Enable cloud security to establish a secured tunnel from an Edge to cloud security service sites. This enables the secured traffic being redirected to third-party cloud security sites.
- Ensure that you have access permission to configure network services.
- Ensure that your SD-WAN Orchestrator has version 3.3.x or above.
- You should have Cloud security service gateway endpoint IPs and FQDN credentials configured in the third party Cloud security service.
- In the Enterprise portal, click .
- Click the Device Icon next to a profile, or click the link to the profile, and then click the Device tab.
- In the Cloud Security area, switch the dial from the Off position to the On position.
- Configure the following settings:
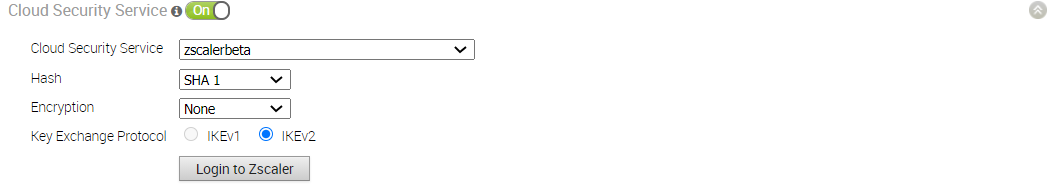
Option Description Cloud Security Service Select a cloud security service from the drop-down menu to associate with the profile. You can also click New Cloud Security Service from the drop-down to create a new service type. For more information about how to create a new CSS, see Configure a Cloud Security Provider. Note: For cloud security services with Zscaler login URL configured, Login to Zscaler button appears in the Cloud Security Service area. Clicking the Login to Zscaler button will redirect you to the Zscaler Admin portal of the selected Zscaler cloud.Tunneling Protocol This option is available only for Zscaler cloud security service provider. Choose either IPsec or GRE as the tunneling protocol. By default, IPsec is selected. Note: If you select an automated Zscaler service provider then the Tunneling Protocol option will not be available for configuration.Hash Select the Hash function as SHA 1 or SHA 256 from the drop-down. By default, SHA 1 is selected. Encryption Select the Encryption algorithm as AES 128 or AES 256 from the drop-down. By default, None is selected. Key Exchange Protocol Select the key exchange method as IKEv1 or IKEv2. By default, IKEv2 is selected.
This option is not available for Symantec cloud security service.
Login to Zscaler Click Login to Zscaler to login to the Zscaler Admin portal of the selected Zscaler cloud. - Click Save Changes.
When you enable Cloud Security Service and configure the settings in a profile, the setting is automatically applied to the Edges that are associated with the profile. If required, you can override the configuration for a specific Edge. See Configure Cloud Security Services for Edges.
For the profiles created with cloud security service enabled and configured prior to 3.3.1 release, you can choose to redirect the traffic as follows:
- Redirect only web traffic to Cloud Security Service
- Redirect all internet bound traffic to Cloud Security Service
- Redirect traffic based on Business Policy Settings – This option is available only from release 3.3.1. If you choose this option, then the other two options are no longer available.