load Balancer. The example will grant the user the specific Tenant-Admin role within these tenants.
configure authmappingprofile authmapping
[admin:avicontroller]: > configure authmappingprofile authmapping
[admin:avicontroller]: authmappingprofile> mapping_rules index 1
New object being created
[admin:avicontroller]: authmappingprofile:mapping_rules> group_match
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> criteria auth_match_regex
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> groups "lb_(?P{tenant}\w+)_admin"
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> save
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_tenant assign_matching_group_regex
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_role assign_from_select_list
[admin:avicontroller]: authmappingprofile:mapping_rules> role_refs Tenant-Admin
[admin:avicontroller]: authmappingprofile:mapping_rules> save
Roles may also be dynamically mapped using the ?P{role} Named Capture Group. The example below will map a user that is a member of a group named lb_app1234_appowner to the role appowner and tenant app1234:
configure authmappingprofile authmapping
[admin:avicontroller]: > configure authmappingprofile authmapping
[admin:avicontroller]: authmappingprofile> mapping_rules index 1
New object being created
[admin:avicontroller]: authmappingprofile:mapping_rules> group_match
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> criteria auth_match_regex
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> groups "lb_(?P{tenant}\w+)_(?P{role}\w+)"
[admin:avicontroller]: authmappingprofile:mapping_rules:group_match> save
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_tenant assign_matching_group_regex
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_role assign_matching_group_regex
[admin:avicontroller]: authmappingprofile:mapping_rules> save
Similarly, regex-based mapping based on the value of an LDAP attribute rather than group membership is also supported. The example below will map a user with LDAP attribute business_unit with value bu_sales to the tenant sales:
configure authmappingprofile authmapping
[admin:avicontroller]: > configure authmappingprofile authmapping
[admin:avicontroller]: authmappingprofile> mapping_rules index 1
New object being created
[admin:avicontroller]: authmappingprofile:mapping_rules> attribute_match
[admin:avicontroller]: authmappingprofile:mapping_rules:attribute_match> criteria auth_match_regex
[admin:avicontroller]: authmappingprofile:mapping_rules:attribute_match> name business_unit
[admin:avicontroller]: authmappingprofile:mapping_rules:attribute_match> values "bu_(?P{tenant}\w+)"
[admin:avicontroller]: authmappingprofile:mapping_rules:attribute_match> save
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_tenant assign_matching_attribute_regex
[admin:avicontroller]: authmappingprofile:mapping_rules> tenant_attribute_name business_unit
[admin:avicontroller]: authmappingprofile:mapping_rules> assign_role assign_from_select_list
[admin:avicontroller]: authmappingprofile:mapping_rules> role_refs Tenant-Admin
[admin:avicontroller]: authmappingprofile:mapping_rules> save
Note: Currently group-based regex matching can only be configured through the CLI/API.
User Profile Mapping
Using user profile mapping, it is possible to choose a user profile for remote users based on certain conditions.
Use the following CLI to configure the user profile:
[admin:123]: systemconfiguration> admin_auth_configuration [admin:123]: systemconfiguration:admin_auth_configuration> mapping_rules index 1 [admin:123]: systemconfiguration:admin_auth_configuration:mapping_rules> assign_userprofile assign_from_select_list [admin:123]: systemconfiguration:admin_auth_configuration:mapping_rules> userprofile_ref Tacacs-Userprofile [admin:123]: systemconfiguration:admin_auth_configuration:mapping_rules> save
Ensure that the user profile is already created. For more information on how to create and configure a user profile, see User Profile.
View the user profile configuration as shown below.
[admin:123]: > show systemconfiguration |----------------------------------|------------------------------------| |Field | Value | |----------------------------------|------------------------------------| | Truncated Output | | admin_auth_configuration | | | auth_profile_ref | tacacs1 | | mapping_rules[1] | | | index | 1 | | assign_tenant | ASSIGN_FROM_SELECT_LIST | | tenant_attribute_name | | | tenant_refs[1] | admin | | assign_role | ASSIGN_FROM_SELECT_LIST | | role_attribute_name | | | role_refs[1] | Application-Admin | | is_superuser | False | | assign_userprofile | ASSIGN_FROM_SELECT_LIST | | userprofile_ref | Tacacs-Userprofile | | allow_local_user_login | True | |----------------------------------|------------------------------------|