In this topic, you can learn how TAS for VMs uses WebSockets, why use WebSockets in your apps, and how to configure your load balancer to support WebSockets.
Operators who use a load balancer to distribute incoming traffic across VMware Tanzu Application Service for VMs (TAS for VMs) router instances must configure their load balancer for WebSockets. Otherwise, the Loggregator system cannot stream app logs to developers, or app event data and component metrics to third-party aggregation services. Additionally, developers cannot use WebSockets in their apps.
WebSocket overview
The WebSocket protocol provides full-duplex communication over a single TCP connection. Apps can use WebSockets to perform real-time data exchange between a client and a server more efficiently than HTTP.
TAS for VMs uses WebSockets for the following metrics and logging purposes:
-
To stream all app event data and component metrics from the Doppler server instances to the Traffic Controller.
-
To stream app logs from the Traffic Controller to developers using the Cloud Foundry Command Line Interface (cf CLI) or Getting Started with Apps Manager.
-
To stream all app event data and component metrics from the Traffic Controller over the Firehose endpoint to external apps or services.
For more information about these Loggregator components, see Loggregator Architecture.
Configuring your load balancer for WebSockets
To form a WebSocket connection, the client sends an HTTP request that contains an Upgrade header and other headers required to complete the WebSocket handshake. You must configure your load balancer to not upgrade the HTTP request, but rather to pass the Upgrade header through to the TAS for VMs router. The procedures required to configure your load balancer depend on your IaaS and load balancer. Here are several possible approaches:
-
Some load balancers can recognize the
Upgradeheader and pass these requests through to the TAS for VMs router without returning the WebSocket handshake response. This may not be the default behavior, and may require additional configuration. -
Some load balancers do not support passing WebSocket handshake requests containing the
Upgradeheader to the TAS for VMs router. For example, the Amazon Web Services (AWS) Elastic Load Balancer (ELB) does not support this behavior. In this scenario, you must configure your load balancer to forward TCP traffic to your TAS for VMs router to support WebSockets. If your load balancer does not support TCP pass-through of WebSocket requests on the same port as other HTTP requests, you can do one of the following:-
Configure your load balancer to listen on a non-standard port (the built-in TAS for VMs load balancer listens on 8443 by default for this purpose), and forward requests for this port in TCP mode. App clients must make WebSockets upgrade requests to this port. If you choose this strategy, you must follow the steps in Set Your Loggregator Port.
-
If a non-standard port is not acceptable, add a load balancer that handles WebSocket traffic (or another IP on an existing load balancer) and configure it to listen on standard ports 80 and 443 in TCP mode. Configure DNS with a new hostname, such as
ws.cf.example.com, to be used for WebSockets. This hostname should resolve to the new load balancer interface.
-
Regardless of your IaaS and configuration, you must configure your load balancer to send the X-Forwarded-For and X-Forwarded-Proto headers for non-WebSocket HTTP requests on ports 80 and 443. For more information, see Securing Traffic into TAS for VMs.
Gorouter does not support:
- WebSockets requests for routes that are bound to route services: These requests return a 503 error and a
X-Cf-Routererror route_service_unsupportedheader.
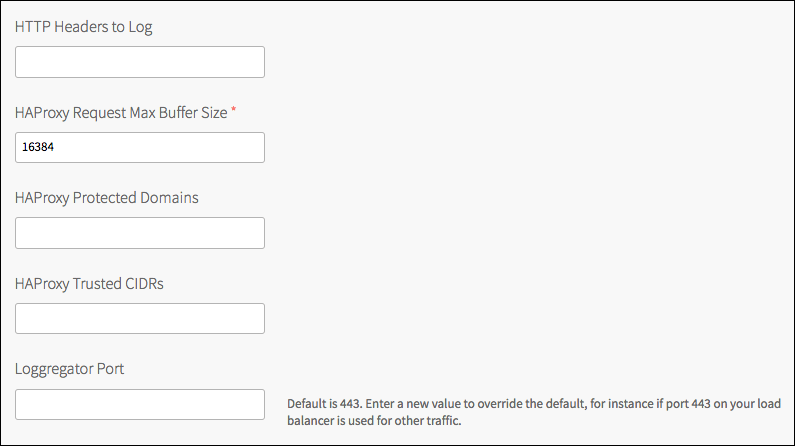
Set your Loggregator port
By default, TAS for VMs assigns port 443 for TCP/WebSocket communications. If you have configured your load balancer to use a port other than 443 for TCP/WebSocket traffic, you must edit the Loggregator port field in the Networking pane of the TAS for VMs tile.