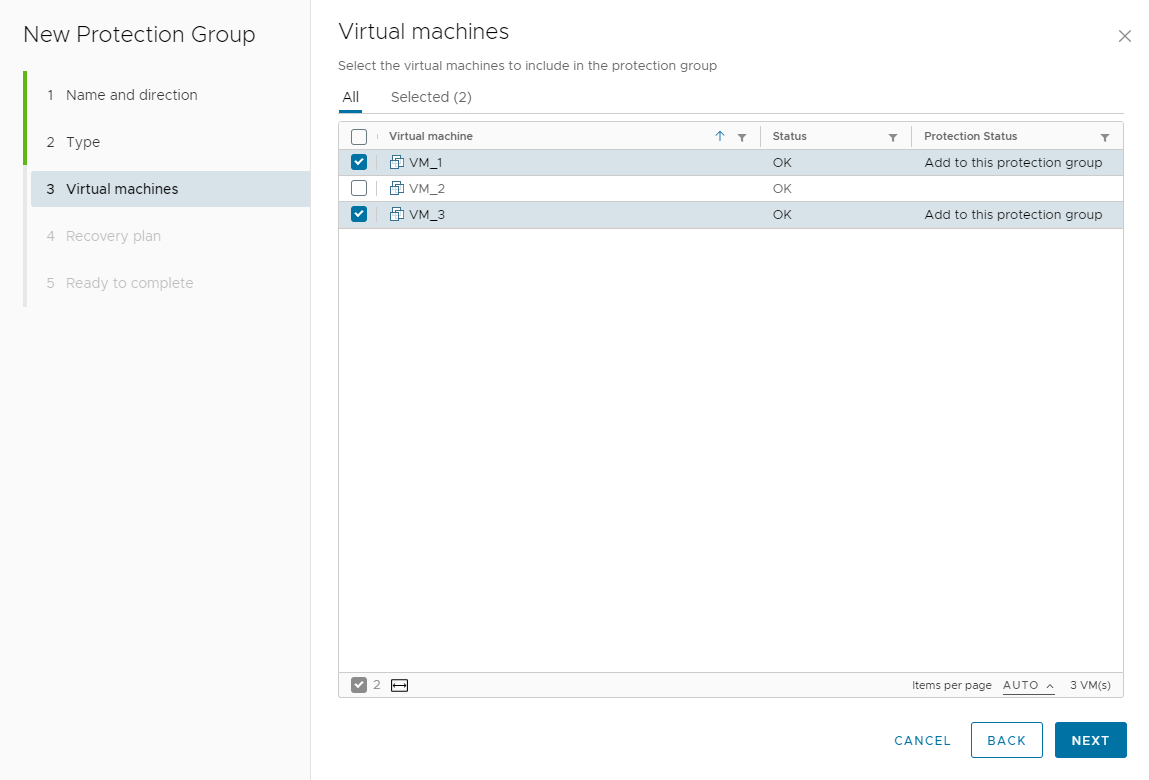
You create protection groups to enable Site Recovery Manager to protect virtual machines.
You can organize protection groups in folders. Ensure that protection group names are unique across all folders.
When you create protection groups, wait to ensure that the operations finish as expected. Make sure that Site Recovery Manager creates the protection group and that the protection of the virtual machines in the group is successful.
Prerequisites
- Verify that you have configured vSphere Replication on virtual machines
Procedure
What to do next
For vSphere Replication protection groups, if the protection status of the protection group is Not Configured, apply inventory mappings to the virtual machines:
- To apply site-wide inventory mappings, or to check that inventory mappings that you have already set are valid, see Configure Inventory Mappings. To apply these mappings to all of the virtual machines, see Apply Inventory Mappings to All Members of a Protection Group.
- To apply inventory mappings to each virtual machine in the protection group individually, see Configure Inventory Mappings for an Individual Virtual Machine in a Protection Group.