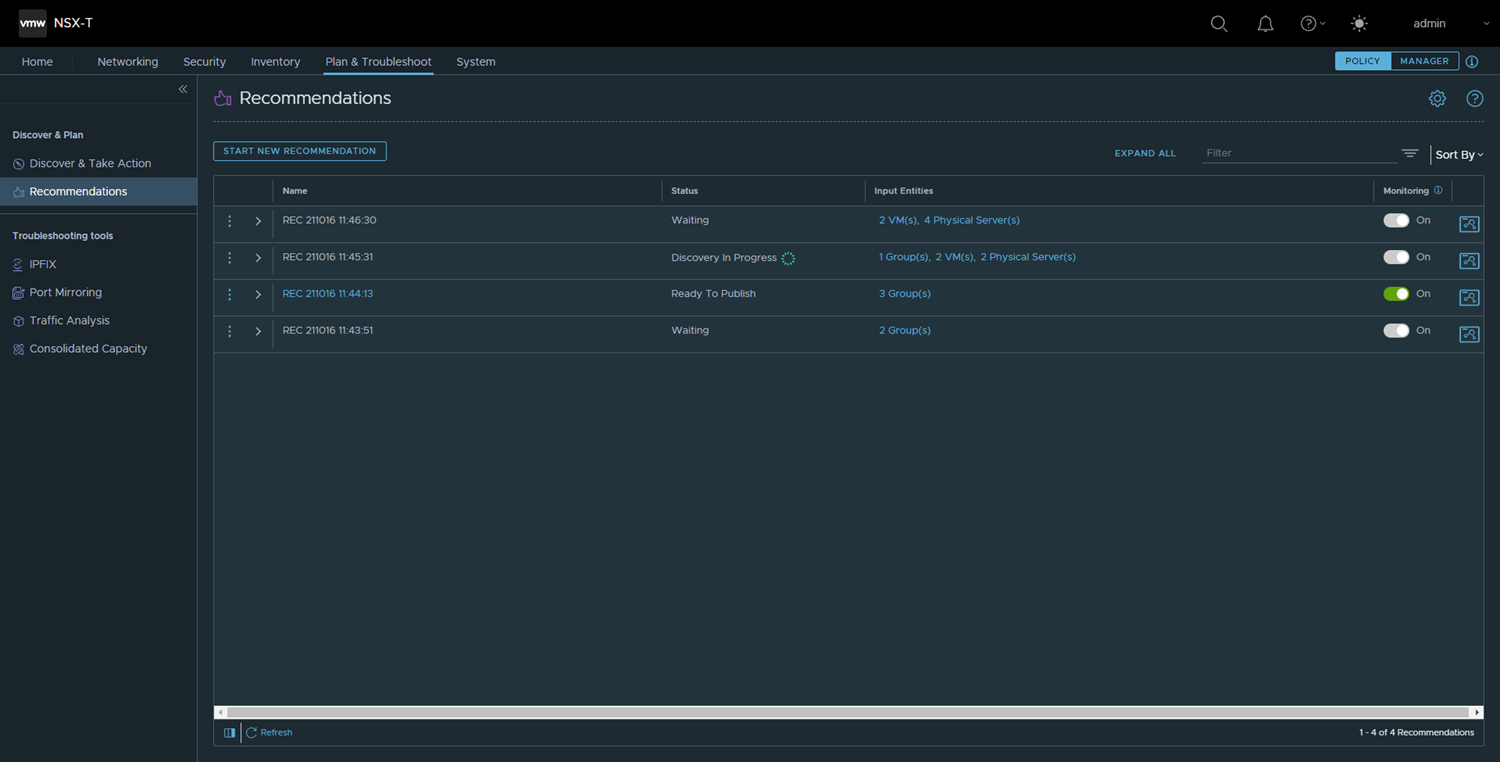
The NSX Intelligence Recommendations feature can provide you with recommendations to help you micro-segment your applications.
Generating an NSX Intelligence recommendation involves recommendations of security policies, policy security groups, and services for the application. The recommendations are made based on the traffic pattern of communication between virtual machines (VMs) and physical servers in your NSX-T Data Center.
You can generate a recommendation by selecting the input entities of groups or 100 VMs and physical servers, or a combination of groups, VMs, and physical servers, or existing security policies. The total number of VMs and physical servers that you can select as input cannot exceed 100 of those entities. The total number of effective VMs and physical servers that you can use in an input that includes groups, VMs, or physical servers cannot exceed 250 input entities.
For example, if you select 50 VMs and 50 physical servers as part of your recommendation input entities, you can only select groups with no more than 150 compute members combined.
You can only generate a new recommendation for security groups that were created in Policy mode. The security groups must have at least one of the supported member types in order for the NSX Intelligence feature to begin a recommendation analysis for those security groups. The supported member types include virtual machines, physical servers, virtual network interfaces (VIFs), logical ports, and logical switches. If at least one supported member type is present in the security group, the recommendation analysis can proceed, but unsupported member types are not considered during the recommendation analysis.
There are multiple ways to generate a recommendation using the NSX Intelligence user interface. The following procedure describes the available methods to use.
Prerequisites
Activate the NSX Intelligence 3.2 or later feature on the NSX Application Platform. See the Activating and Upgrading VMware NSX Intelligence 3.2 document.
Ensure you have the required privileges to generate recommendations. See Role-Based Access Control in NSX Intelligence for more information.
 on the left-side of the
on the left-side of the